If your company is evaluating Windows 10, which I assume they are, one of the new features with Windows 10 is that you can have your end users to join their off-the-shelf purchased Windows 10 PC to Azure Active Directory. With this feature, users simply just have to know their email and password to get started. For IT departments, they’re able to configure their Azure Active Directory subscription for automatic enrollment of AAD-joined devices with Microsoft Intune. To me, this capability is simply just brilliant. End-users are now able to simply just log on, get all their settings and apps and automatically be managed by the IT department.
In this post I intend to outline the steps required to setup the Azure subscription with Azure Active Directory for automatic Microsoft Intune enrollment.
Requirements
In order to enable your Azure Active Directory subscription, you’ll need to have purchased Azure Active Directory Premium licenses (or setup a trial for 30-days). As well for the premium licenses, you’ll of course also need a Microsoft Intune tenant. In order to setup a demo environment for the purpose of demonstrating this feature, I’ve performed the following steps:
- Registered a Microsoft Intune tenant by signing up for a 30-day trial
- Signed up for Azure with the tenant created for Microsoft Intune
- Added a 30-day trial of Azure Active Directory Premium
- Assigned an Azure Active Directory Premium license to my Global Administrator account (this is required to be able to configure the Microsoft Intune app through the Azure portal)
At this point, I’ve created a few test users and an All Users group in the Azure Active Directory. This group comes in handy at a later stage when we’re about to configure the Microsoft Intune application through the Azure portal.
It’s also worth mentioning that every user that’s gonna have their Azure Active Directory joined devices automatically enrolled into Microsoft Intune, needs to have an Azure Active Directory Premium license assigned.
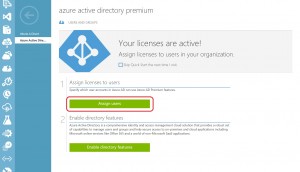
This can be managed in the Azure portal under your Azure Active Directory – Licenses – Azure Active Directory Premium. See screenshot below:
Configure Microsoft Intune application in Azure portal
Before we go ahead and configure anything in the Azure Active Directory, it’s important that you’ve set your Microsoft Intune tenant to manage your mobile devices. This can be done by following this great documentation on TechNet:
https://technet.microsoft.com/library/mt346013.aspx
In addition to configuring the MDM authority in Microsoft Intune, you’ll also need to configure a DNS CNAME on your public registrar for your domain. Follow the documentation from the TechNet below:
https://technet.microsoft.com/en-us/library/mt346003.aspx
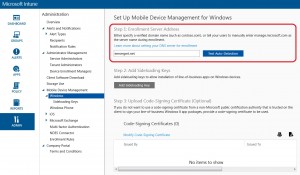
When you’ve configured your DNS correctly, you can verify it by opening the Intune Admin console, going to Admin – Mobile Device Management – Windows and enter your domain in the Test-Auto Detection field, see picture below:
When all of this is taken care of, let’s start configuring Azure Active Directory.
1. Once you’ve your Microsoft Intune tenant setup and the Azure subscription with a premium license assign for your Global Administrator account, go into your Azure Active Directory (mine is called EMS Management).
