At Ignite 2019 Microsoft announced BitLocker key rotation for Intune managed Windows 10 devices. It is a long awaited feature and closes the feature gaps in the cloud managed BitLocker solution. In this article we have a look how this actually works. First of all we need to configure our devices to actually perform client-driven recovery password refresh after an OS drive recovery or unlock of a fixed data drive. The OS recovery can be done either by bootmgr or via WinRE. This automatic rotation will refresh only the recovery password which was used to unlock during BitLocker recovery. Other recovery passwords will remain unchanged. The newly generated recovery password will be securely stored in Azure AD as well. In addition to the automatic rotation, Intune got the ability to trigger a BitLocker Key rotation manually from the Intune web portal. The main difference here is, that during this process all existing recovery passwords will be deleted, and a single new recovery password will be set and a backup is written to Azure AD.
How can we configure BitLocker key rotation with Intune now?
First we have some prerequisites:
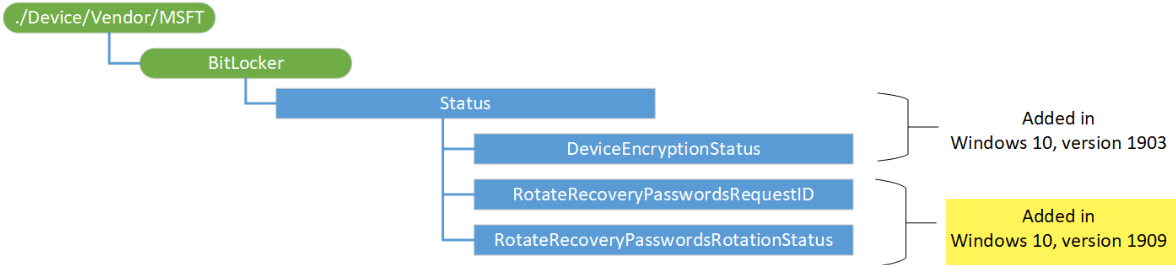
- Windows 10 Version 1909 or higher
- Azure AD joined devices
- Hybrid Azure AD joined devices
- Intune managed (MDM enrolled)
If the prerequisites are fulfilled, all we need is a Windows 10 device manged by Intune and an Endpoint protection profile to configure the BitLocker settings. In the background the BitLocker CSP is utilized to provide this functionality which was enhanced with Windows 10 Version 1909.
As said the recovery password rotation works with Azure AD joined devices and with Hybrid Azure AD joined devices.
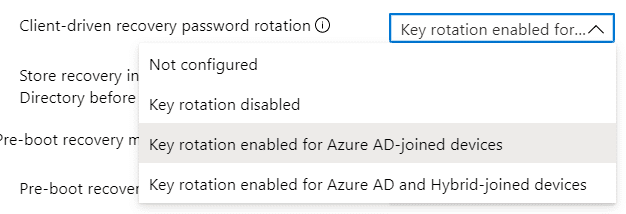
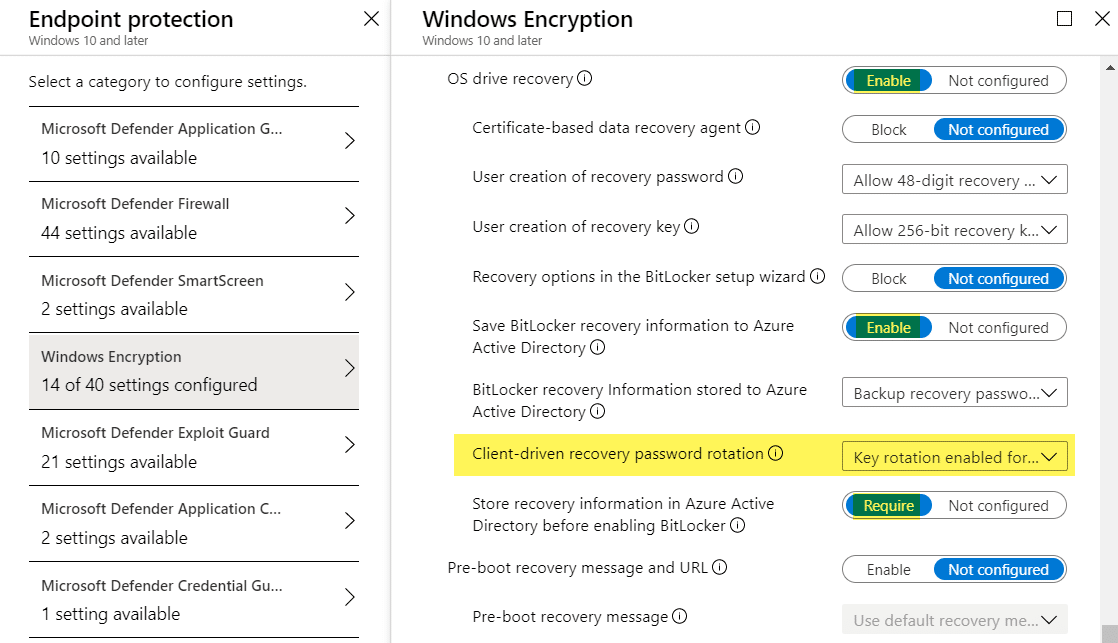
In my following example I’m using a “Key rotation enabled for Azure AD-joined devices”. Starting with the BitLocker basics first, we have to configure BitLocker settings to require encryption.
