In this, the final part of this four-part series, we will look at how to validate MBAM is escrowing keys, they are retrievable through different methods.
Part 1: Installation of MBAM components
Part 2: Validating IIS sites and customisation
Part 3: Configuration of GPO policies and client agent deployment
Part 4: Validation of key storage and recovery tests
Escrow recovery details
In order to successfully escrow the recovery key through to the MBAM database you will need to do one of two things depending on your roll-out of MBAM. You will of course need your clients also prepared for BitLocker, including ensuring that a TPM chip is available, cleared and activated, with the preferred BIOS mode being UEFI using Secure Boot. These pre-requisite steps can be automated where the computer manufacturer provides methods to update BIOS settings, either through applications or WMI methods.
Post OSD Deployment
With the pre-requisite hardware preparation completed, for those machines already in production it is a matter of pushing out the GPO and following up with the MBAM Client application. Once the application services start running, the policies can be applied to the machine and encryption started.
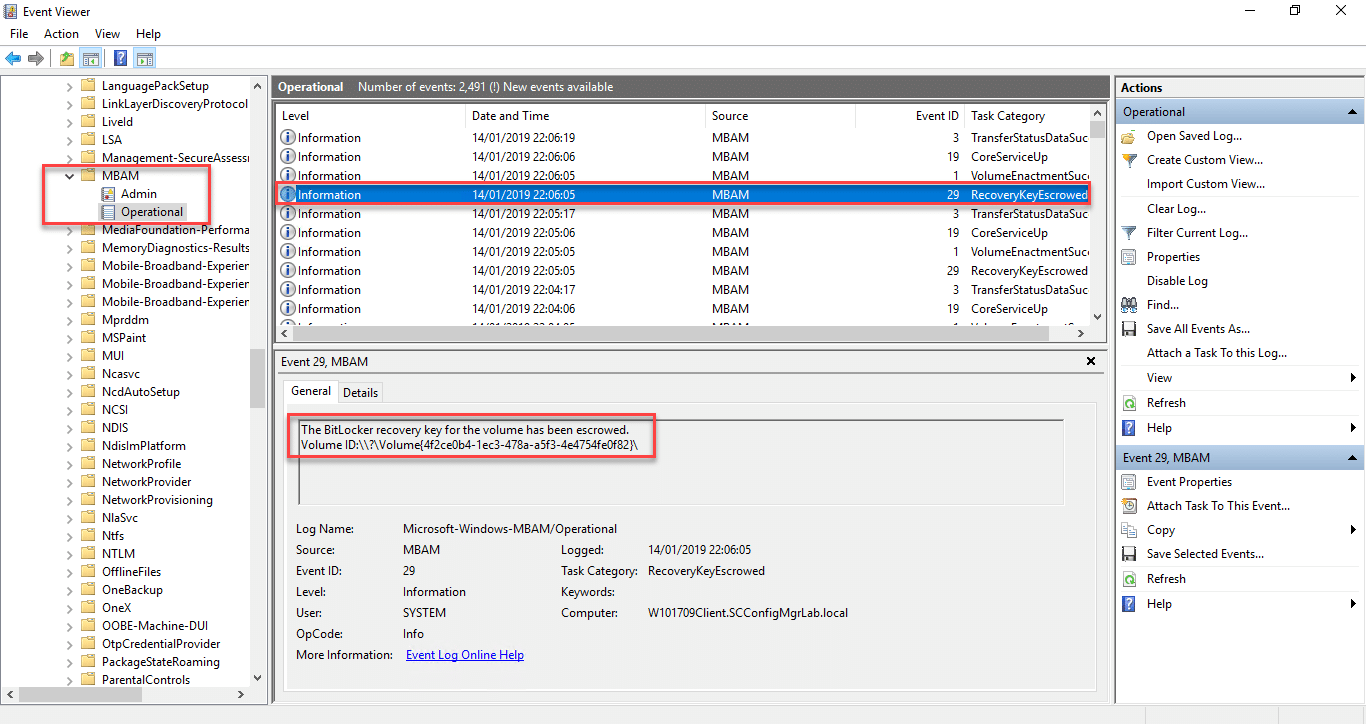
The MBAM service provides event logs so you can see what is taking place, these are located in the following location – Application and Services Logs\Microsoft\Windows\MBAM. In the below example you can see an entry showing that the key was escrowed as part of a recovery event;
Bare Metal Deployments
For those machines running bare metal deployments, you will need special consideration for initialising the BitLocker encryption process. Microsoft have a documented article on how to add the deployment scripts, along with links on the following URL – https://docs.microsoft.com/en-us/microsoft-desktop-optimization-pack/mbam-v25/how-to-enable-bitlocker-by-using-mbam-as-part-of-a-windows-deploymentmbam-25.
