On-boarding our macOS devices into Microsoft Defender ATP is not as straight forward as your Windows 10 machines. Today it requires not only deployment of the Defender ATP App, but also quite some settings. This post will guide you through all the steps needed to get your macOS machines into Defender ATP. I have based this post on macOS Catalina.
Fetch your on-boarding information from Microsoft Defender Security Center
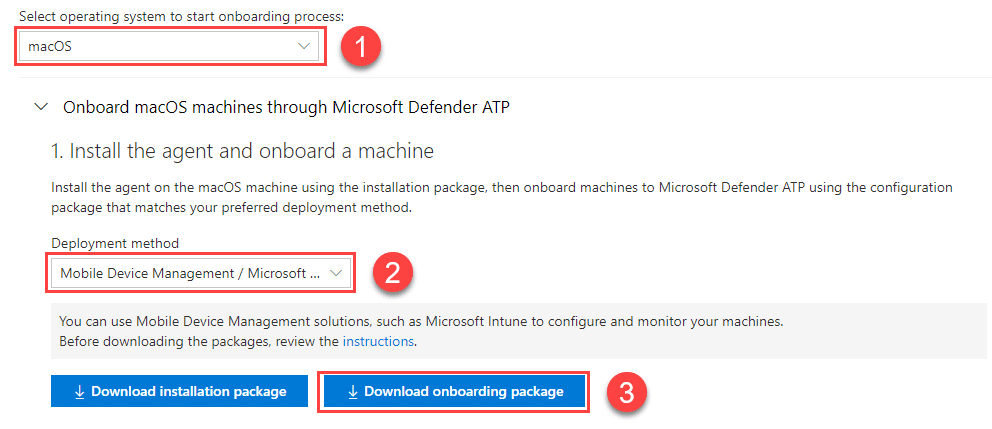
So first thing first, assuming you already have setup Defender ATP integration with Intune and have it running for your Windows machines, go into the Microsoft Defender ATP portal at https://securitycenter.windows.com and go to Settings ->Machine Management -> Onboarding
- Select macOS
- Select Mobile Device Managment / Microsoft Intune
- Download onboarding package. (We do not need the installation package)
You will now get a file called WindowsDefenderATPOnboardingPackage.zip in your Downloads folder. Unzip this in a temporary location. In this folder you find a folder for Jamf and a folder for Intune. Delete the jamf folder as we are using Intune to do this. In the Intune folder you find 2 files. We have kext.xml which is for configuring kernel extensions on your macOS devices, and the WindowsDefenderATPOnboarding.xml that contains your tenant on-boarding information. But before we go into the details of this let us have a look of what else is needed.
Required configuration for MDATP to work on macOS Catalina
To make MDATP work as we want it to we need to have some additional settings in addition to the ones in the on-boarding package. I recommend the following configurations to be deployed before deploying the Defender ATP application to our machines:
- MDATP Configuration settings
- This is where we decide how MDATP is behaving on your devices like enabling real-time protection.
- MDATP Full Access on Catalina
- On macOS Catalina we need to allow MDATP to have full access to all files on the machine with a specific configuration
- MDATP White-list
- We need to white-list Defender ATP and Autoupdate for displaying notifications in UI on macOS Catalina
- Microsoft AutoUpdate (MAU) Configuration (optional)
- To update MDATP on macOS this program is used. If you want to enforce update ring or change behavior this must be configured.
- MDATP Kernel Extensions
- This is part of the on-boarding package and is required for MDATP to work
- MDATP On boarding
- This is part of the on-boarding package and is required for MDATP to work
MDATP Configuration settings
The configuration profile is basically a XML file containing all your configuration settings for Defender ATP. I am going to
Some of the things we would like to configure is the following:
- Enable Real Time Protection
- Exclusion Merge to restrict local users from adding their own exclusions
- Disallowed threat actions
- Threat Type settings with actions to take
- Threat type settings merge policy
- Cloud-delivered protection
- User Interface
- Endpoint detection and response
I recommend you to start by downloading a recommended configuration file from docs.microsoft.com, at the same place you will also find a full configuration version. In the full configuration file you have keys and you have underlying settings. The keys is antivirusEngine, cloudService, edr and userInterface.
