This is a post about enabling BitLocker on non-HSTI devices with Windows 10 version 1809 and standard user permissions.
First of all a little background on HSTI. HSTI is a Hardware Security Testability Interface. It is an interface to report the results of security-related self-tests. Its purpose is to provide high assurance validation of proper security configuration.
The enhancement with Windows 10 version 1809 is that we are able to activate BitLocker with a MDM policy (Intune), even for non-HSTI devices and on Windows 10 Pro Edition. This was not working with Windows 10 version 1803 or lower and the community came up with custom solutions to handle this like custom PowerShell scripts deployed via Intune Management Extension. If we wanted to use Intune native MDM policies via the BitLocker CSP we needed HSTI compliant devices like the Surface devices or newer hardware devices which are mostly delivered as HSTI compliant devices now. To successful start the encryption as a standard user, a Windows 10 version 1803 was the minimum as the feature was introduced with this version.
The prerequisites for Intune BitLocker configuration are
- Windows 10 version 1809 Enterprise and Pro
- Azure Active Directory joined devices
- Microsoft Intune
- non-HSTI device
Older devices can be protected by Intune BitLocker policy now?
Yes, as long as they are running Windows 10 version 1809. The most common problem is that we do not replace all devices in every Windows 10 project to have only latest HSTI compliant devices in the environment. We have to support older devices purchased maybe not long ago but not HSTI compliant. These devices can now be managed by an Intune device configuration policy to turn on BitLocker silently without administrative permissions as long as the device is a Windows 10 version 1809 device.
What do we need to do?
Currently at the time of writing we need two configuration policies. One endpoint protection profile and a custom profile.
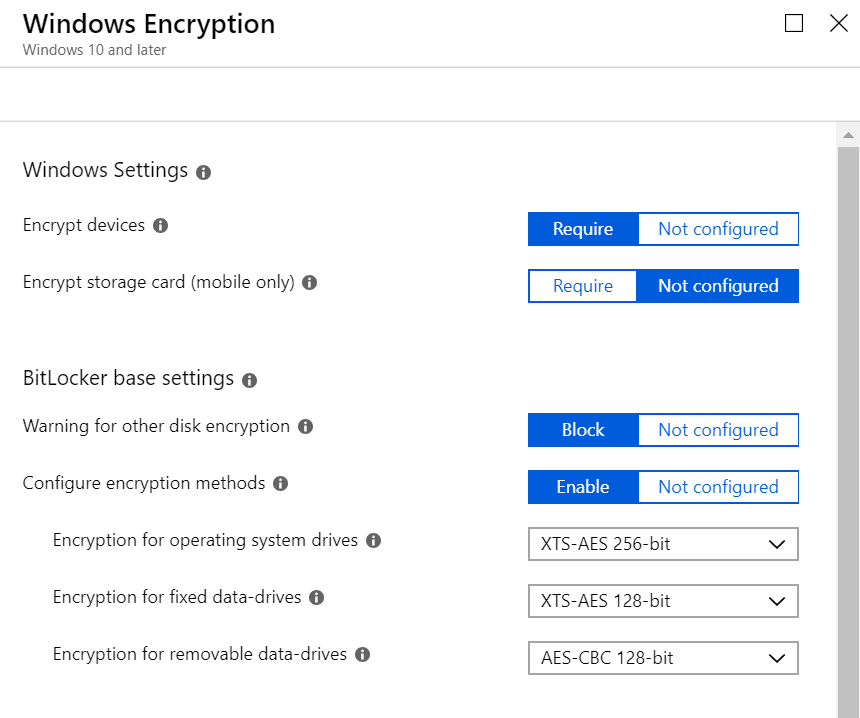
The endpoint protection profile configures the silent BitLocker enforcement and other parameters like encryption strength. Go to Microsoft Intune > Device configuration – Profiles > yourpolicyname – Properties > Endpoint protection > Windows Encryption
Set Encrypt devices to Require
Set Warning for other disk encryption to Block
Sure you can set other parameters like encryption methods as well, but for a functional test this is enough.
These two settings make sure the encryption starts and it starts silently as we block the warning dialog for other disk encryption software.