Testing this method is simple, all it requires you to do of course is pause your OS task sequence in the Operating System phase of the deployment and launch a PowerShell window to test the full PowerShell command. Below is an example of this;
Invoke-MbamClientDeployment.ps1 -RecoveryServiceEndpoint “https://lab-mbam.scconfigmgrlab.local/MBAMRecoveryAndHardwareService/CoreService.svc” -StatusReportingServiceEndpoint “https://lab-mbam.scconfigmgrlab.local/MBAMComplianceStatusService/StatusReportingService.svc” -EncryptionMethod “UNSPECIFIED” -EncryptAndEscrowDataVolumes
Database Key Storage & Validation
SQL Database
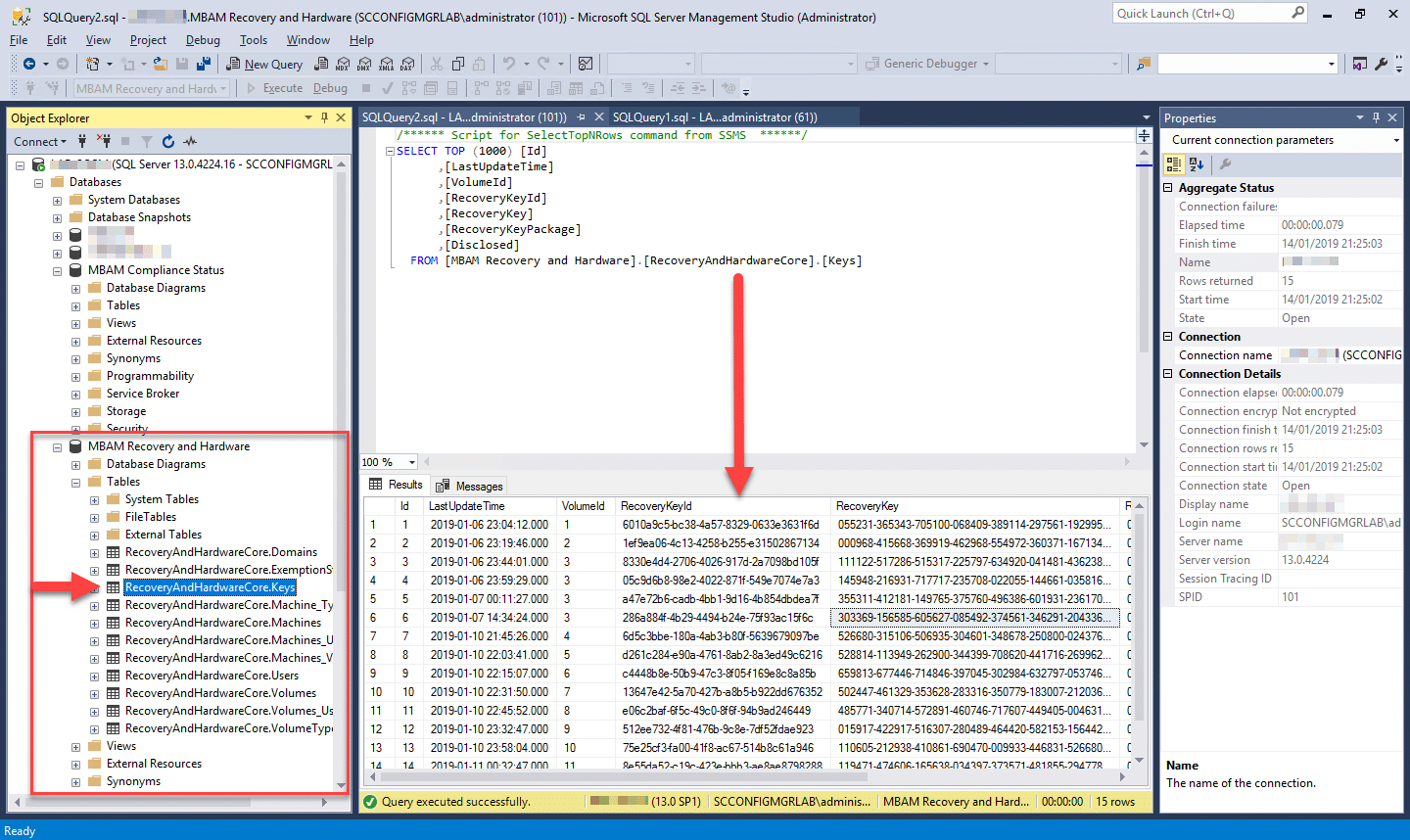
For those with access to the SQL server database you can of course use SQL management studio to review recovery information. All BitLocker key information is stored in clear text in the RecoveryAndHardwareCores.Keys table in the MBAM Recovery and Hardware database;
Should you wish to validate that the key on your machine is being stored within the MBAM database it is a simple process on the client.
