Friday arrived early this week in the ConfigMgr community, with the announcement that the much anticipated 1806 build had hit public availability on the fast ring. This is a feature packed release, Nickolaj has already covered the highly requested third party patching integration in this post –https://msendpointmgr.com/2018/07/31/configure-and-deploy-third-party-software-updates-with-configmgr/ in this post I am going to run through some of the security related enhancements in this release.
Client Push Installation
Client push installation is a quick and easy means of getting the ConfigMgr client onto machines in your estate, however it could have a potential nasty sting in its tail. The sting could take shape in the form that credentials could be harvested and this would provide local administrator access to at worst case, every computer within your environment.
To address this issue Microsoft published a best practice on security relating to the use of the client push account (https://docs.microsoft.com/en-us/sccm/core/plan-design/hierarchy/security-and-privacy-for-site-administration), in which deployment of the client via GPO was the preferred approach.
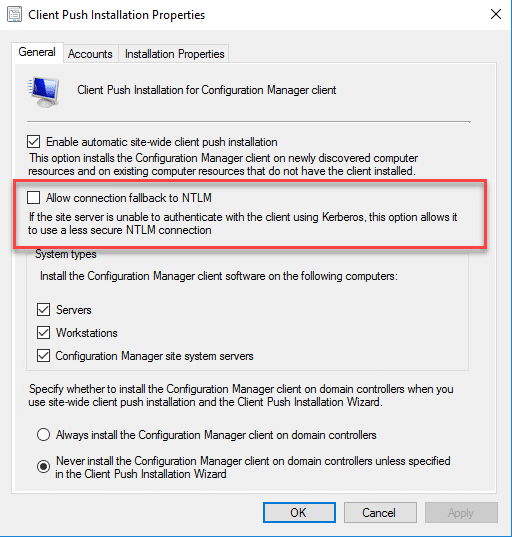
In 1806 security has been enhanced with the introduction of Kerberos mutual authentication. This new authentication method is used by default, with an option to revert to NTLM authentication in the event of authentication failure.
Enhanced HTTP – Pre-Release
Using HTTPS has been the recommendation by the product team for a number of years now, why do things in an insecure manner when there is a secure way right? Well for some organisations this has been something that was on the “to-do” list as it required an internal public key infrastructure to be in place. This becomes an issue when it comes to supporting machines on a workgroup or via CMG. This is in the process of being addressed for Azure AD joined systems, providing secured communications out of the box.
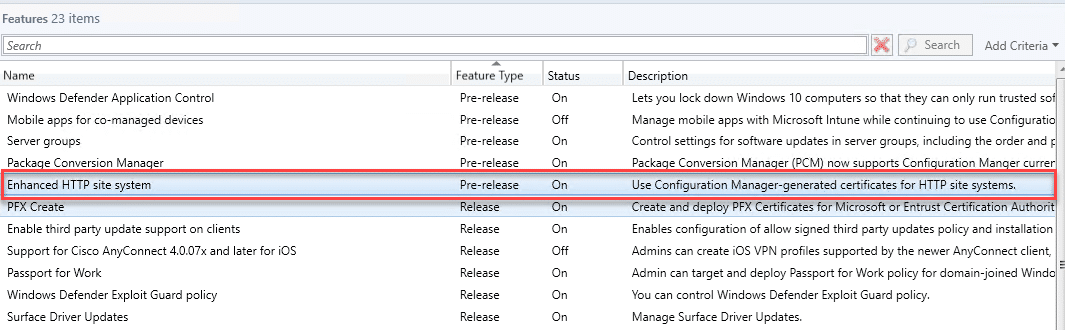
Configuration Manager in this instance will manage the creation of certificates for HTTP systems. You can see this by first of all enabling the Pre-Release feature;
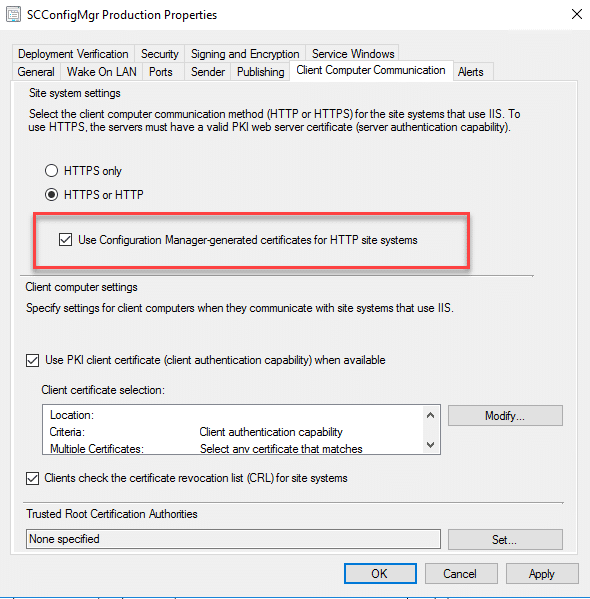
Once enabled if you go to the Site Properties and click on the Client Communications tab you will have a new checkbox;
The new features works in the following scenarios;
- Client to HTTP Management Point
In this scenario AAD joined clients communicating with a CMG configured for HTTP will be secured when communicating with the MP by automatic generation of an SSL certificate. - Client to HTTP Distribution Point
In this scenario workgroup or AAD joined devices communicating with distribution points will download content over a secure channel
Network Access Account
The enhanced HTTPS feature also has a knock on security impact for task sequence deployments, both initiated through PXE/Boot Images and the Software Center. In that instance certificates are generated and secure transport communications.