Example shown below:
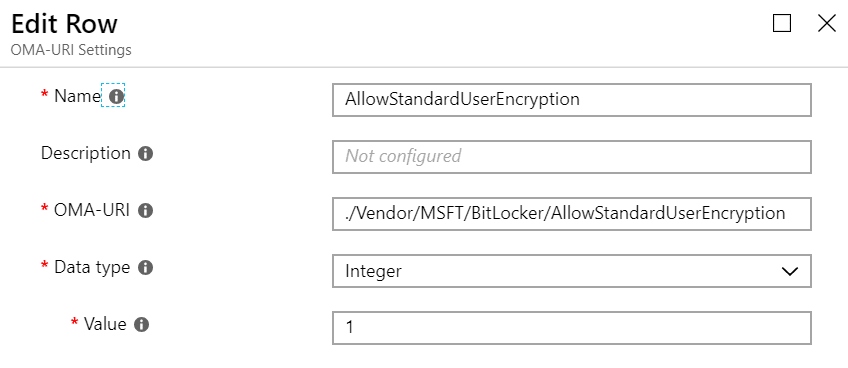
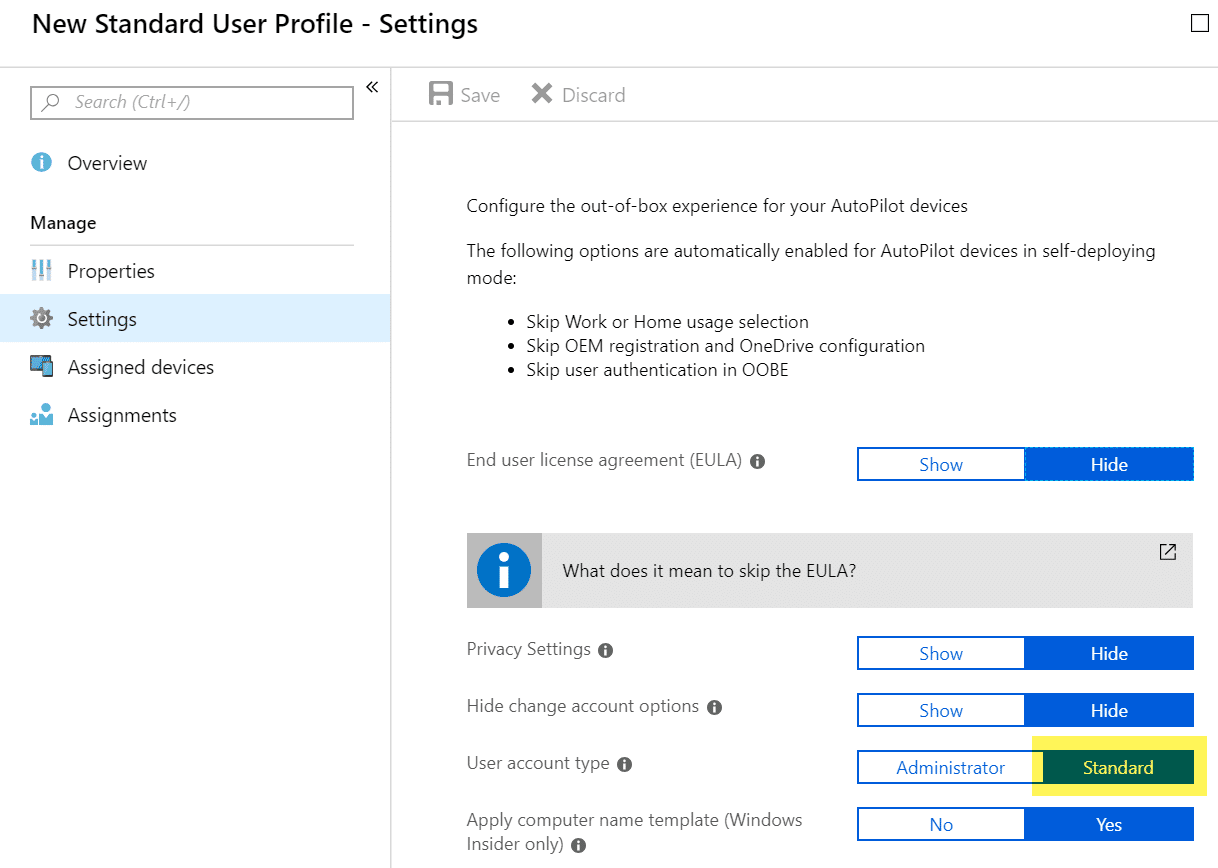
The second profile is a custom profile (at time of writing it was not available in the UI) and it configures the ability to enforce the BitLocker encryption even when standard users are logging in. For example when the Windows 10 device is enrolled with an Autopilot profile where the user account type is set to standard user. AllowStandardUserEncryption is a new setting introduced with Windows 10 version 1809 BitLocker CSP and must be used in conjunction with the setting “Warning for other disk encryption set to Block” otherwise it is not functional!
The custom OMA-URI configuration must be configured like this:
OMA-URI: ./Vendor/MSFT/BitLocker/AllowStandardUserEncryption
Data type: integer
Value: 1Example shown below:
The two policies must be assigned to a user group or device group to test the new policies. To force the user type to a standard user after enrollment we need an Autopilot profile and assign it to our device.
