So you have a complex password policy on your domain, ensuring that users change their password every 60-90 days, passwords are complex, their passwords can’t be re-used and your users are not local admins but one thing poses a security risk, the local administrator password.
The chances are you have deployed your standard Windows image using a password specified within the image/MDT or SCCM task sequence and in some cases you do not have the IT resources to ensure that this password is changed on a regular basis and even if you are, are you ensuring that the passwords are being documented and stored securely?.
Security Risk – Local Administrator Rights
If you do not have a well maintained local administrator password strategy it opens your network up to security vulnerabilities including elevation of privilege. It isn’t going to go down well when your standard local workstation admin password is shared and users add themselves to the local admin group, potentially in a worst case scenario adding malware, key loggers etc.
The Answer – Microsoft Local Administrator Password Solution (LAPS)
Microsoft LAPS is a free tool released back on May 1st 2015 and allows you to automate the process of updating local administrator passwords on your workstations and servers across your Active Directory domain/forest. LAPS uses a local agent in conjunction with GPO deployed settings to update the local administrator password at set intervals, based on complexity settings that you specify and most importantly it automatically stores backups of this info within Active Directory.
Deploying Microsoft LAPS
First of all you will need to download the installer from the following URL – https://www.microsoft.com/en-us/download/details.aspx?id=46899. In the below section we will run through the entire installation and configuration process;
Management Server Installation
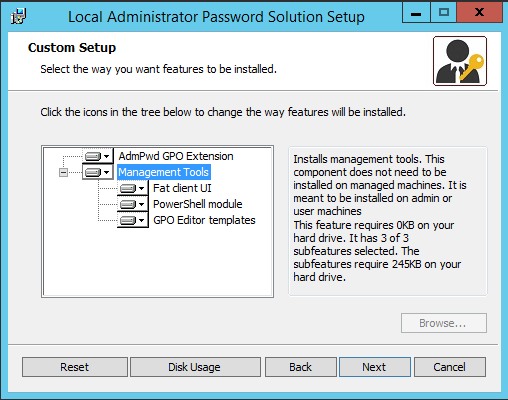
A single installer is used for both the server and client installs, the only real difference being that the management tools need to be installed on the management server. Run the LAPS.x86 or LAPS.x64 installer as per your system architecture, then run through the following;
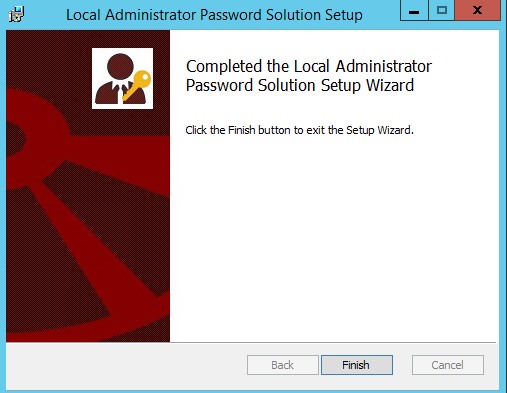
Launch the installer
At the custom setup screen select the management tools and select run from my computer and then click Next
Click on the Finish button to finalise the install
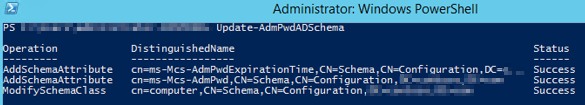
Active Direct Schema Modification
In order for computers to write back their local administrator passwords and expiry date/time, a schema update is required. The update adds the following two values:
ms-Mcs-AdmPwd – Stores the password in clear text
ms-Mcs-AdmPwdExpirationTime – Stores the time to reset the password
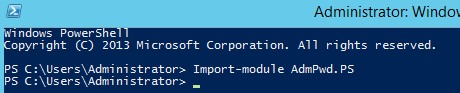
To add these values, launch a PowerShell session on your management server and perform the following actions;
Type – Import-Module AdmPwd.PS to import the required LAPS module
Note: If you have an RODC installed in the environment and you need to replicate the value of the attribute ms-Mcs-AdmPwd to the RODC, you will need to change the 10th bit of the searchFlags attribute value for ms-Mcs-AdmPwd schema objet to 0 (substract 512 from the current value of the searchFlags attribute). For more information on Adding Attributes to or Removing attributes from the RODC Filtered Attribute Set, please refer to https://technet.microsoft.com/en-us/library/cc754794(v=WS.10).aspx.
Active Directory Rights
Computer Rights
In order for computer accounts to write values to the ms-Mcs-AdmPwdExpirationTime and ms-Mcs-AdmPwd attributes in Active Directory, the following PowerShell command needs to be run (note if closed the previous PowerShell window you will need to run Import-Module AdmPwd.ps again)
Set-AdmPwdComputerSelfPermission -OrgUnit "name of the OU to delegate permissions"
User Rights
By default members of the Domain Admins group will have rights to view the local administrator passwords stored in Active Directory, however what happens if you want your desktop support team to view them?. To facilitate this you will need to delegate rights.
