When testing and implementing Windows Autopilot as your provisioning solution for Windows 10 devices, you need to import the device hash including other values into the Autopilot service. This can be done through the Intune portal by uploading a CSV file that has been gathered from the device in question or multiple devices depending on your scenario. Microsoft also provides various scripts and modules for simplifying the whole process, but in my opinion, it could be made even more simpler.
The current process from Microsoft consists of you installing a gather script that creates a CSV file for you that you’d then have to upload to Autopilot through the Intune portal. The overall process for this is described under “Device identification” in the following article from Microsoft:
https://docs.microsoft.com/en-us/windows/deployment/windows-autopilot/add-devices
Improving the import process for Autopilot devices
How could we improve this process of gathering the device details required for Autopilot and then importing it into the service? We combine the two steps into a single script that takes care of everything for us. I’ve taken the liberty of uploading such a script to the PowerShellGallery repository making it easy to get started and use. This script is named Upload-WindowsAutopilotDeviceInfo and for those that’s interested in the source code, it’s available on GitHub here:
https://github.com/MSEndpointMgr/Intune/blob/master/Autopilot/Upload-WindowsAutopilotDeviceInfo.ps1
Upload a device identity in Autopilot
Using this simplified scripted approach is pretty much straight forward.
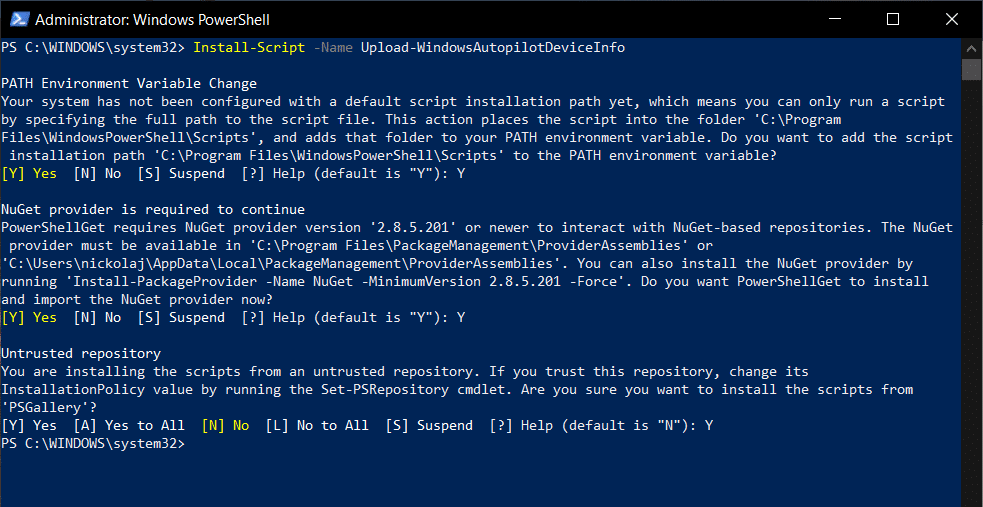
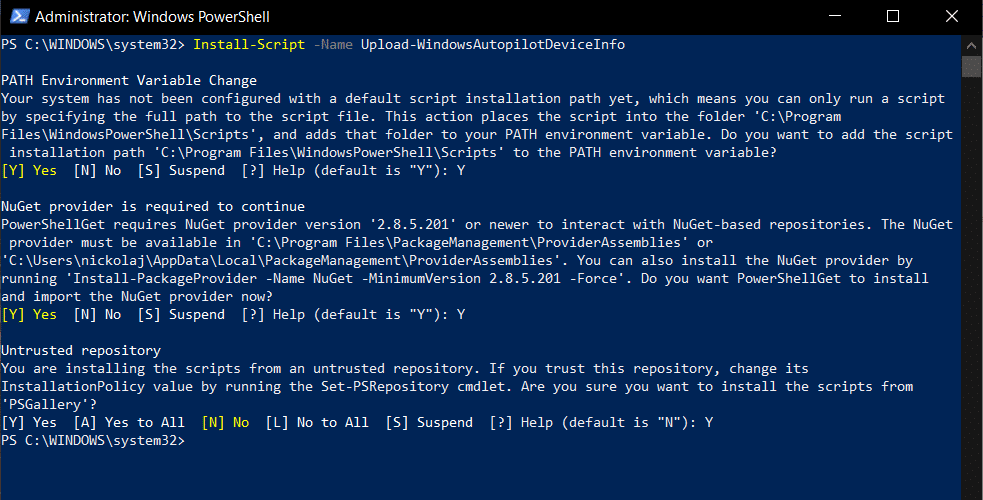
- Start by opening a PowerShell console and run the following command:
Install-Script -Name Upload-WindowsAutopilotDeviceInfo
- Answer Yes to any questions that might appear as shown in the above screenshot.