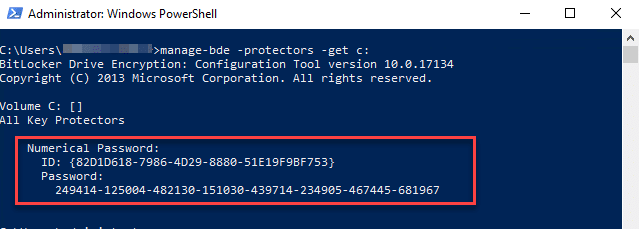
- Open an administrative Command Prompt or PowerShell Window on your client machine
- Type in the following; manage-bde -protectors -get c:
- You should now be presented with a screen similar to the one below;
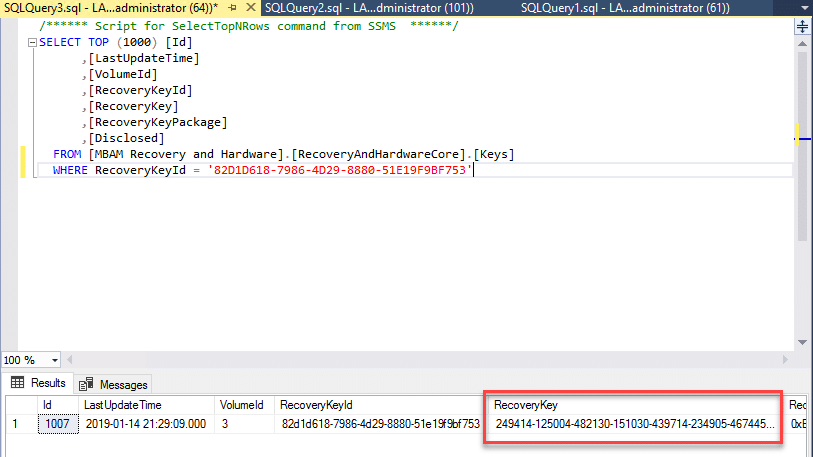
- Running a query in SQL with the ID and you should return the same recovery password;
Active Directory
Active directory in this example is also storing recovery keys as per the group policy settings being applied. Viewing the recovery information requires that the BitLocker Drive Encryption Administration Utilities are installed. Installation can be done either through the Add Roles and Features Wizard or via Powershell, through running the following command;
Install-WindowsFeature BitLocker –IncludeAllSubFeature -IncludeManagementTools
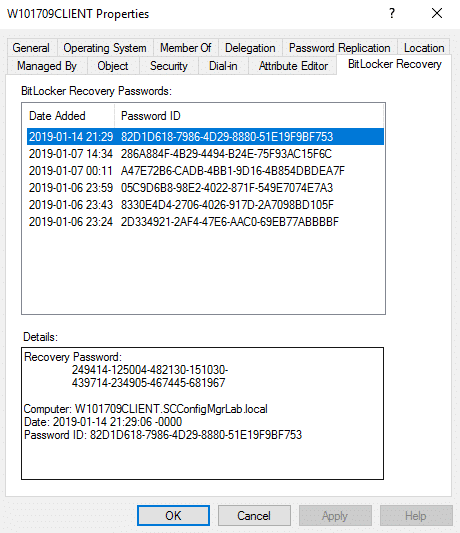
