For earlier posts, please find them here:
In the last part of this blog post I wrote about the beginning of my passwordless journey and which keys I had available.
In this second part I will conclude with the overall experiences that I had with security keys from the vendors that I have had a chance to test with.
A few new keys, that I have been sent from various vendors will get added in a third part within a few weeks.
The experiences with each key
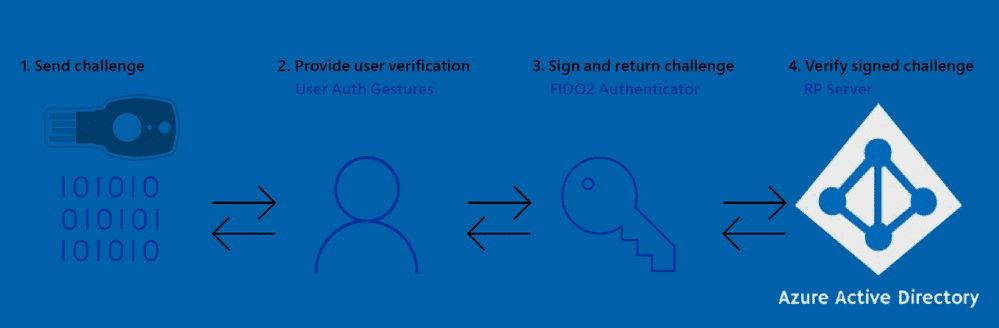
Generally the whole process of adding a security key through aka.ms/MFASetup is rather easy, but there are some bumps and I did get some scratches!
A fact that is true for each key is: The key only needs to be inserted at time of authentication, so don’t just leave it in there all day.
The keys experiences are listed in no specific order.
Solokeys Solo Tap USB-A (NFC)
This key might be good for Google or Facebook use, but it was not a pleasant experience for Azure AD use.
Unfortunately, the pre-loaded firmware did not allow me to add it to Azure AD.
And even after going through a less than pleasant firmware update process via update.solokeys.com, getting prompts every second like this gif shows.
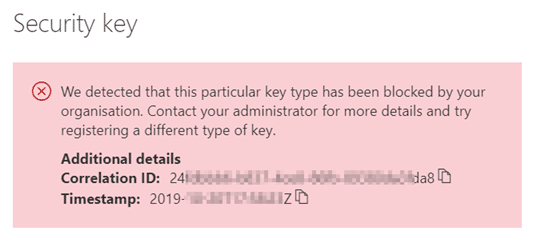
The “mysignins” page told me that this specific key was blocked by my organisation when I tried to add it.
This was sort of a conflicting message from my point of view, because I know that we had not blocked it, but it turns out that the organisation mentioned in this case is Microsoft, and not my tenant.
So, in the end, I never managed to use this key for real, but it was fun trying to fit the red silicone cover over the “naked” key when it arrived (no, not really).
And this was even the most expensive of the keys, since I had to pay double the price because of import taxes.
Fortunately I have read that Solokeys plan on addressing all of the issues, it’s just not the right key for an enterprise to go completely passwordless with right now.
And in all fairness, it really isn’t marketed as an enterprise token for passwordless use, but I gave it a go because of the Open Source part of it appealed to me, and the fact that they state it can be used for login to Windows, which I did not get to work, and have heard the same from others.
The moral of this experience was “Go with an approved vendor”, don’t just use any FIDO2 Security Key.
Now, on to some of the approved vendors…
Yubico keys
Unboxing these was a nice experience, and they are very easy to get started with.
Overall the build quality is nice, and I had no trouble registering the keys with Azure AD.
The built-in Security Key Manager in Windows works nicely with this key.
But because is can do a lot of other auth types, most people will probably end up using the YubiKey Manager, which you can get from the Yubico website.
Side note: The YubiKey Manager is a 250MB install and has over 3500 files in it, which you need to keep in mind if you thought that it was just a quick deploy to all your users laptops. This is just my personal opinion, but I think it could be more compact for what it is.
Sign-in to Windows works as expected with this key, but as it has no biometrics, you will need to enter a personal PIN on each login, which is not really a fast experience, compared with the biometric keys that don’t have this requirement. So anyone wanting to make things smoother for the users might want to keep these extra steps in mind when comparing.
Yubico has recently announce the release of a biometrics enable key, so things are looking up, if you want to go with Yubico as your main key provider (keep in mind that you can have a mix of security keys, they are not exclusive).
One thing I really like about the Yubikey with regards to moving to a passwordless future, is the fact that you can add a static password to the key, using the YubiKey Manager.
Adding a static password means that they key will actually type a specified password whenever you long press the touch sensor on the key.
And I do mean “long press”, don’t just tap it, because that will write out the keys ID.
This is possible because the Yubikey registers itself as a HID keyboard in your system, and thus enables it to type in the static password in any legacy application that you where unable to add Single Sign On to.