- Invoke the Upload-WindowsAutopilotDeviceInfo.ps1 script by running the following command with parameter input values:
Upload-WindowsAutopilotDeviceInfo.ps1 -TenantName "tenant.onmicrosoft.com" -OrderIdentifier "AADUserDriven" -Verbose
- The parameter input values are described below:
- TenantName: This should be tenant.onmicrosoft.com name of your tenant
- OrderIdentifier: This could be anything you like, it’s meant for easily grouping the devices and simplifies the dynamic device grouping features in Azure Active Directory
- First of all the script will prompt you to authenticate yourself, ensure you enter the credentials for an identity that’s the required permissions for uploading data into Autopilot, e.g. Intune Service Administrator or Global Administrator.
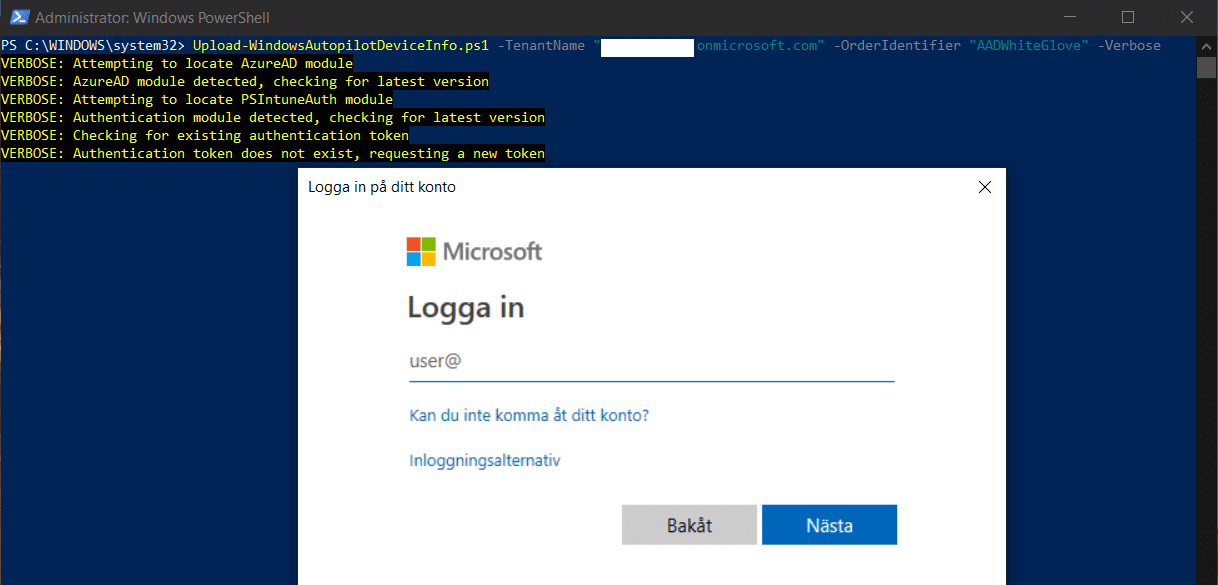 (Excuse the Swedish in the above image, although you should be familiar with the authentication prompt that appears)
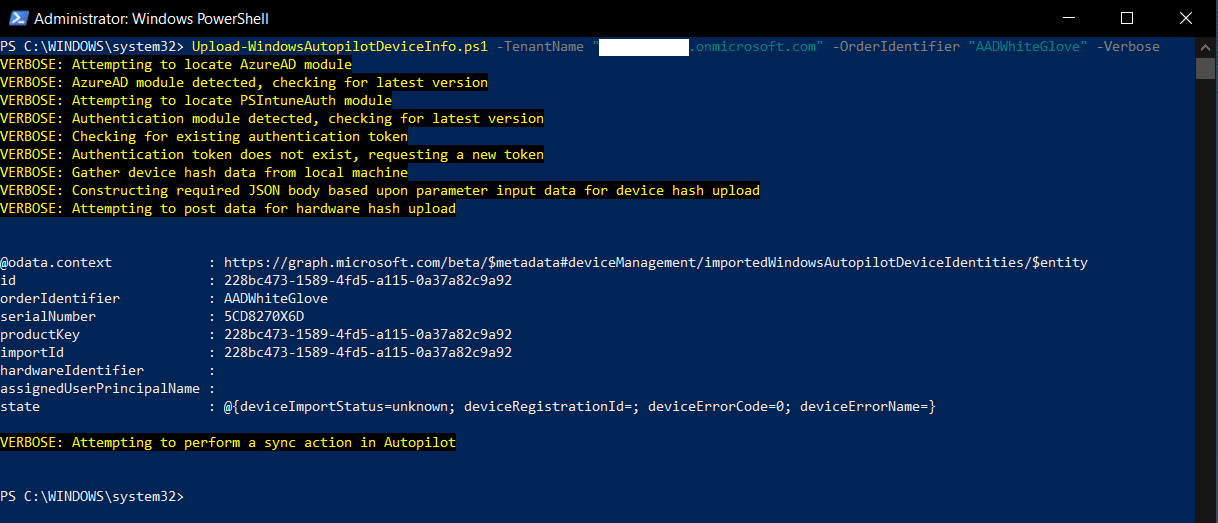
(Excuse the Swedish in the above image, although you should be familiar with the authentication prompt that appears) - After a successful authentication, the script will start the following operations:
- Device details gathering of: device hash and serial number
- Import the device identity in Autopilot using Intune Graph API
- Initiate a synchronization between Intune and Autopilot
- Once completed, the output should look similar to the following when the device has successfully been uploaded:
- In the Intune portal under Device enrollment – Windows enrollment – Windows Autopilot devices you should now see the uploaded device identity:
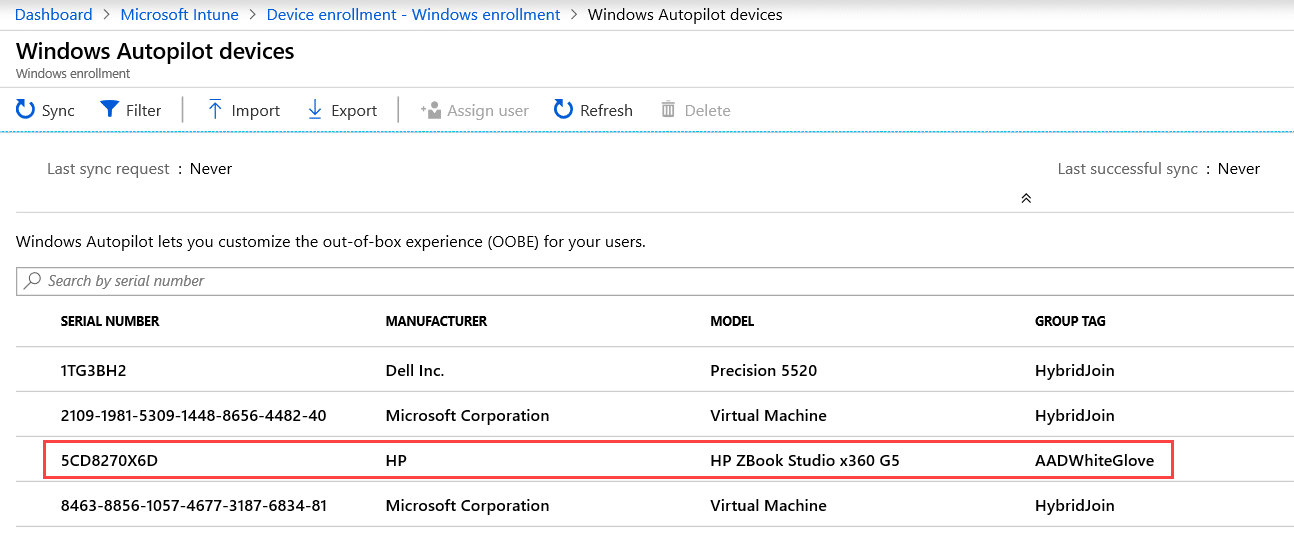