Once installed, opening the properties of the computer object and clicking on the BitLocker Recovery tab will display all associated recovery keys;
Entering the recovery key obtained either directly from the SQL database or Active Directory should of course work providing the Key ID is in place, however this will provide no auditing of this recovery action.
Recovery of the recovery key when using either the Self Service or Helpdesk (pictured below) will drive accountability of the action through audit reports, this is the preferred method when MBAM is in place.
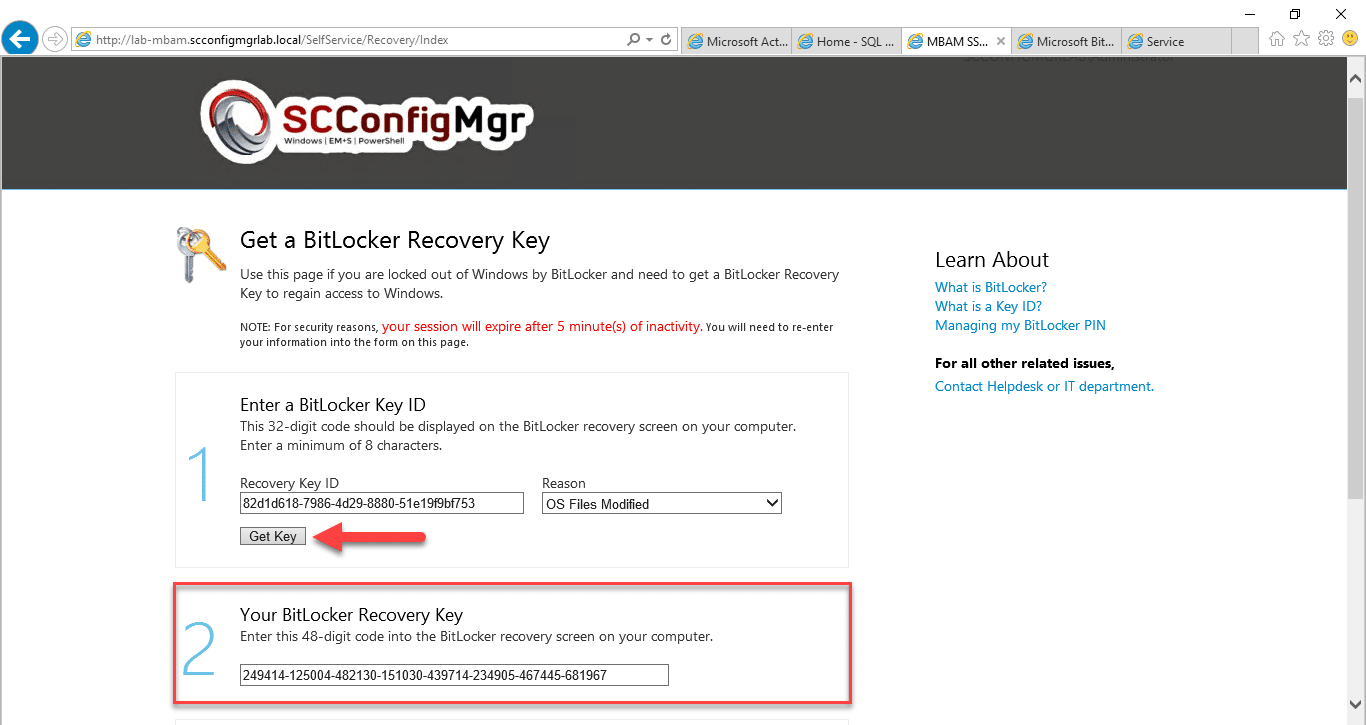
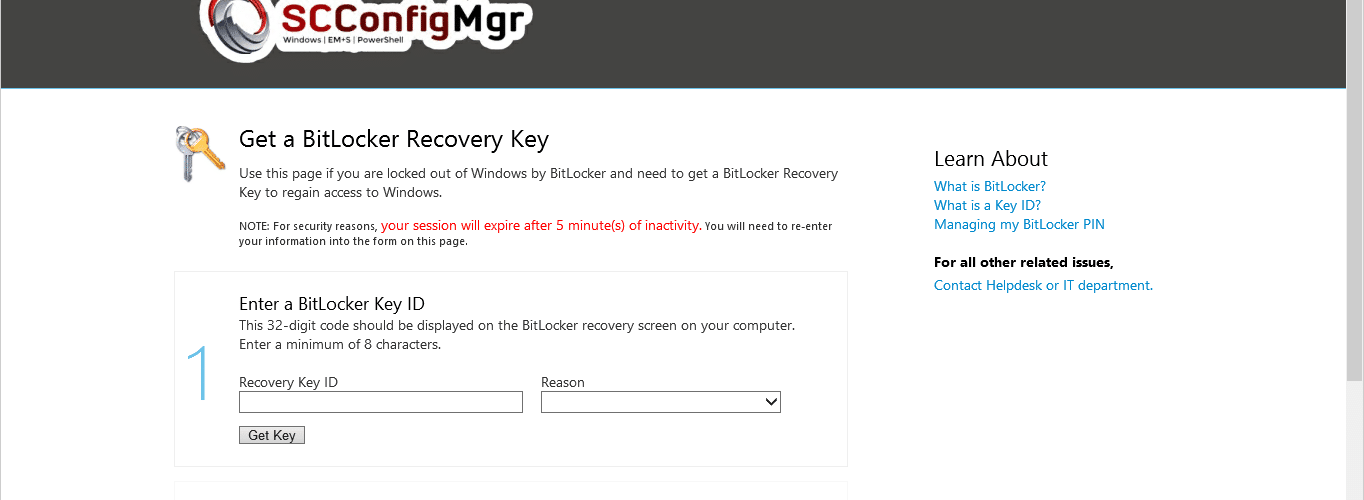
Self Service Portal
- Launch the Self Service portal in a web browser, enter the Recovery Key ID and provide a reason for the recovery
- Click on Get Key
- You should now be provided with the BitLocker Recovery Key;
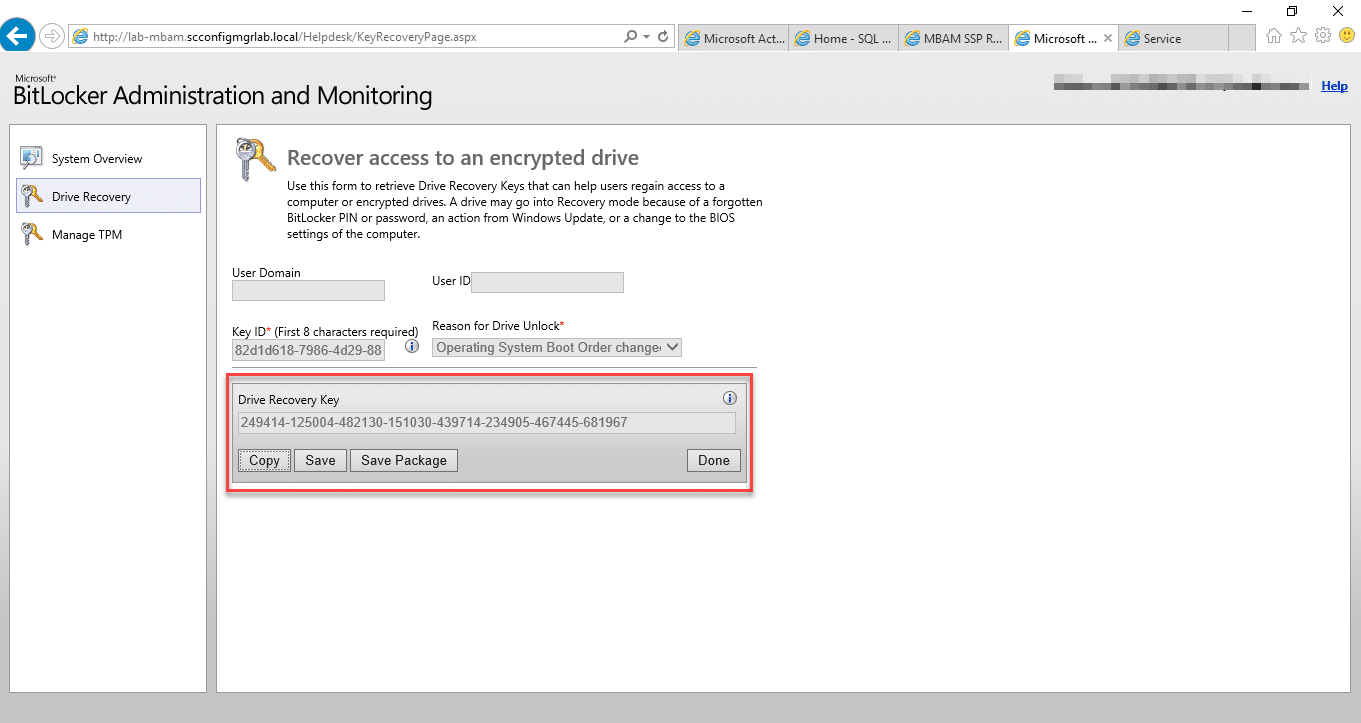
Helpdesk Portal
- Launch the Helpdesk portal using a web browser (assuming you are a member of the Advanced Helpdesk security group for this example)