Antivirus Engine Settings
I have configured this with the following: 3. enable Real Time Protection, 5. disable passive mode, 15. excluded “/var/log/system.log”, 27.disabled users from creating their own exceptions, 30/31. restricted users from allowing threats or removing threats from quarantine, threat type settings set to 37.block unwanted applications and 43. audit archive_bomb and 49. not allowing users to define their own settings for threat types. My settings for this part is here:
<key>antivirusEngine</key>
<dict>
<key>enableRealTimeProtection</key>
<true/>
<key>passiveMode</key>
<false/>
<key>exclusions</key>
<array>
<dict>
<key>$type</key>
<string>excludedPath</string>
<key>isDirectory</key>
<false/>
<key>path</key>
<string>/var/log/system.log</string>
</dict>
<dict>
<key>$type</key>
<string>excludedPath</string>
<key>isDirectory</key>
<true/>
<key>path</key>
<string>/home</string>
</dict>
</array>
<key>exclusionsMergePolicy</key>
<string>admin_only</string>
<key>disallowedThreatActions</key>
<array>
<string>allow</string>
<string>restore</string>
</array>
<key>threatTypeSettings</key>
<array>
<dict>
<key>key</key>
<string>potentially_unwanted_application</string>
<key>value</key>
<string>block</string>
</dict>
<dict>
<key>key</key>
<string>archive_bomb</string>
<key>value</key>
<string>audit</string>
</dict>
</array>
<key>threatTypeSettingsMergePolicy</key>
<string>admin_only</string>
</dict>Cloud Service Settings
Under Cloud Service Settings we define how to handle cloud delivered protection, diagnostics level and automatic sample submissions. I have configured this to 3. enable Cloud delivered protection, 6. diagnostic level is set to required and 7. automatic sample submissions is enabled.
<key>cloudService</key>
<dict>
<key>enabled</key>
<true/>
<key>diagnosticLevel</key>
<string>required</string>
<key>automaticSampleSubmission</key>
<true/>
</dict>User Interface settings
The only thing we can configure here now is whether or not the status meny icon should be hidden or not. I have set this to show the icon.
<key>userInterface</key>
<dict>
<key>hideStatusMenuIcon</key>
<false/>
</dict>EDR settings
Under EDR settings you can define a group tag and enable early preview of EDR features. I have configured this to enable early preview.
<key>edr</key>
<dict>
<key>earlyPreview</key>
<true/>
</dict>This concludes the configuration of the settingsfile. I have published the complete configuration file on github . We will return back to how to deploy this settings a bit later on the blogpost.
Configure MDATP Full Access on Catalina
This one is a bit simpler to to, as Microsoft has published the config of this file for us (tcc.xml ) on docs.microsoft.com, and I have also published this in XML format for you do download on github.
MDATP White-list
The same story here, you will find the configuration file on same docs.microsoft.com page as above, and the file is available on github.
Microsoft AutoUpdate (MAU) Configuration
Even though this setting is optional, I really recommend you configure these settings. This will allow you to control what rings your machines are on and also the frequence of checking for updates. This also applies to Office Pro Plus and other Microsoft applications in addition to MDATP.
I have set the configuration in my file to 4. automatic download updates, 5. keep the check for updates button enabled, 8. Update frequence is set to 180 minutes (default is 720), 9. disabled the insider checkbox and 11. send all telemetry.
<key>ChannelName</key>
<string>Production</string>
<key>HowToCheck</key>
<string>AutomaticDownload</string>
<key>EnableCheckForUpdatesButton</key>
<true/>
<key>UpdateCheckFrequency</key>
<integer>180</integer>
<key>DisableInsiderCheckbox</key>
<true/>
<key>SendAllTelemetryEnabled</key>
<true/>The complete configuration file with payload is to be found at github
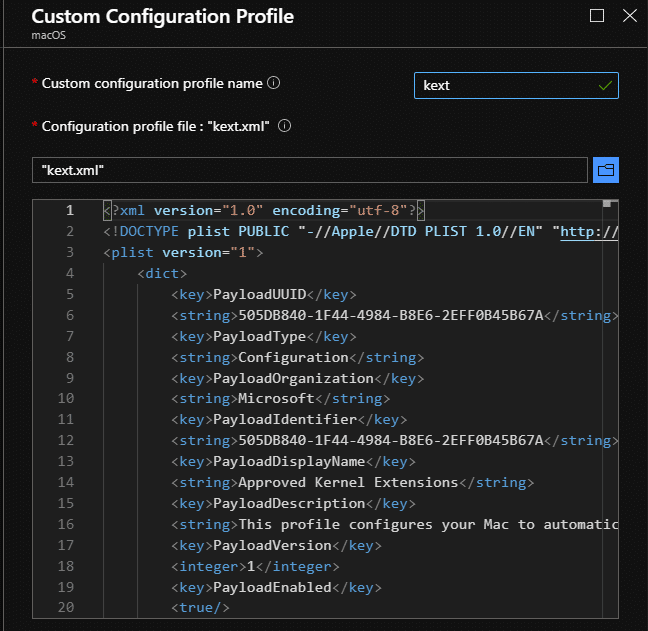
MDATP Kernel Extensions
Microsoft are preparing a Microsoft Defender ATP for macOS update that leverages system extensions instead of kernel extensions. In the meantime Apple will give a user facing “Legacy System Extension” warning. If you deploy this Kernel extension to your machines BEFORE you deploy the MDATP application, users will not get this warning.