Task Sequence Variable Additions
Do not display this value
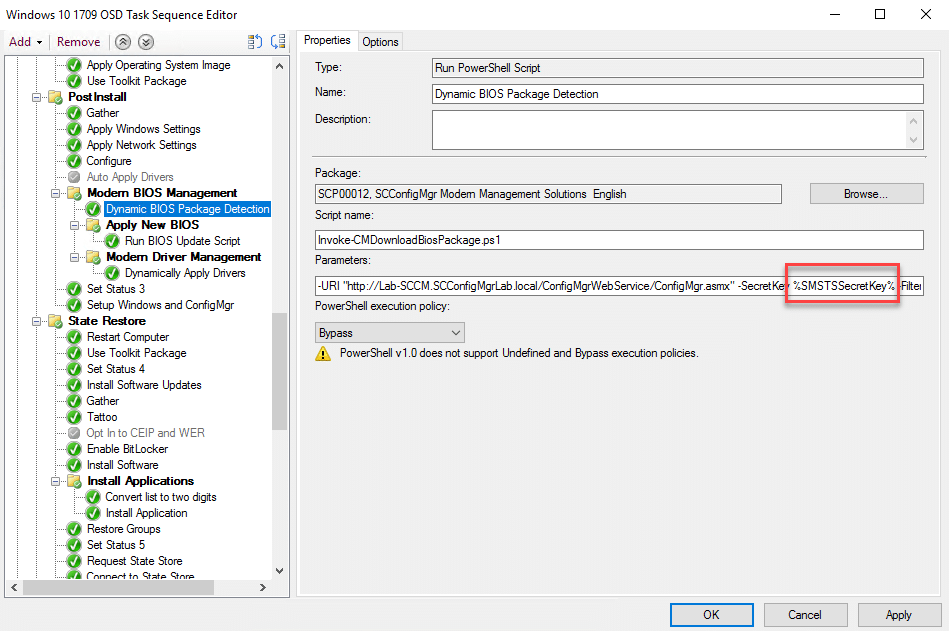
One of the nice additions here for task sequence variables is the ability to hide the contents, this is particularly useful when storing passwords. In the below example I have added a variable containing the SecretKey for the ConfigMgr Web service;
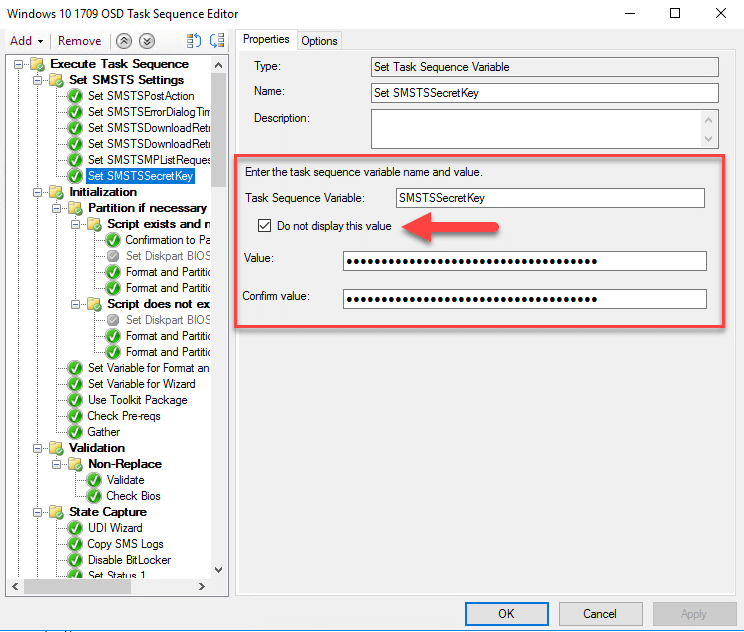
Now later in the task sequence I can call the variable to retrieve the value without disclosing it in clear text;
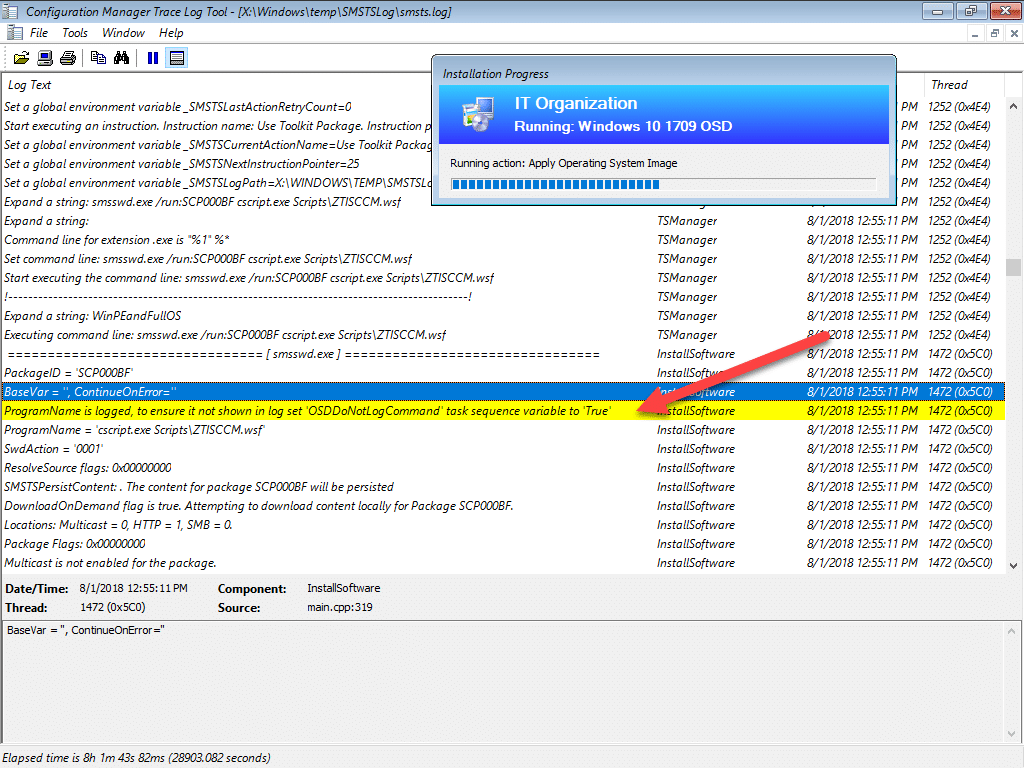
OSDDoNotLogCommand