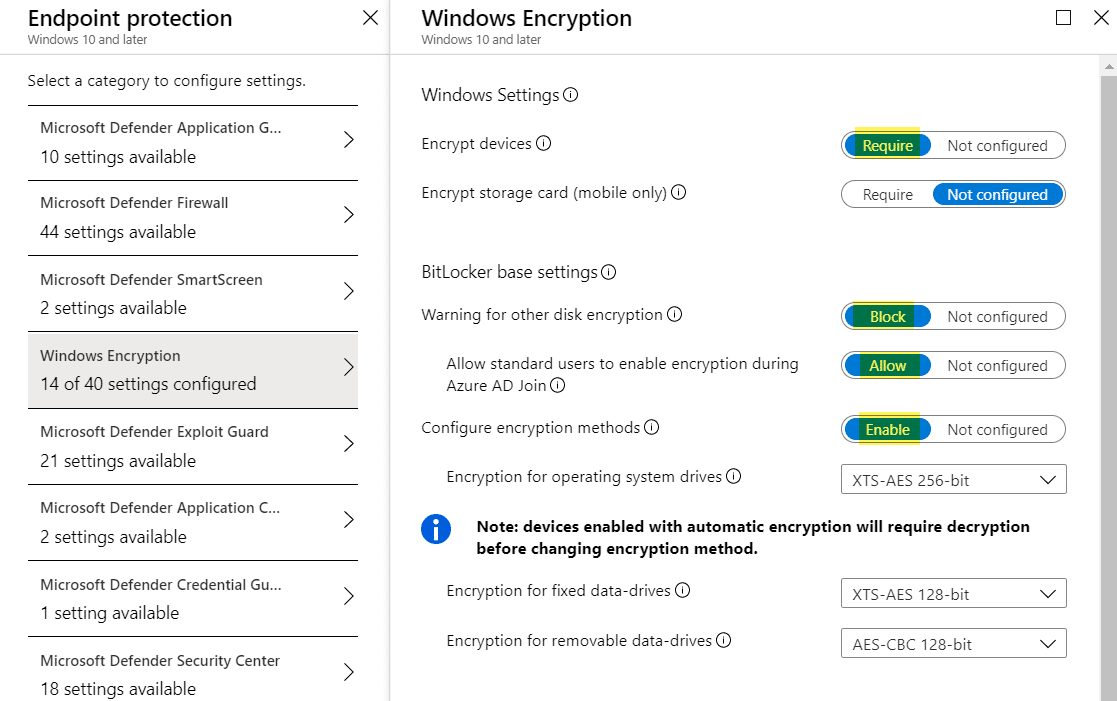
For the OS drive recovery we need to make sure the new “Client-driven recovery password rotation” is set. In my case I have chosen “Key rotation enabled for Azure AD-joined devices”.
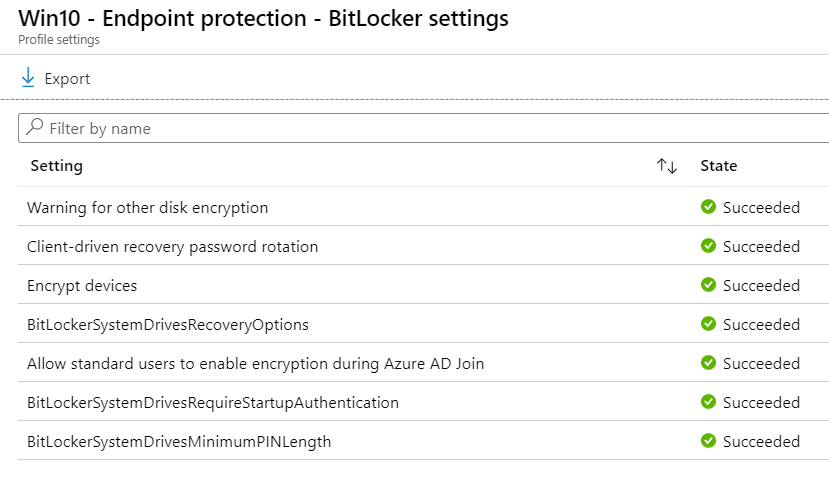
Finally we need to make sure our device is correctly configured afterwards. I’ve checked in the Intune portal if all settings are successfully applied.