- Click on Drive Recovery
- Enter the Recovery Key ID
- Click on the Submit button
- You will now be presented with the Recovery Key
Testing the recovery process
At this point you might want to simulate a recovery key event, this again is simple to do, simply go back to your client and run through the below process.
- Open the Command Prompt / PowerShell window and type;
Manage-BDE -ForceRecovery C:
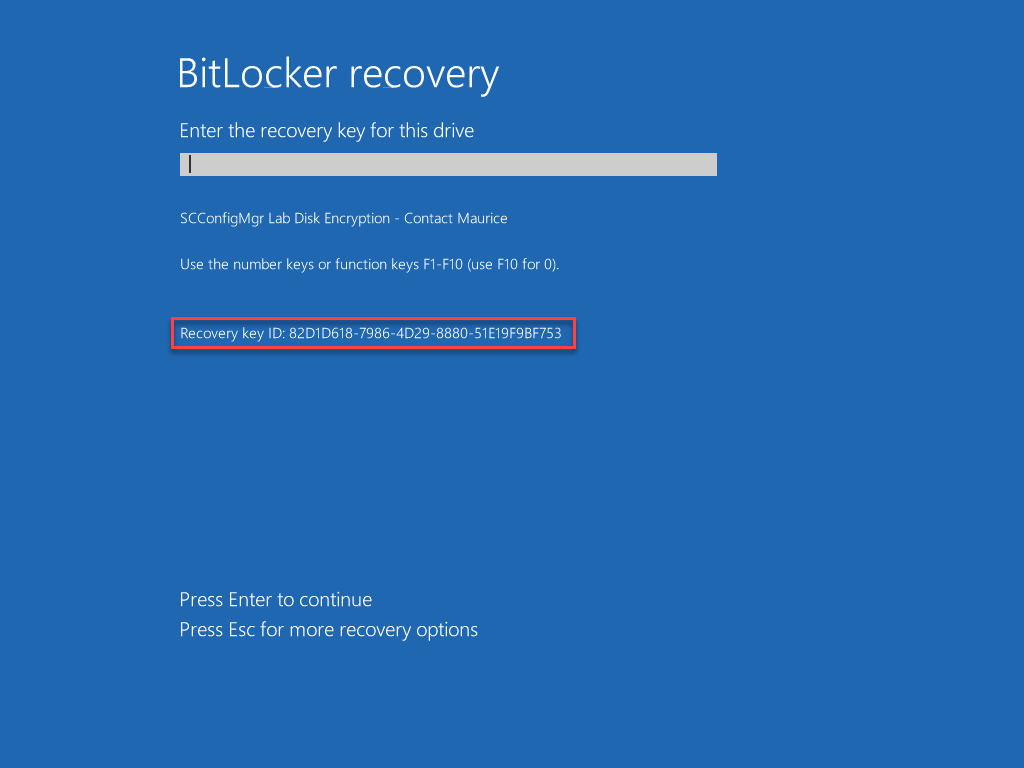
- You should now have a screen similar to the one in the below example;
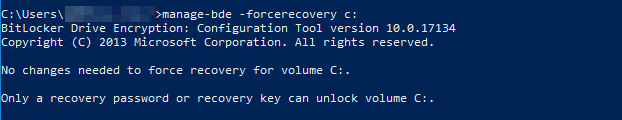
- Restarting the machine will now invoke the BitLocker Recovery screen;
Local, ConfigMgr Hardware Details and SQL Reporting Services Audit Report
Auditing of your environment will typically take place through the built in reports with MBAM delivered via SSRS. There are other methods however so lets take a minute to look at all the methods.
