In most of the customers engagements that I participate in where we’re in the process of setting up a new ConfigMgr environment, one of the daunting tasks that we’re faced with is to configure the Discovery Methods. More specifically, adding the containers (OU’s) for Active Directory User Discovery as well for Active Directory System Discovery. For Active Directory Group Discovery, you can simply just determine the required groups with PowerShell and then add them all by their distinguished name with a simple copy paste. This is however not the situation for User and System Discovery.
Since most of the Active Directory environments often have been around for a very long time, and due to several factors, the OU structure is simply not just suited for specifying a single distinguished name to an OU and then select to recursively include what’s under it. Sometimes, there’s only a few locations that you’d need to include, and in such situations I don’t bother with any kind of automation. However, in the past I’ve always wanted to write a script to automate this task, and I recently had the time to do just that (during a huge ConfigMgr implementation). So in this blog post, I’ll show you how you can leverage the script that I’ve created to import containers (OU’s) by their distinguished names from a CSV file in ConfigMgr.
Determine containers to import in ConfigMgr
Since my script leverage a CSV file for container import, I wanted to give you a few tips on how we can use PowerShell to determine what containers we would want to add to the CSV file. It really helps if you’re able to identify a search string that you can use to query for containers in the Active Directory. For example, in the picture below you can see my lab environment and how I’ve configured it like in real world scenarios that I often run into.

Now, as shown in the picture, this may not be the most efficient structure for various reason. However, I’d rather just work my way around the fact the issue at hand instead of re-structuring the Active Directory. If you’re thinking, that’s not many various locations that for instance user accounts may be stored. Think again when you have perhaps over 100 offices.
Like I said, it’s really helpful if you can determine some sort of search string. In my scenario outlined in the picture above, I could for instance query for all OU’s with the name of Users underneath the Offices OU. Let’s take a look at how we can accomplish just that with PowerShell. Simply run the one-liner shown below to get the objects that you want.
Get-ADOrganizationalUnit -Filter "Name -like 'Users'" -SearchBase "OU=Offices,DC=contoso,DC=com" | Select-Object Name, DistinguishedName

With the objects that we want, we could use any kind of method that PowerShell supports to output the data that we need (the distinguished names) to a text file, directly to a CSV file or perhaps an Excel file if you prefer that.
Construct required CSV file
Now that I’ve shown you a method to determine the distinguished names, let’s have a look at how we should construct a CSV file from that data. Below is my exported distinguished names from the example above, translated into the a format with required headers and additional data that the script needs:

As you can see in the picture above, there are three headers:
- DistinguishedName
- Recursive
- Group
As for the DistinguishedName column, simply just specify the container data that you’ve extracted. In the Recursive and Group columns, add the desired configuration. Options for Recursive is either Yes or No, and for Group it’s simply Included or Excluded. This will be translated into the proper data types required to add the containers to the Discovery Methods. What about System Discovery then? No worries, since what I’ve demonstrated up until now is exactly the same process for containers (OU’s) that you wish to add to the System Discovery Method. The CSV file should also be constructed like shown above.
For demonstration purposes, I’ve saved my CSV file with container data for my Users OU’s in C:\Temp on my Primary Site server.
Obtain the script
As for all of my PowerShell scripts, I’ve uploaded this to my repository on GitHub as well. Browse to ConfigMgr – Site Administration and look for Import-CMDiscoveryMethodContainers.ps1. You also have the option to download it straight from this post, by using the link below:
[download id=”3846″]
Either grab the script from my GitHub repository or download it from the link above.
How to use the script
Now that we’ve downloaded the script, which is placed in C:\Scripts in my lab environment, we can execute it providing the CSV file that we’ce constructed. You may have noticed that the CSV file does not contain the required LDAP:// protocol portions for the distinguished names. Don’t worry, I’ve got you covered. If the script detects that the distinguished name of the current object it’s processing does not have the LDAP protocol prefix, it will simply add it. It will also check for duplicate distinguished name entries, if case you’ve made a mistake in your CSV file, or if it’s already present in the selected Discovery Method. Speaking of selected Discovery Method, that’s where the ComponentName parameter comes into play, as shown in the command line below. You can choose between:
- SMS_AD_USER_DISCOVERY_AGENT
- SMS_AD_SYSTEM_DISCOVERY_AGENT
1. Open an elevated PowerShell console and browse to C:\Scripts.
2. Run the following command:
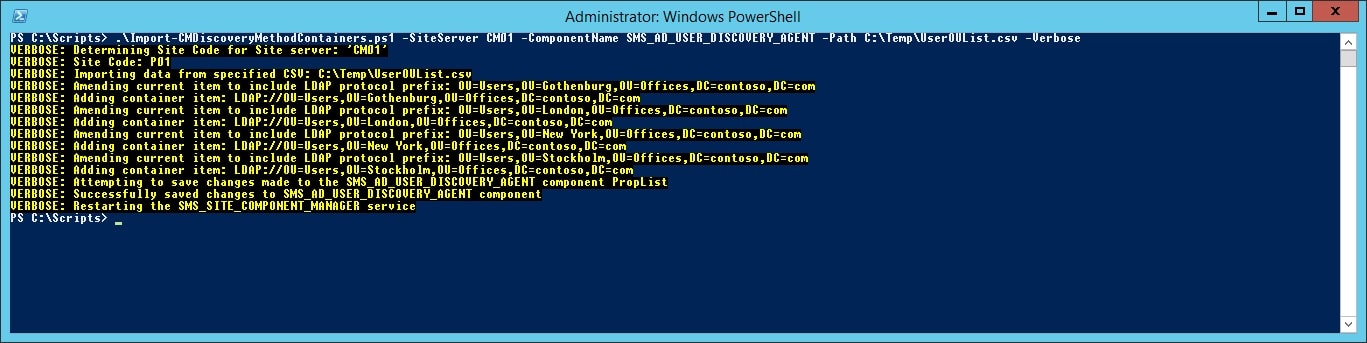
.\Import-CMDiscoveryMethodContainers.ps1 -SiteServer CM01 -ComponentName SMS_AD_USER_DISCOVERY_AGENT -Path C:\Temp\UserOUList.csv -Verbose

And there you have it. Your containers that we determined are now added to the User Discovery Method. Check the Properties of the Active Directory User Discovery to see how it has been extended:

Also, notice how the Recursive and Group columns that we entered in the CSV have been taken into account when the containers have been imported. I hope this helps, and as usual, if you have any questions please leave a comment or send me an email.








I’m at big organization I run get-adtrust -filter * | Select name and get 126 objects how can I Get-ADOrganizationalUnit to read from a text file with the 126 objects.