How can we test the BitLocker key rotation with Intune now?
In my case I’m using a Hyper-V Virtual Machine for testing. Hereby I make sure to have the Enrollment Status Page (ESP) turned on and the Endpoint protection profile is assigned to my device. For successful silent BitLocker encryption, we have to make sure that we un-mount the Windows 10 ISO image after installation of Windows 10, otherwise BitLocker encryption will fail. I have enrolled a Windows 10 Version 1909 Virtual Machine to my Intune tenant with an enabled ESP. The final result will look like this, a BitLocker encrypted Virtual Machine according to my settings:
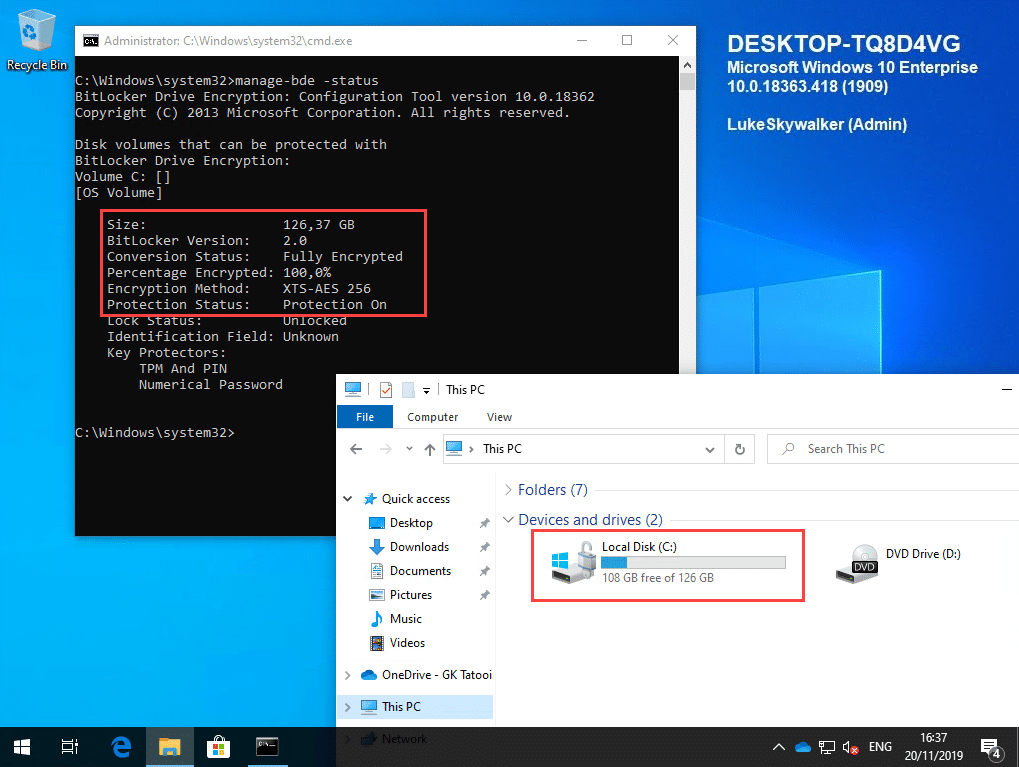
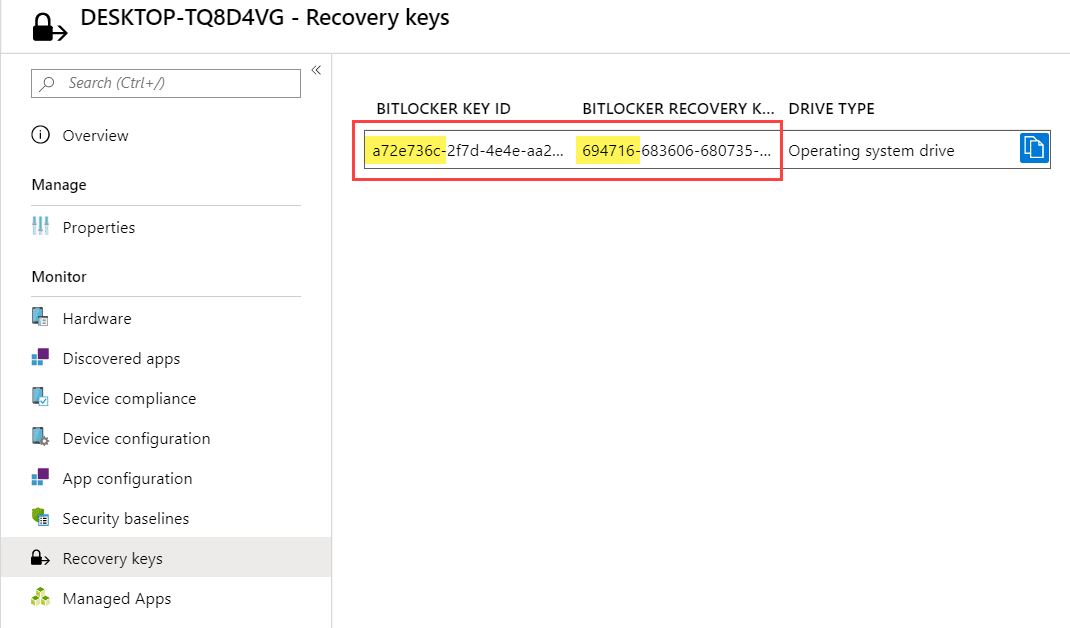
The BitLocker recovery key must be stored in Azure AD as well, according to our Endpoint protection profile settings.
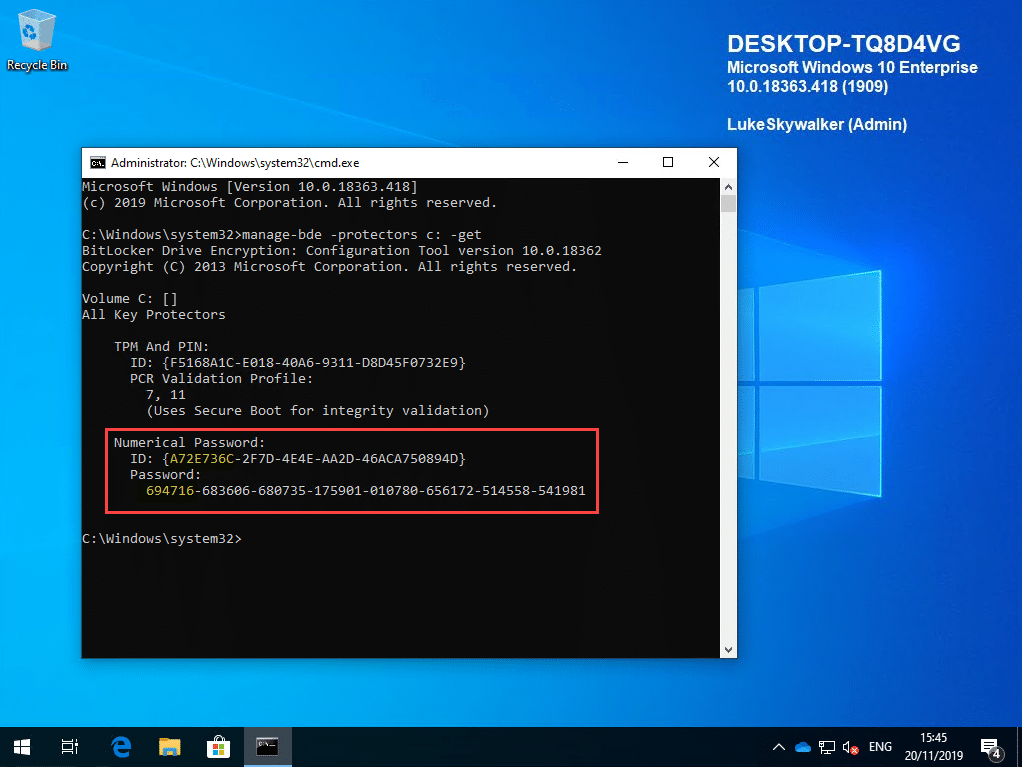
To easily test the OS drive recovery I added an additional startup PIN to the TPM via a custom package which you can find here.