Another mention is the new TS variable is available for hiding the full command during the TS. Simply set OSDDoNotLogCommand with a value of “True” and command line instances will be masked;
Drive Encryption
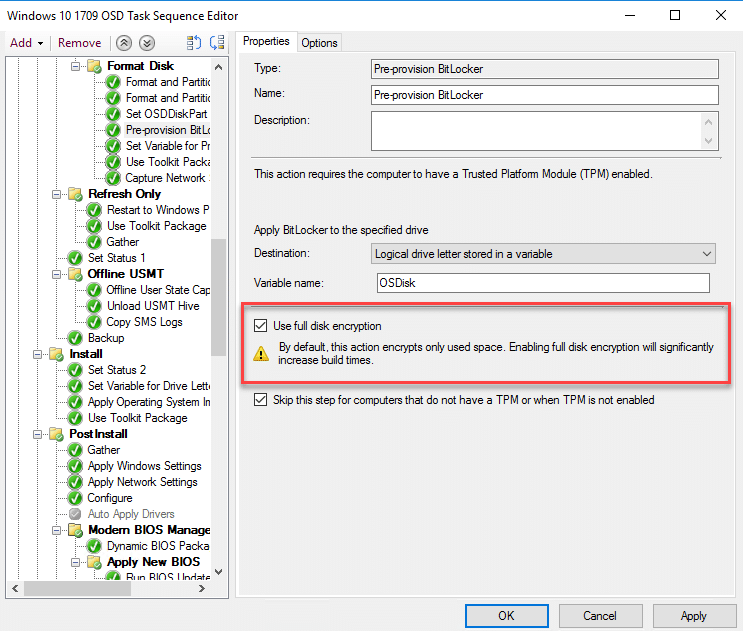
A new option to fully encrypt the entire disk now exists for both the pre-provision step and the enable BitLocker step. This might be a requirement in your organisation, however be prepared for a longer deployment time ad the default method only encrypts the used storage;
Thanks for reading and muck kudos to the ConfigMgr Dev Team! Keep the good stuff coming!









Add comment