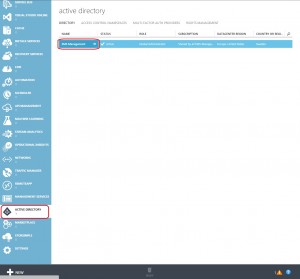
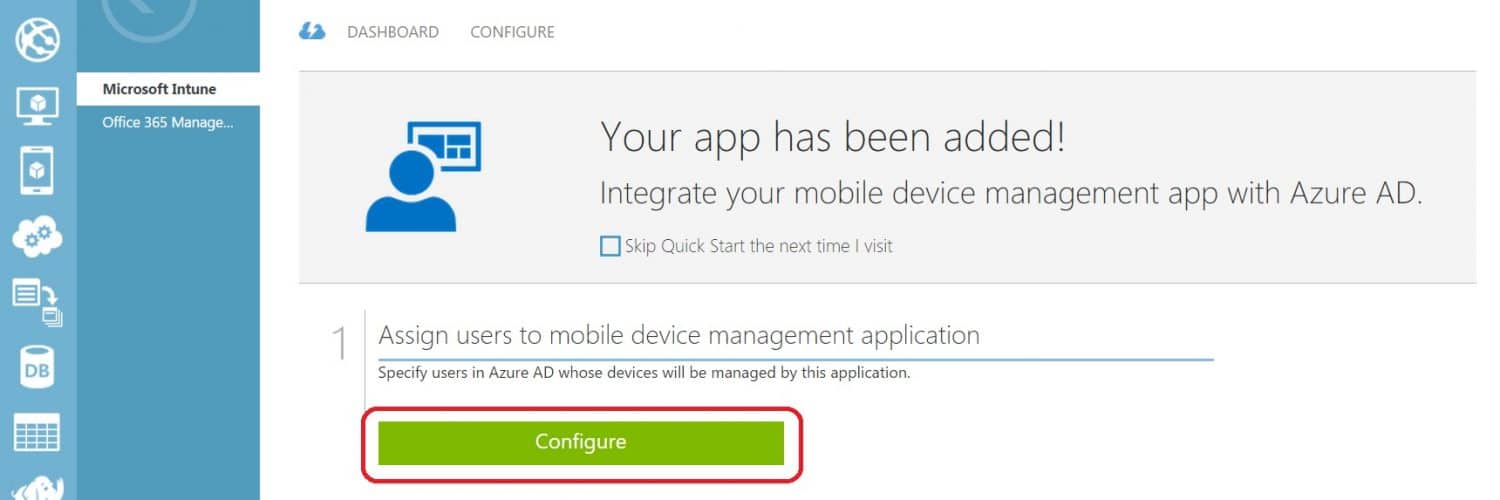
2. Click on the Applications option in the top menu, and click on Microsoft Intune.
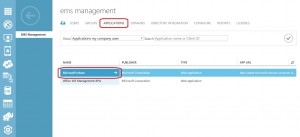
3. Click on Configure.
4. On the Properties view of the Microsoft Intune application, make sure that the following is configured:
MDM Enrollment URL: https://manage.Microsoft.com/enrollmentserver/discovery.svc
MDM Compliance URL: https://portal.manage.microsoft.com/?portalAction=Compliance
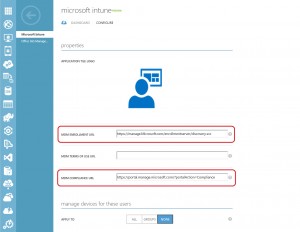
5. The group that I created earlier called All Users, this is where it comes in handy. As you’ve probably noticed, there’s a section under the URL settings where you can configure what users devices should be managed by the MDM service, which in this case is Microsoft Intune. You could easily just to get going select the ALL option, but that would mean every single user in your Azure Active Directory. You may actually want to narrow it down a bit and controlling it with some sort of group memberships. Click on GROUPS and choose Select Groups.

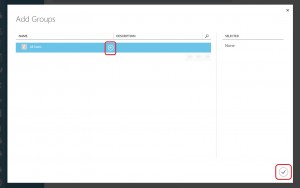
6. In the window that appears, click on the + sign next to the group of users you want to add. The group will then be shown in the right pane under the Selected view. Click the check mark button when you’re ready. Remember to save your configuration by clicking on the Save button in the middle at the bottom of the page.
Note, you can of course add several groups.
7. When you’ve configured everything, it should look similar to the following:
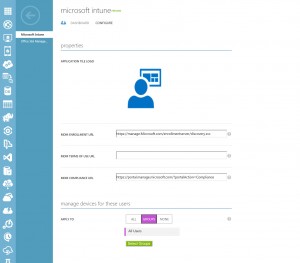
Now you’ve successfully configured the Microsoft Intune application in your Azure Active Directory to automatically enroll devices once they are joined to Azure Active Directory. It’s not really complicated at all to be honest, as you’ve seen in this post. Your users can now simply just go and buy any off-the-shelf PC they desire and in a heartbeat be compliant with company policies.
End user experience when joining Azure Active Directory
In a previous post, I’ve shown how the experience looked like in the Windows 10 Preview. Not much has changed really, so I won’t go over every step again. I will highlight the important part of the process, where the end user is simply just selecting to join his or hers new off-the-shelf PC to Azure AD in the OOBE.