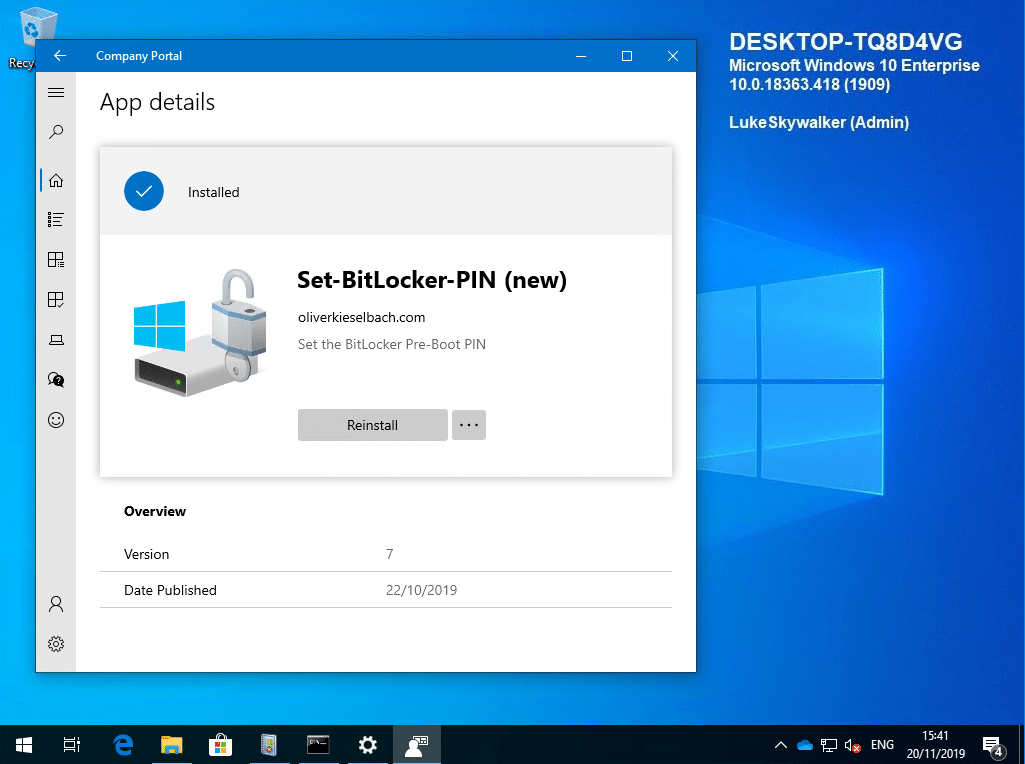
I added the PIN to have a convenient way to boot into BitLocker recovery mode. After everything is setup we can restart into the BitLocker startup PIN dialog.

Here we hit “Esc” to get into BitLocker recovery.

We enter the BitLocker recovery password and hopefully the BitLocker key rotation policy will make sure that the recovery password will be replaced with a new one now.
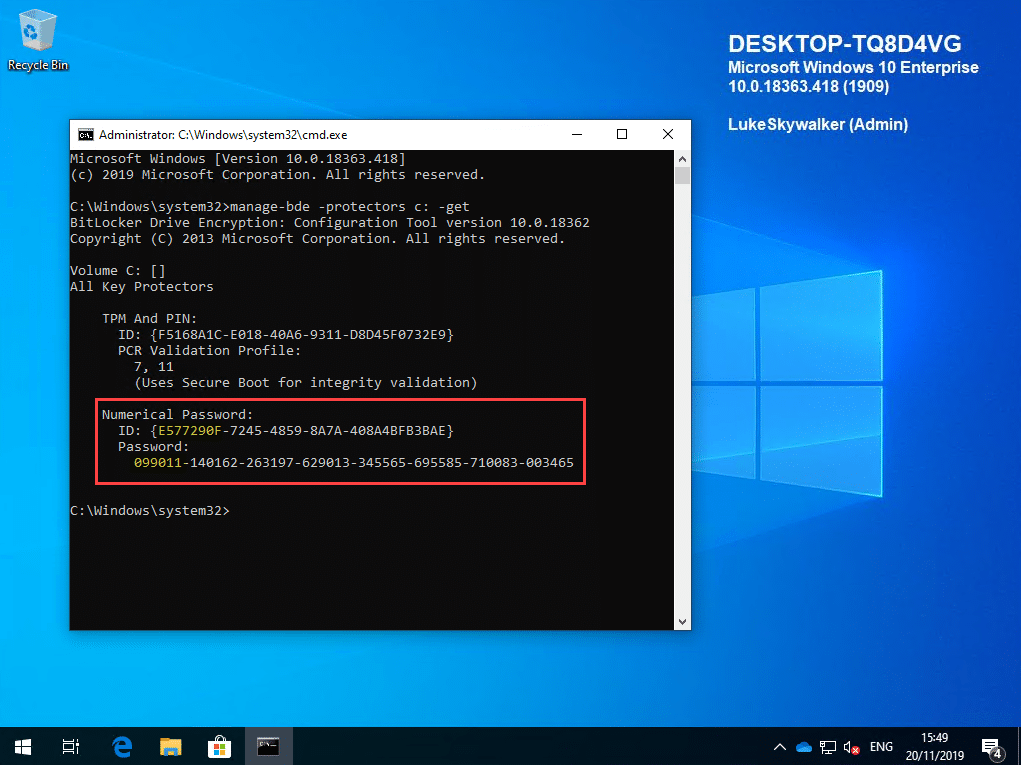
And yes as expected, the BitLocker key recovery password was changed.