Locally – PowerShell
Should you wish to validate the settings applied to your encrypted hard disk are the same as those set in your GPO, you can launch PowerShell to review the active settings;
- Open an administrative PowerShell window
- Type in the following;
Get-BitLockerVolume | FL - You should now be presented with a screen similar to the one below;
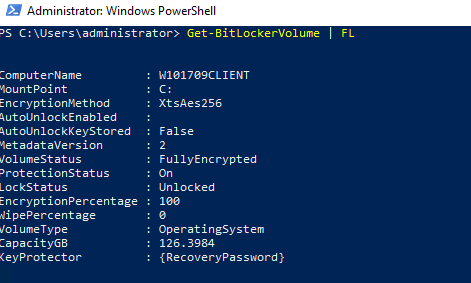
With this information you can now observe the current encryption state and cipher used, comparing this to your GPO to ensure compliance.
Configuration Manager – Hardware Inventory
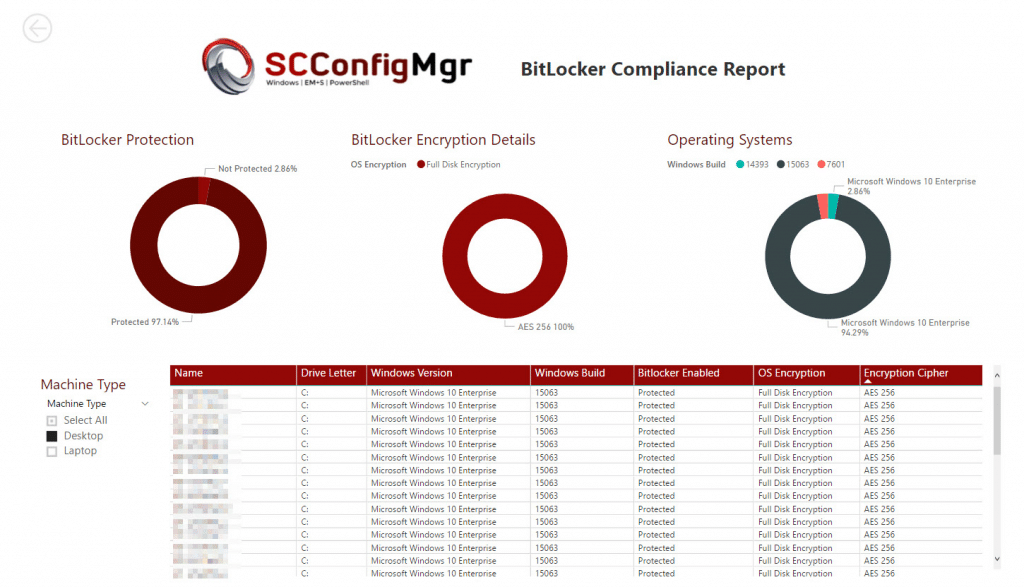
Back in November 2017 I wrote a post on how to use ConfigMgr Hardware Inventory class information to generate a PowerBI compliance report. See the following link for the full post – https://msendpointmgr.com/2017/11/14/bitlocker-compliance-reporting-with-powerbi/
MBAM SQL Server Reports