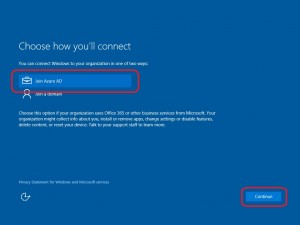
Once the user has either choose to use the express setting for privacy and other, he or she is presented with a selection of how to join this PC. When Azure AD is selected, as in the screen below:
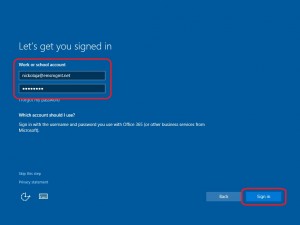
Another screen is then presented with the work account and password fields for the user to enter. Clicking Sign in results in the PC being not only joined to Azure Active Directory, with the configuration we’ve setup in this post, the PC will also be managed automatically by Microsoft Intune.
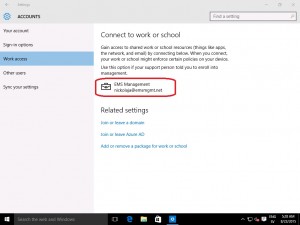
Once the user is taken to the desktop after creating a PIN, we can see in the Settings app under Accounts that the PC is indeed enrolled into Microsoft Intune:
If we would to check in the Intune Admin console under Groups – All Devices – Ungrouped Devices, we can see that the PC in fact has been enrolled into Microsoft Intune:

Pretty slick and easy! As I’ve stated before, I think this sort of mobile device management is going to increase within companies with the release of Windows 10. This cloud-optimized management solution is great for companies that are looking at getting their work force more productive right out of the box. As for organizations that are looking at Windows 10 management with ConfigMgr and EMS (Mirosoft Intune), this procedure works the exact same way, only instead the PC will end up in ConfigMgr being managed as a mobile device through the Microsoft Intune service.








how can i connect to azure ad from a windows 10 enterprise image that I have. My image is being created in sccm. Is there a step in the task sequence that i can add?
Hi Rizwan,
You can’t automate the Azure AD join during your deployment process with the tool set currently available. Hopefully in the future we’ll be able to do this, depends on how Microsoft thinks in terms of modern management etc.
Regards,
Nickolaj
Here is the issue, I AAD join a windows 10 machine. Great it shows up as a mobile managed device. You cannot do anything with it. This would be useful if you could push the Intune client down but you cannot. So what happens is you go and install the client manually and then you end up with two devices for the same machine, a computer and a mobile device both show up. Worst is when you try to go to the app store it no longer knows what device is which. You have to pick the icon with that looks like a monitor now with the same name as the icon that looks like a tablet. Me being an admin knows what all this means, but an end user …… no way man.
My recommendation is if you plan on using Intune DO NOT LET USERS Azure AD JOIN. Manually install the client and save yourself a world of headache.
Thanks for the Hint!
However I have still one question. Has Microsoft realeased an update or will there be one to fix this? I don’t want to install this manually for more than 10.000 devices… or is there an easier way to handle with it? This environment is really new for me, so if anyone has a link or something like that, please leave it as a comment below.
Thanks!
I’m getting the same issue as TellisTorillian and Adrian. You guys get any resolution?
[…] “Configure automatic Microsoft Intune enrollment of Windows 10 devices when joining Azure Acti…In this post I intend to outline the steps required to setup the Azure subscription with Azure Active Directory for automatic Microsoft Intune enrollment. […]
This works great, but it doesn’t actually push out the intune agent to allow you to manage the PC. Do you know how to automatically push out the agent?
So this works. Until another user logs in.. then the MDM enrolment breaks, and kicking off a sync results in the error TellisTorillian had above.. along with the message “system policies prevent you from connecting to a work or school account”
I really wish there was a way around this, as we want to have AzureAD joined and Intune managed devices, but we do not want all users to be local administrators, which doesn’t seem possible!
You could in theory use a service account in AAD to AAD join the devices, then have the users log on (they will now be standard users) with their AAD account.
I’m not sure how this will affect user policies set in intune though. Needs testing.
Hey,
1st off, I think you might have the only blog post on the internet where the setup process is described clearly and correctly. Thanks!
2nd… I have an issue where AAD Join works, but the MDM connection does not (device never shows up on intune). The Error when clicking info from the MDM section of Windows 10 says:
“The sync could not be initiated (0x80072f0c) ”
Have you run into this before?
Hi Tellis,
Unfortunately I’ve not encountered that error message. I’d back step everything and make sure that’s configured correctly. Are you able to enroll any devices manually?
Regards,
Nickolaj