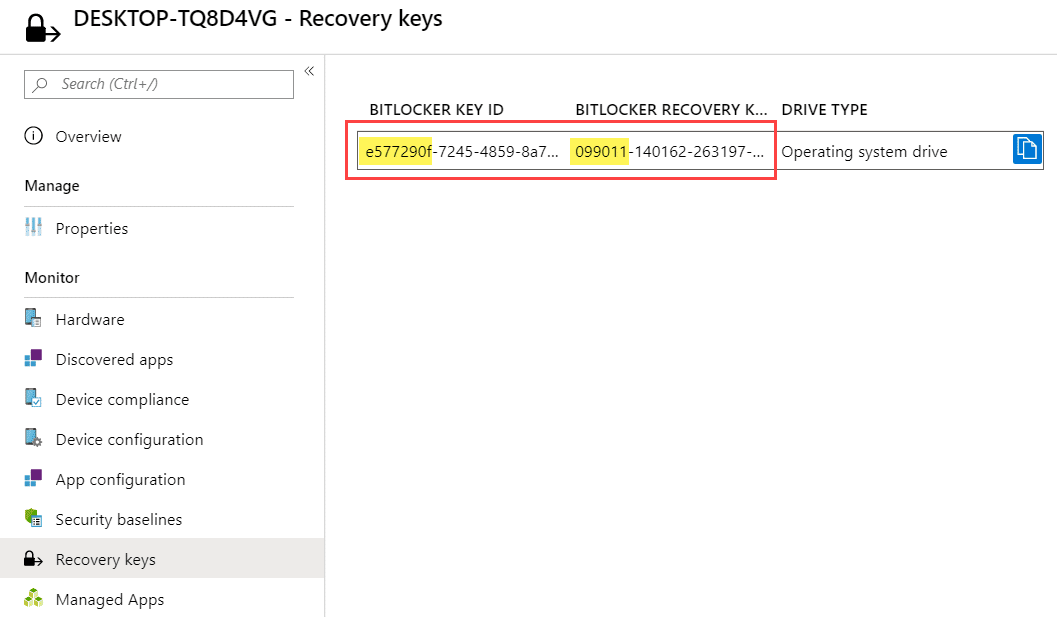
The new BitLocker key recovery password is also stored in Azure AD.
This is really great news and a welcome feature. It prevents BitLocker recovery password from re-usage and is something that has to be implemented in terms of good device security. In my opinion this is a major argument to upgrade to Windows 10 Version 1909. The Windows 10 feature upgrade 1909 is anyway a small update and you should not fear or hesitate to update your fleet. If you are on Windows 10 Version 1903 then the update is comparable to a monthly Quality Update. It is small and installs really fast like the monthly Cumulative Updates.