MBAM of course provides its own reporting. Opening a browser and browsing to the Reports server set up during the MBAM installation will provide reports similar to the one in the below screenshot;
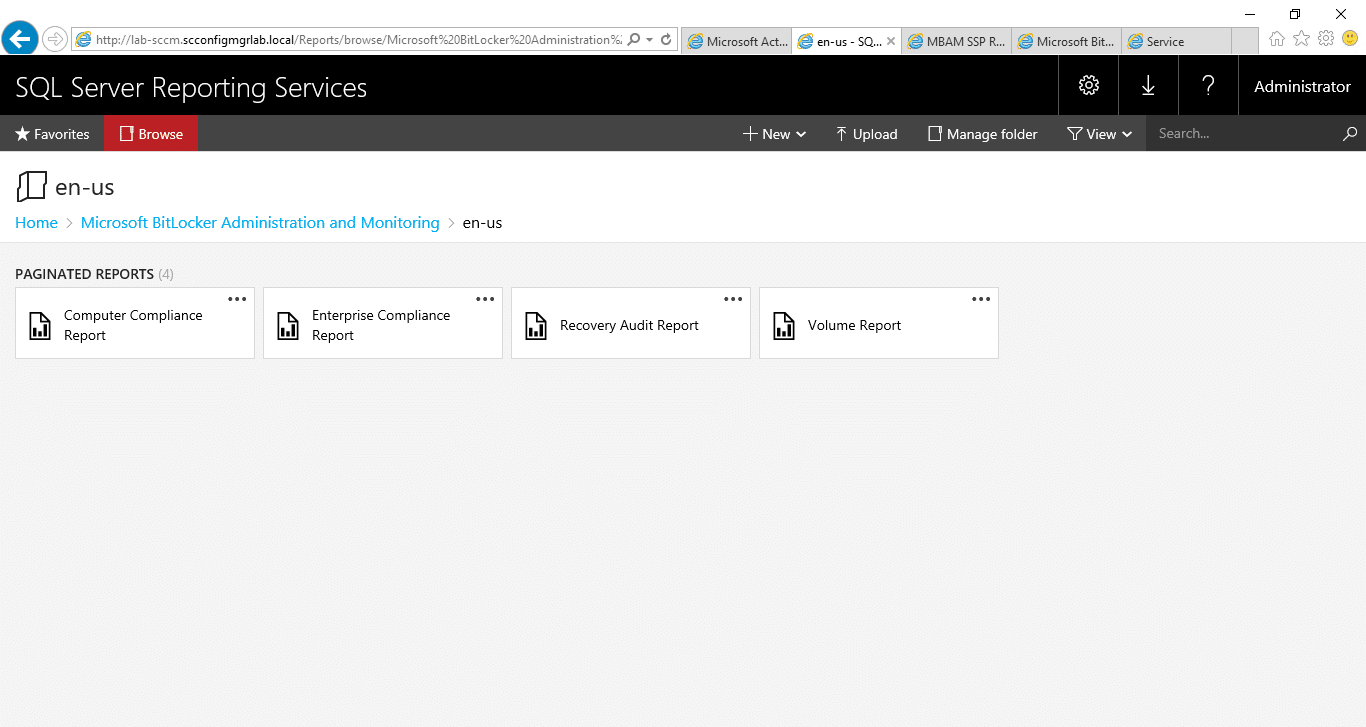
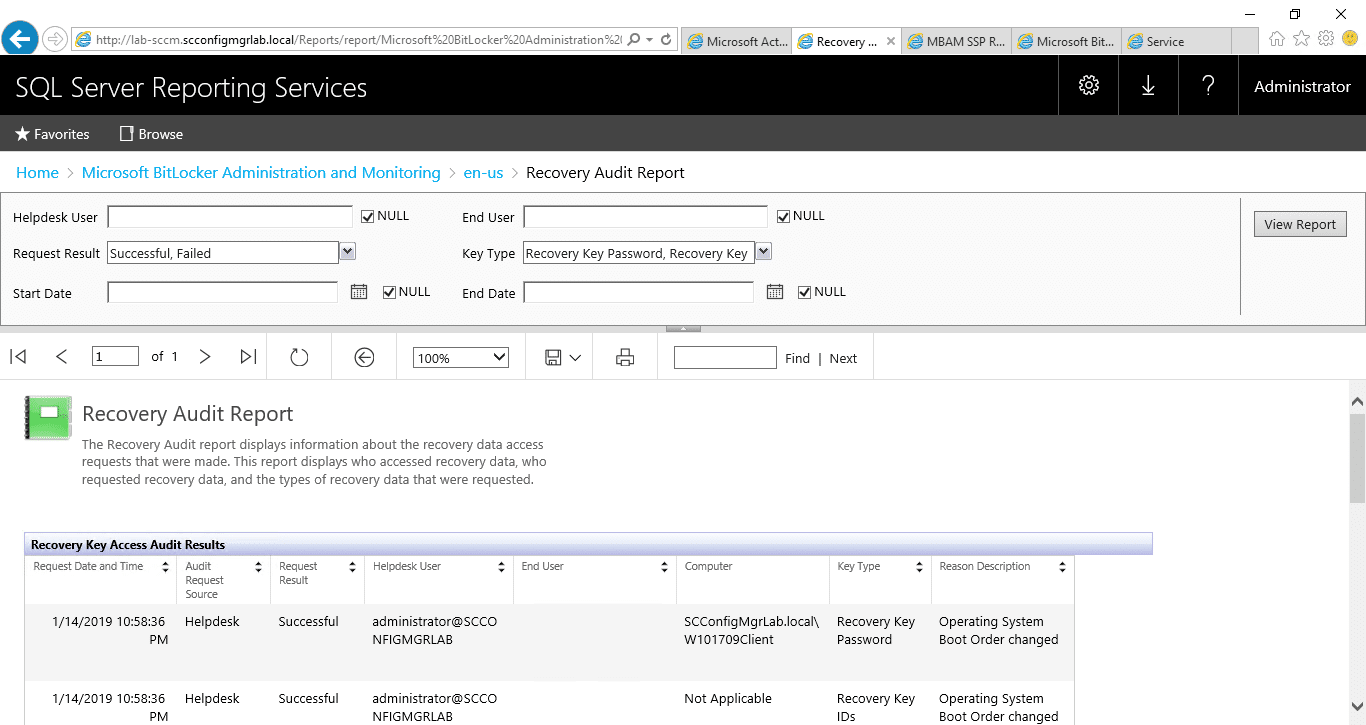
Recovery Audit Report
Here you can view all of the recovery actions taken through the self service and helpdesk portals;
Compliance Report
The compliance report helps you to identify those machines on your network which are failing to adhere to the policies deployed via group policy;
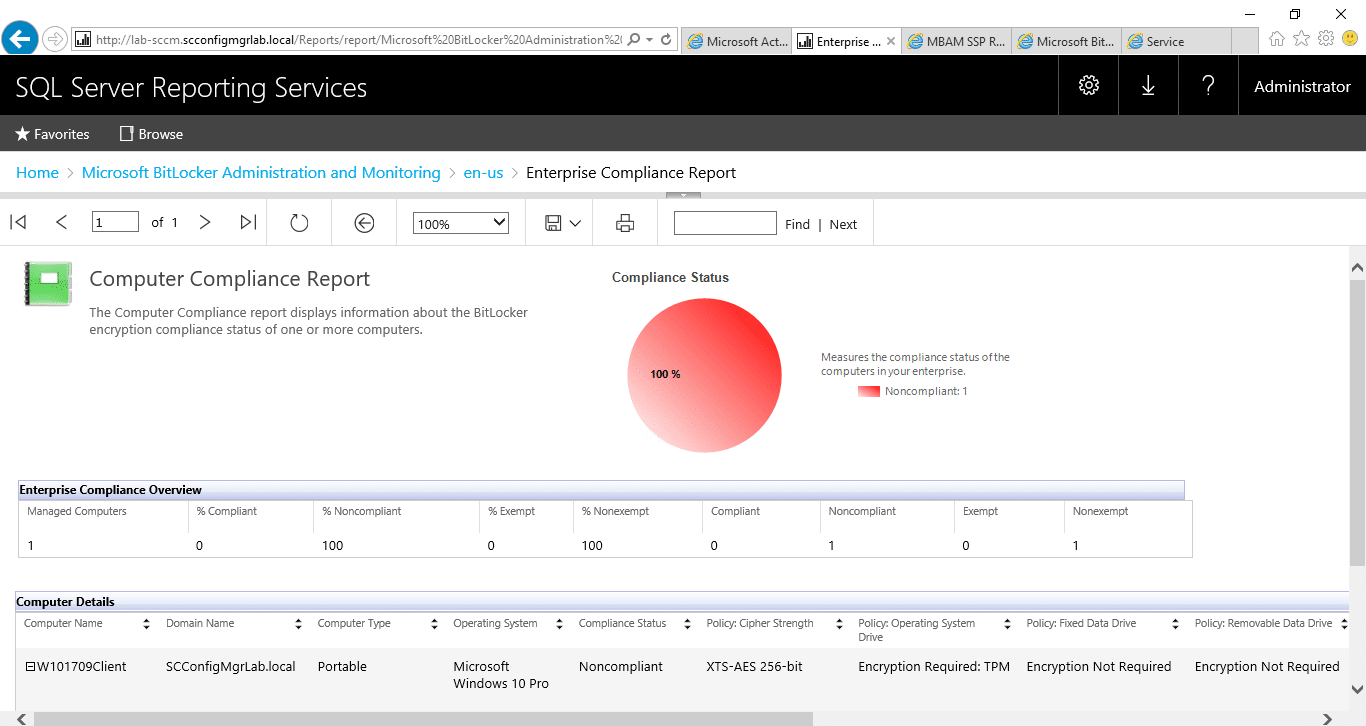
As you might of spotted in the above, the machine in question is listed as non-compliant. In this instance the machine in question is a VM and has TPM compatibility issues, this can be determined by running the following process;
- Launch an administrative PowerShell window
- Type the following command; Get-WMIObject -class mbam_volume -Namespace root\microsoft\mbam