Essentially this enables you to go passwordless faster, by skipping the trouble of enabling SSO on legacy applications, and just change to the static password of the security key. But you will have an added overhead of administering these static passwords or educating your users properly to manage this themselves as the password will get lost if the key gets lost.
I tried using the static password for some of my Cisco AnyConnect VPN connections to customers sites, but alas, Cisco did not support my 32 char crazy complex password, which was a bummer. I had to cut it down to 16 chars, which is still good, but not awesome.
If using the same user name on several services along with the static password, you could be in trouble if one service is compromised, so I suggest keeping it strictly for internal legacy applications.
Overall I have been happy using the Yubikeys but the lack of biometrics have kept me from using them more regularly.
I know I have not really touched upon all the other cool features of the Yubikey, but remember this is only about access to Azure AD and legacy systems on-prem. I am sure a quick search on Bing/Google will yield you a world of reviews.
eWBM keys
The eWBM keys come in a nice reusable box, which I quite like – because having a bunch of keys lying around, is easier if they come in reusable packaging.
The keys seem very robust, and the hard black casing would probably allow you to have it as a part of your regular key-chain without worrying about breakage (thought I am sure someone will prove me wrong on this).
Like with the Yubikey, the start is smooth, and there was no need to do any kind of firmware upgrade, and no software needs to be installed at all. I simply configured the key with the built’in utility in Windows 10, and then added it to my authentication mechanisms on the https://mysignings.microsoft.com portal.
Thought there is a key manager application called BioManager, I found no real use for it in my daily routines.
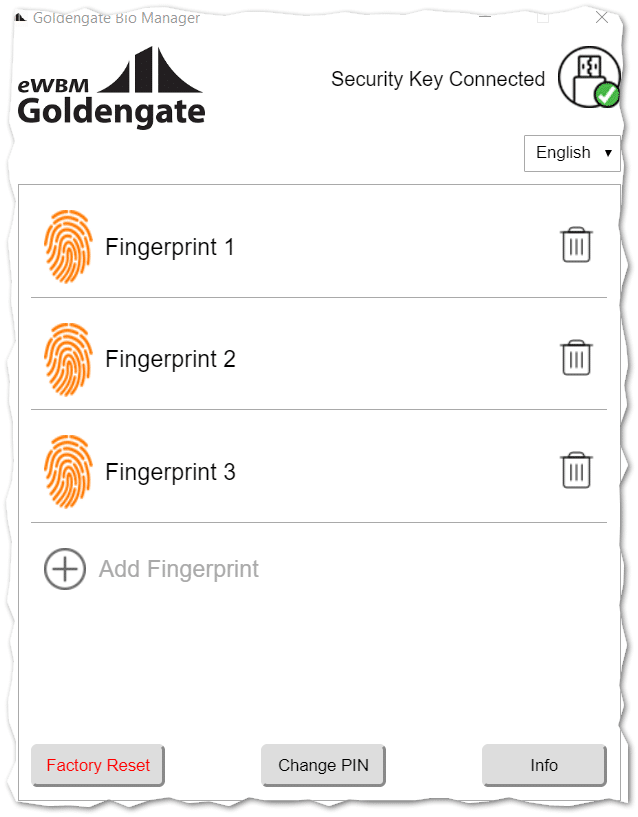
The software allows you to manage the fingerprints and factory reset the key, but there is no way to know which fingerprint is which, so you have to devise a system on your own.
The two eWBM keys are fitted with a super fast bio-metric finger print reader, that I quickly came to love, because it’s just so much smoother having to only insert the key and touch it, instead of having to type a PIN and then do a touch gesture on the key.
Normally I am not a fan of fingerprint reader on laptops, but this one is far superior to any that I have previously tried.
And with daily use, speed becomes a very important factor for almost any type of user.
With my most common use case being login to the Azure and Office 365 portal from a device that I don’t personally own, it’s nice that I don’t have to worry about shoulder surfers and theft of my key.
This key does not boast any other notable features that being a straight up FIDO2 key that did not succumb to feature creep.