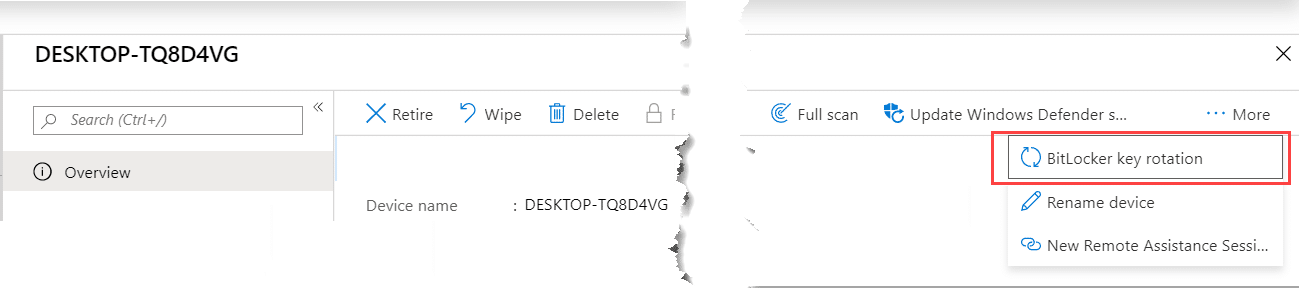
Finally we rotate the BitLocker key manually by triggering a rotation from the Intune console. We navigate to the device and click on BitLocker key rotation:
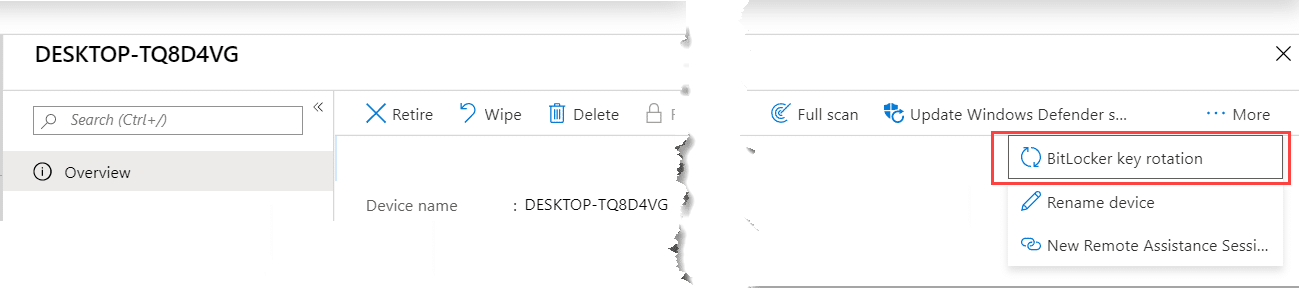
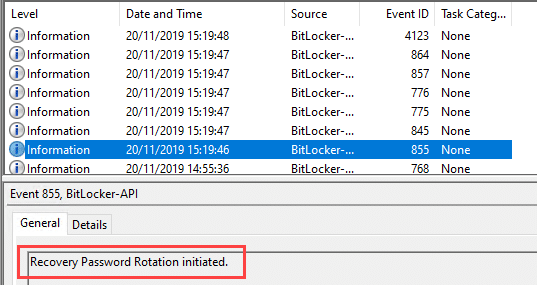
Intune will reach out to the device and trigger the BitLocker key rotation, which can be traced easily in the eventlog for BitLocker under Applications and Services Logs > Microsoft > Windows > BitLocker-API > Management
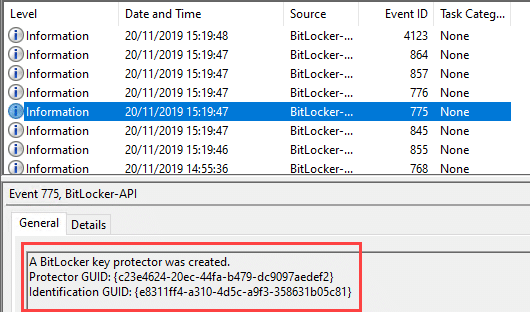
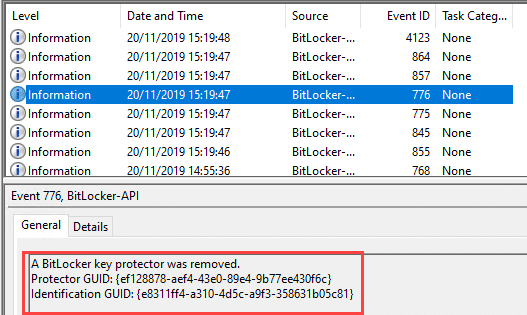
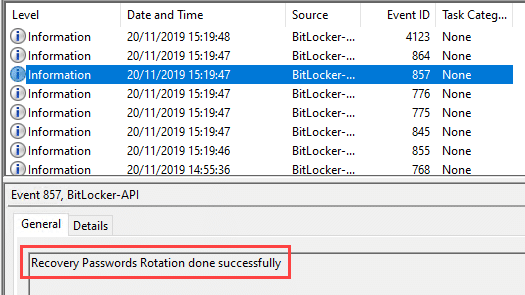
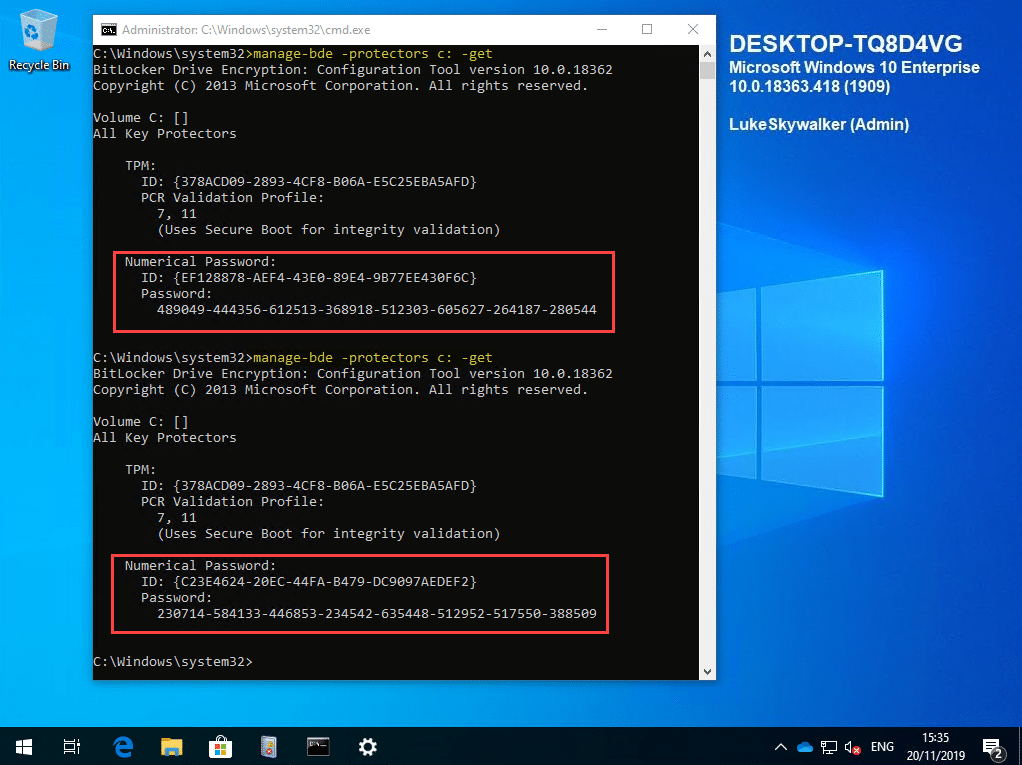
Finally, we see the new BitLocker recovery password on the device. The first entry was gathered before triggering the BitLocker key rotation from the Intune portal. The second entry is the newly generated BitLocker password.