To do so use the following PS command:
Set-AdmPwdReadPasswordPermission -OrgUnit "name of the OU to delegate permissions" -AllowedPrincipals "users or groups"
Going another step further you can also delegate rights to allow groups or individuals to force a password change. To do so use the following PS command:
Set-AdmPwdResetPasswordPermission -OrgUnit "name of the OU to delegate permissions" -AllowedPrincipals "users or groups"
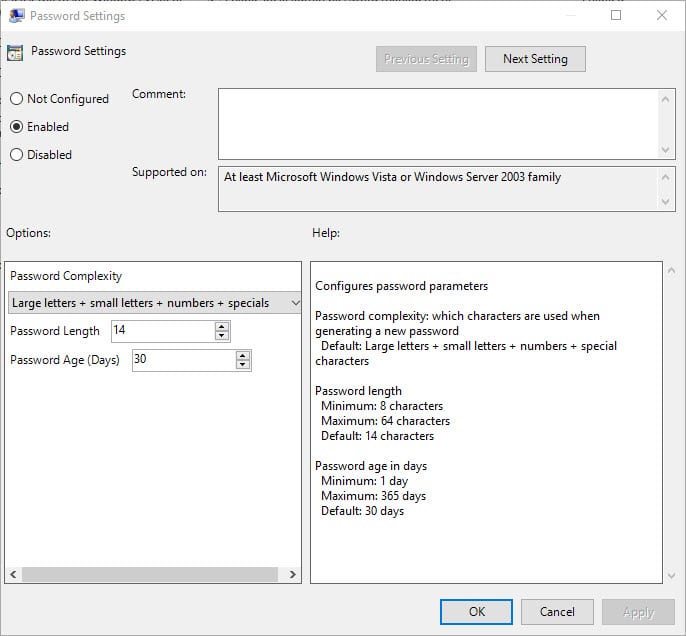
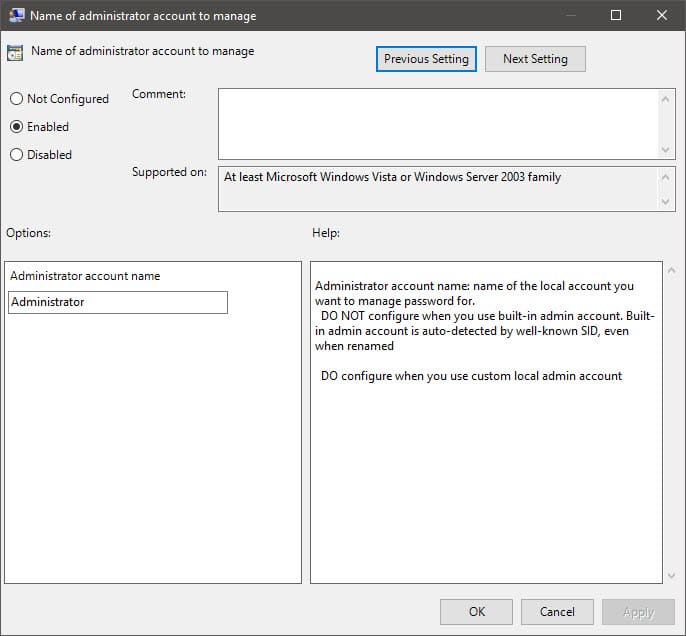
Group Policy ConfigurationFirst of all you will need to copy the LAPS ADMX and ADML files to your central store. The two files are located in the %WINDIR%\PolicyDefinitions folder on the management server.Now follow the below;
- Open Group Policy Manager and either create or modify a GPO that you wish to apply the LAPS settings
- Expand Computer Configuration\Policies\Administrative Templates\LAPS
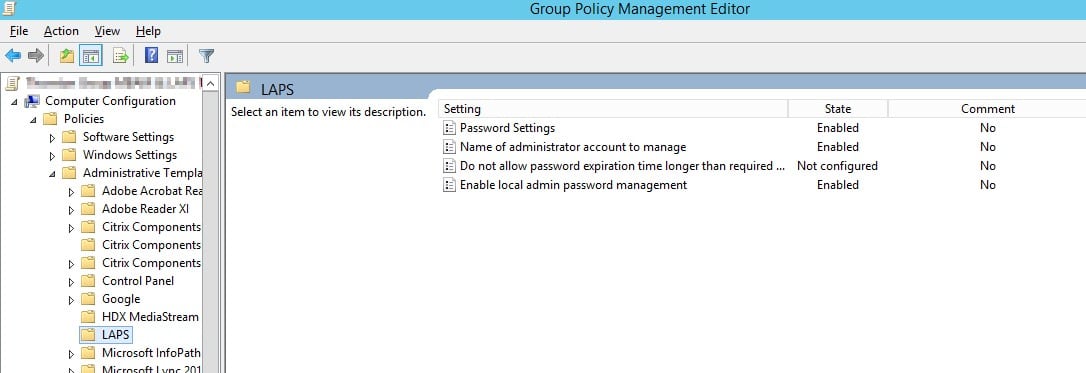
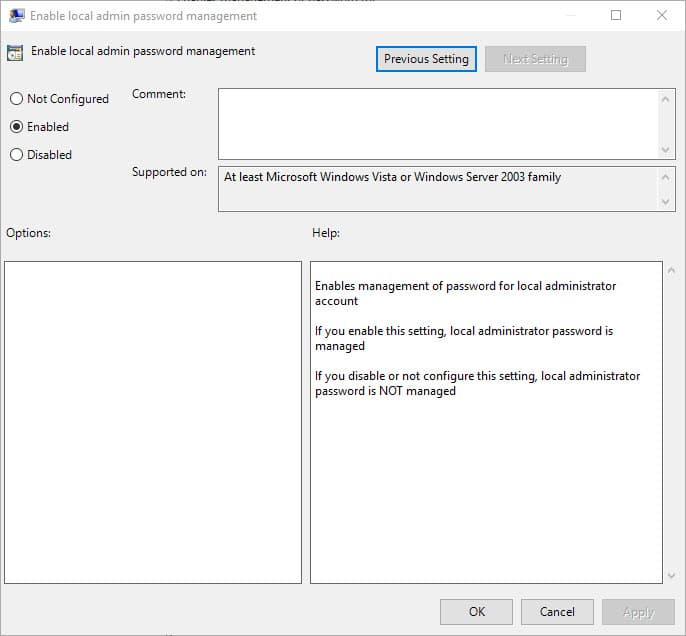
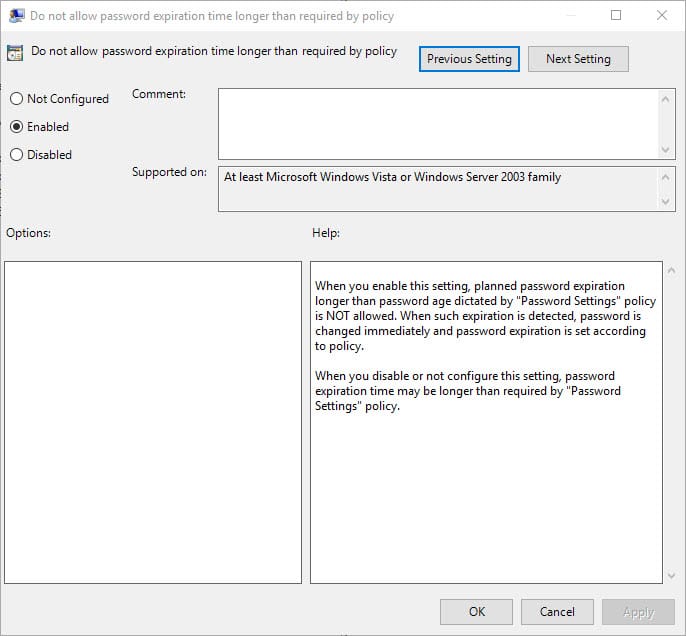
Configure your Password Settings, Name of the Local Admin Account and Enable Password Management, as per the below examples:
Deploying the LAPS client
Deploying the client is a simple process. Using the same MSI installation files you can deploy the client to your x86 and x64 clients via GPO, SCCM or other third party application deployment systems. Simply use the /quiet switch for client deployments.
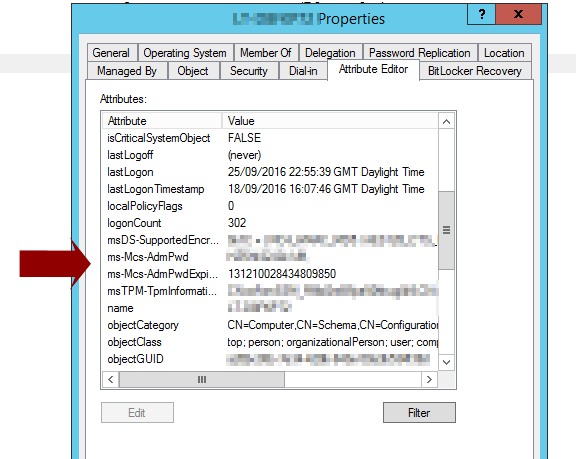
Check its working..Active Directory Users & Computers
Opening the Active Directory Users & Computers console and viewing the Attribute Editor of a machine located within the OU that you earlier deployed your LAPS enabled GPO to, should result in values being available as per the below screenshot;
LAPS Admin GUI
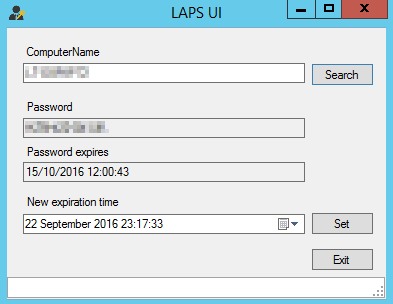
On the management server that earlier installed LAPS on, you will have the LAPS GUI. This will allow you to both look up details from computers but also set a new expiration date for the existing local admin password;
For more info on LAPS, visit Microsoft TechNet – https://technet.microsoft.com/en-us/mt227395.aspx










[…] Extension for SCCM 2012 R2 + LAPS is higly recommended for most enterprises see Maurice’s post about it […]