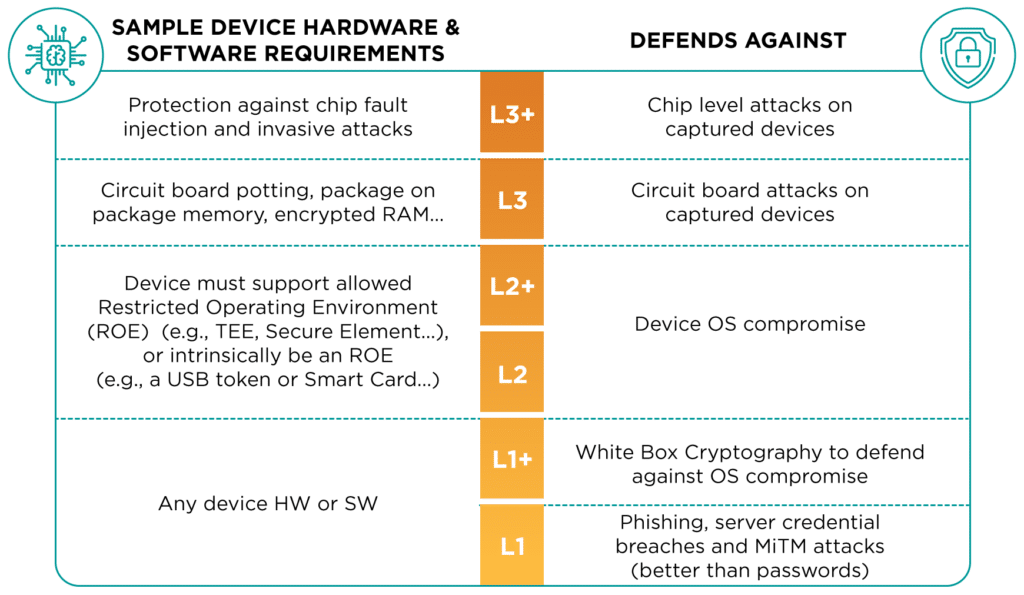
And this is something I found quite positive, because it says to me that this company is very serious about this one thing, and their FIDO2 certificate level also proves this, as they have managed to get Level2 certified, which is probably the best level we can get our hands on now. as FIDO2 levels 3 and 3+ are probably very hard to achieve, just take a look at this requirement chart:
The end of part 2
So just to be clear – this is not a review of products or services, but basically one guys opinion out the use of some random FIDO2 security keys, and his experience as an admin and user of the keys on a daily basis.
And to be honest, I will probably prefer using Windows Hello for Business as my primary OS sign-in mechanism, as long as Face ID compatible hardware is available.
But I see great security benefits in having a company policy of only using security keys when connecting from any other device than the one you have personally been assigned.
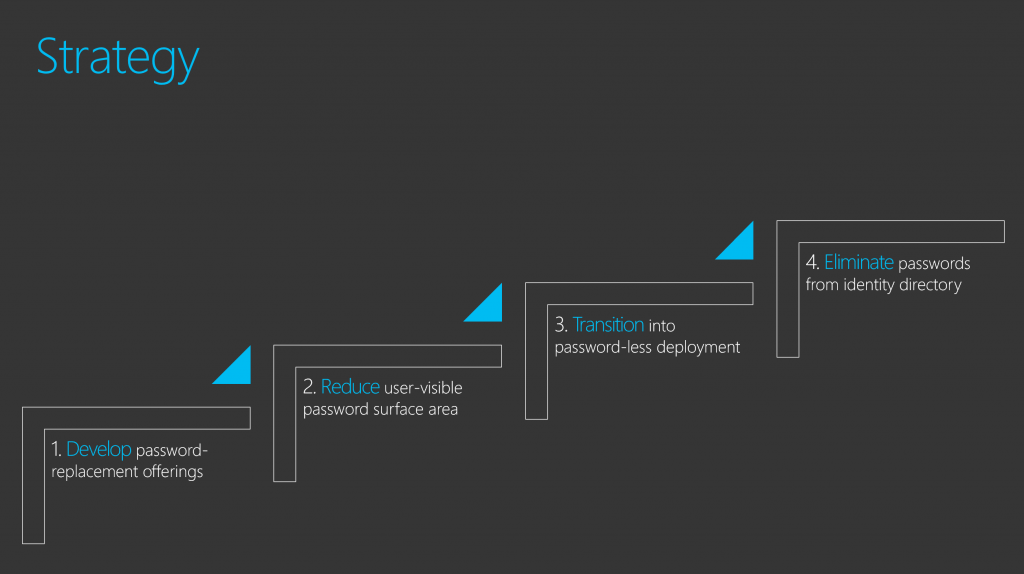
If you are embarking on a serious passwordless journey, I recommend reading the passwordless strategy from Microsoft (which they are using themselves).
Since starting on this article series, I have come into possession of two additional security keys from Feitan (K27) and OnlyKey .
Both keys seem very interesting, and I am excited to see if they can add some value to my decision process when suggesting keys to use in PoC’s for my customers.
Please don’t hesitate to follow and reach out on Twitter if you have experiences to share with me and others, or are curious about anything Enterprise Mobility and Security related.








Is there a possibility to require the fido key to be inserted? We can still login with only pin if we select the pin provider on login screen.
Are you perhaps mixing Windows Hello For Business with Security Key login?
Login with the security key will require the key to be inserted when typing the pin, as the pin resides on the key, not your computer.
If you have the same key for Windows Hello for Business, that might cause confusion.
I use static password as Bitlocker unlock password with Yubikey 4 to my Desktop PC which doesn’t have TPM chip installed. Works quite fine although restarts are funky. I still wish I bought mobo with TPM built in instead 😉
That’s a fun use of a Yubikey 🙂
Though I would also have spent the few extra dollars on a TPM capable motherboard.