This is a remarkable step forward in terms of BitLocker management with Intune. I can really recommend to test it out and bring your devices to Windows 10 Version 1909 to use this great feature.
If you have difficulties in getting this feature to work you might consider two things:
- Don’t forget to un-mount the ISO file if you are testing in a Virtual Machine, otherwise the encryption will not start successfully
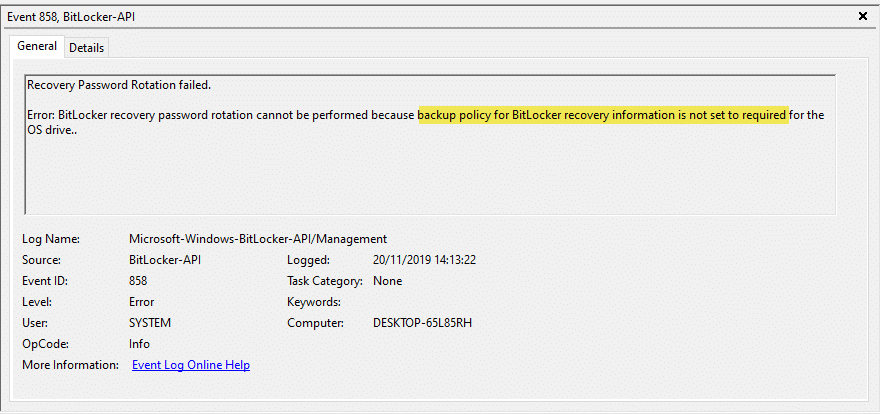
- Make sure you have the correct Intune settings like shown above. Initially I forgot to set “Save BitLocker recovery information to Azure Active Directory in my policy” which resulted in the following error:
I hope you got a good understanding of the new cloud managed BitLocker capabilities. Personally I was eager to get this feature, as a lot of security departments requested such functionality.








Add comment