- If the device is currently not present in this blade, it could take a few minutes for it to appear.
At this point you have imported the device into Autopilot and now have to assign an Windows Autopilot deployment profile to the device. This could be made easier since we added the OrderIdentifier parameter when running the script and provided it with a value of AADUserDriven (or AADWhiteGlove as seen in some of the screenshots). With this information at hand, you could create a dynamic device group in Azure Active Directory that specifically looks for this value on the device and groups only those that meet the criteria. Below is an example query of how this could be done:
(device.devicePhysicalIds -any _ -eq "[OrderID]:AADUserDriven")
Then simply assign a deployment profile to this group and your device is now ready for provisioning using Autopilot.








Hi, It was working perfectly until about 5 days ago, are you having the same issue?
Could you see if this works any better?
https://github.com/MSEndpointMgr/Intune/blob/master/Autopilot/Upload-WindowsAutopilotDeviceInfo.ps1
Regards,
Nickolaj
Hi Nikolaj. Great article, thanks!
Typically I ask myself how to bulk assign users when I already have hundred AutoPilot devices in Intune.
An idea?
nice article, thanks!
Very awesome script! Perhaps it’s wise to change the OrderIdentifier parametername to GroupTag and [OrderID] to [Group Tag] in the dynamic query? Microsoft recommends to use Group Tag instead of OrderID since the 1905 service update in Intune.
Check https://techcommunity.microsoft.com/t5/Intune-Customer-Success/Known-Issue-with-importing-Windows-Autopilot-devices-using-Order/ba-p/624279 for more info.