- You should now have a screen similar to the one below;
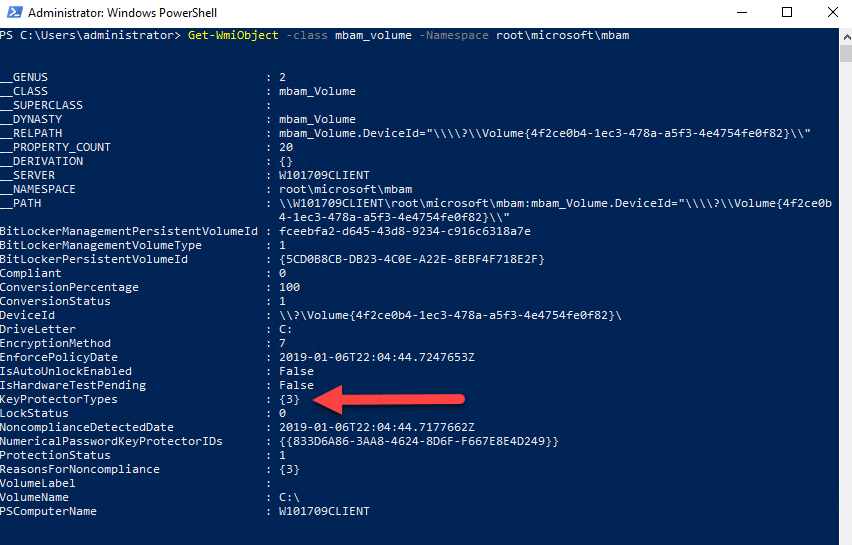
- Using the KeyProtectorStatus values, visit the following URL and match your values – https://docs.microsoft.com/en-us/microsoft-desktop-optimization-pack/mbam-v25/determining-why-a-device-receives-a-noncompliance-message
- In this example the reason is; 3- MBAM Policy requires this volume use a TPM protector, but it does not.
Conclusion
I hope you found this series on MBAM useful. For how long this solution remains in organisations is unclear, but with extended support ending in 2024 time is ticking by for a feature rich cloud based alternative. For all its legacy traits however, MBAM still provides many with the functionality they require right now.
Thanks for reading.








Great article, Maurice. Not really related to the installation of MBAM, but do you know if Bitlocker Network Unlock server feature works with MBAM?