If we now enroll a new Windows 10 version 1809 non-HSTI device it must be encrypted silently and the recovery key must be backed up to Azure AD.
How can I easily verify this?
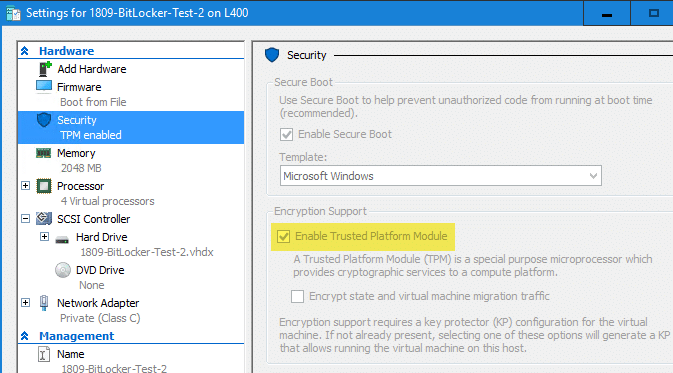
I used a Hyper-V VM Generation 2 with an enabled TPM module:
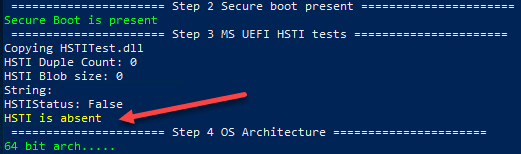
To test if the VM is reporting as a non-HSTI compliant device I downloaded the Device Guard and Credential Guard hardware readiness tool and verified the HSTI status with the following PowerShell command:
.\DG_Readiness_Tool_v3.5.ps1 -CapableThe result is displayed like this:
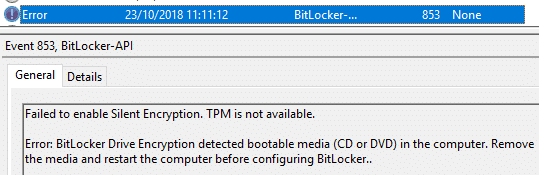
During my test I had to make sure that after the first restart, the Windows 10 version 1809 ISO is ejected, otherwise silent BitLocker encryption will fail. This is because the system does not have the normal start parameters during the BitLocker and TPM provisioning. The platform would take into account the additional media as the normal platform verification parameter. Which means after ejecting the ISO it would have prompted us for the recovery key. Microsoft takes care of this situation and does not start the BitLocker provisioning process at all. So, the generation of the platform default configuration parameters for later verification to unlock the TPM is prevented, as long as a removable media is inserted. See the failure event here:
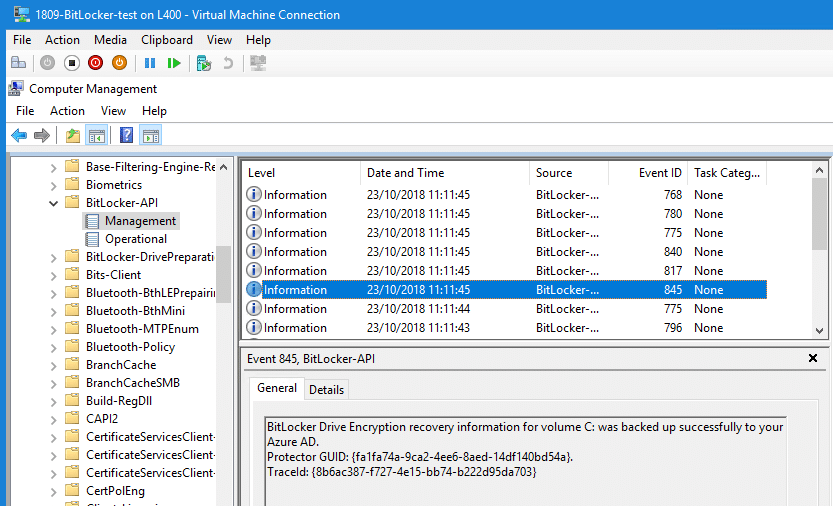
Without an ISO it will successfully starts the encryption and key backup to Azure AD. A success event is shown below:
The BitLocker state can be verified with the PowerShell command on the client:
Get-BitLockerVolume | fl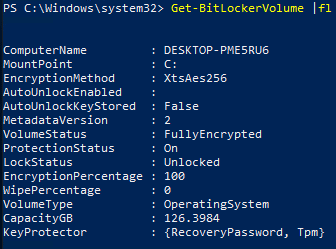
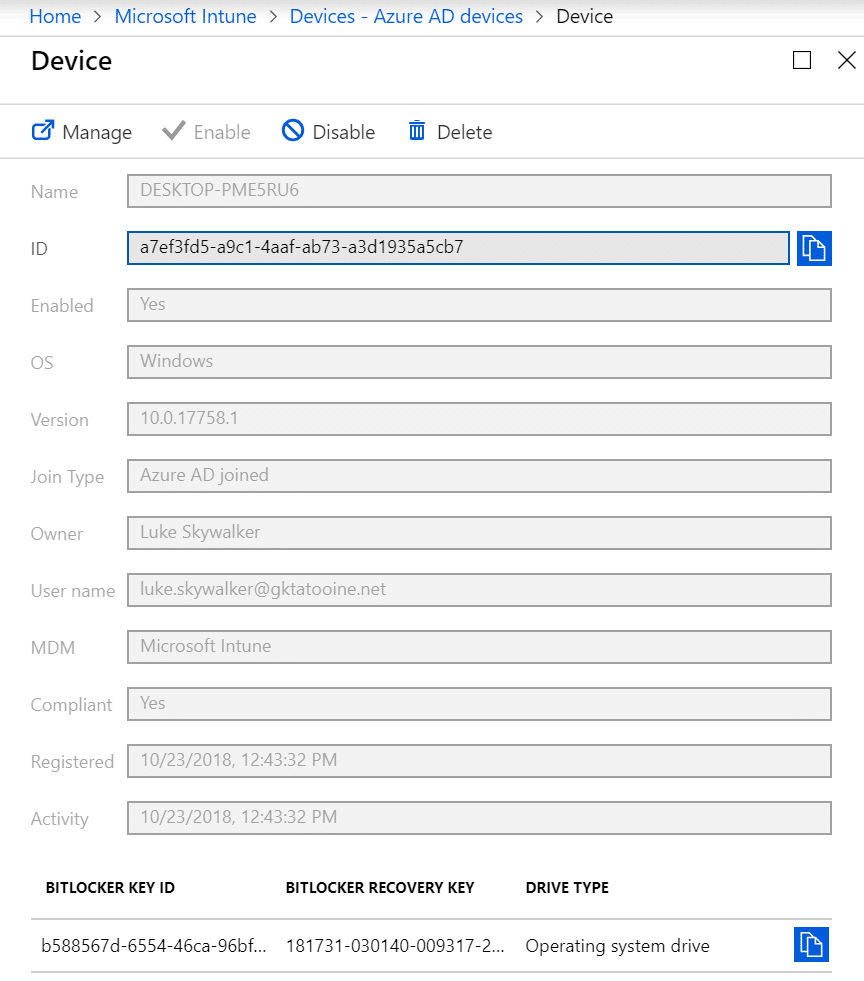
In the Intune portal we can see the recovery key appended to the AAD device object:
Further information
What’s new in Windows 10, version 1809 for IT Pros