The configuration file for this is found in your on-boarding package that we downloaded and is called kext.xml
MDATP On boarding
The configuration file for this is found in your on-boarding package that we downloaded and is called WindowsDefenderATPOnboarding.xml
Deploying the Configurations via Intune
Now that we have created all the configurations we should have a total of 6 configuration files in our temporary folder. My files has these names:
To deploy these settings we go into Intune Device management portal at https://endpoint.microsoft.com and go to Devices -> macOS -> Configuration Profiles and create a new profile.
Give a name that corresponds to the settings you are deploying, choose macOS as platform and select Profile type Custom. Here you will have the option to upload your xml files that we have now created or downloaded.
Give the profile the correct name and choose your file, the result should look like this:
Now we need to repeat this for all 6 of our files with the following information:
| Recommended Profile Name | Platform and Type | Custom configuration profile name | File |
| MACOS MDATP Configuration | macOS – Custom | mdatpconfiguration | mdatpconfiguration.xml |
| MACOS MAU Configuration | macOS – Custom | com.microsoft.autoupdate2 | com.microsoft.autoupdate2.xml |
| MACOS MDATP Full Access | macOS – Custom | tcc | tcc.xml |
| MACOS MDATP Kernel Extensions | macOS – Custom | mdav-kext | kext.xml |
| MACOS MDATP Onboarding | macOS – Custom | mdatponboarding | WindowsDefenderATPOnboarding.xml |
| MACOS MDATP Whitelist Defender and MAU | macOS – Custom | whitelist | whitelist.xml |
I recommend using a dynamic group for all macOS devices for targeting and assign this configurations to the device group. You could also assign this to All Users and All Devices if you don’t want to target a dynamic device group. If you choose to use a dynamic device group for this, the query I use is this: (device.deviceOSType -contains “Mac”)
Now the final result should look like this:
After this you can verify the settings are applied to your macOS device by checking System Preferences -> Profiles. This is how the mdav.kext profile should look:
Also we can verify that Microsoft Autoupdate has been configured correctly now. Open up Microsoft AutoUpdate and click on Advanced to verify your settings that should look like this:
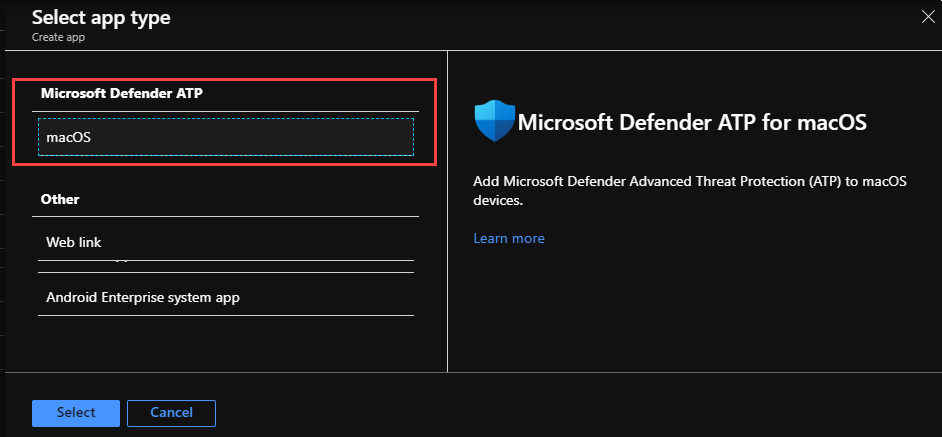
Deploy the Microsoft Defender ATP Application to your devices
Now we are ready to actually deploy MDATP to our devices. The application will not work as expected or get on-boarded if this is done before the above steps are done.
Go to https://endpoint.microsoft.com, select Apps -> All Apps -> Add, Select app type Microsoft Defender ATP / macOS
You get to the App configuration blade. Click Next -> Add Scope tag if you use it -> Assign the app to your dynamic device group as required -> Review and create – Click Create. Now just sit back and wait to see that the application gets installed to our macOS device.
Verify and Test
To verify you are onboarded correctly and that MDATP is working as expected, there are a few things you can do.
- Verify the application is installed and that the status icon is green
- Open Defender ATP and verify your settings

- Check that the device is listed in the machine list in Microsoft Defender Security Center

- Perform a test detection on the device with eicar test file.
- Open a terminal window on your macOS device
- Copy and run the command curl -o ~/Downloads/eicar.com.txt http://www.eicar.org/download/eicar.com.txt
- Defender on your machine will report almost instantly and you should get an alert in the Microsoft Defender Security Center within a few minutes















Hey,
There is a big confusion here, now the Microsoft article says it does not recommend running any third party antivirus solution along with MDATP, now the question is would MDATP be a complete replacement of our Symantec Endpoint protection solution for Mac OS ?
Would be great if you could highlight details on it
It is a full replacement yes. But I am not going to go into a comparison of these two products.