https://docs.microsoft.com/en-us/windows/whats-new/whats-new-windows-10-version-1809#bitlocker
Device Guard and Credential Guard hardware readiness tool
https://www.microsoft.com/en-us/download/details.aspx?id=53337
Hardware Security Testability Specification
https://docs.microsoft.com/en-us/windows-hardware/test/hlk/testref/hardware-security-testability-specification
Go ahead and start encrypting all your Windows 10 devices to strengthen your security level 👍








Hi Oliver
Superb work as usual.
Anyway, will this work on “Devices with non-compatible TPM”?
Info appreciated
Honestly I don’t think so. I never tested but I think it won’t work. I know it works for TPM equivalent hardware like the firmware TPM alternatives for China.
Doesnt work with Hybrid join ? bit locker keys are not backed up for standard user. Any solution
Hi no this is not working for hybrid joined devices, you need to use MBAM then. The backup of BitLocker keys as standard user is working as soon as you specify the OMA-URI, but again this is a Azure Active Directory joined scenario.
First, thank you for your article.
For Autopilot Hybrid join, I think the problem went from the fact that Hybrid Azure AD joined device have no owner assigned in Azure AD. When I assign a device Owner (with AzureAD PS module), recovery key are successfully saved to AD.
Nice, thanks for sharing the finding!
Hi Oliver,
This looks great but do you know if this will work for Hybrid Joined clients?
I want to roll out BitLocker using the Hybrid Autopilot scenario with standard users.
Best Regards
Olof
Hi Olof,
my example does use MDM for settings management, as long as your devices will also use MDM this is possible with Hybrid Joined devices also.
best,
Oliver
Thanks,
With Autopilot and AAD join it was working just fine, but since we switched to autopilot hybrid join it no longer works. I will do some more testing.