For a while now we’ve been wondering when we’d be able to manage OS X device with Intune. Almost two weeks ago Microsoft announced the support for managing OS X devices through Mobile Device Management (MDM). This is a great extension to organizations that are either looking to invest in Microsoft Intune, or already have. We all know that OS X devices are becoming more and more popular in organizations, and like Windows, iOS and Android devices, we need to be able to manage them as well. In this post, I’ll show you how easy it is to enroll an OS X device into Microsoft Intune.
If you want to read up on the announcement that Microsoft made for their December update for Microsoft Intune, you can do that here:
https://blogs.technet.com/b/microsoftintune/archive/2015/11/17/enhancing-managed-mobile-productivity.aspx
Requirements for managing OS X devices
There are a few requirements that need to be configured properly in order to support enrollment of OS X devices. Below is a list of the requirements that needs to be in place before you can successfully enroll an OS X device:
- Your Mobile Device Management authority must be set as Microsoft Intune
- An Apple Push Notification certificate must be added in Microsoft Intune
- Apple ID for creating the APN certificate
- Devices needs to be running OS X 10.9 or above
As you can see, the list of requirements are not that long and if you’ve used Microsoft Intune to manage iOS or Android devices previously, your Mobile Device Management authority should already be configured correctly. What you need to do though is to add an Apple Push Notification (APN) certificate. See below for a detailed walk through of this is accomplished.
Add an APN certificate to Microsoft Intune
In order to request an APN certificate, you’d need to have an Apple ID. If you don’t have one, I suggest that you visit appleid.apple.com to create an account. Once you’ce signed up for an Apple ID account (or if you already have one), you can go ahead and follow the steps below:
1. Login to manage.microsoft.com with an Global Administrator account.
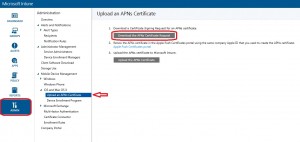
2. Go to the Admin workspace, expand iOS and Mac OS X, select Upload an APNs Certificate and click on Download the APNs Certificate Request.
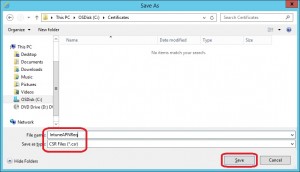
3. In the Save As dialog window, save the CSR file as e.g. IntuneAPNReq.csr in e.g. C:\Certificates and click Save.
4. Click on the Apple Push Certificates portal link in step 2.

5. On the Apple Push Certificates Portal, sign in with your Apple ID.
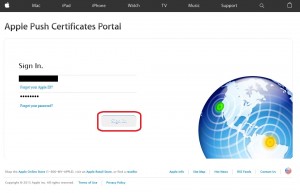
6. Click on Create a Certificate.
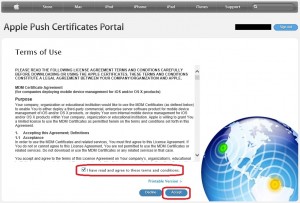
7. Accept the terms and conditions and click Accept.
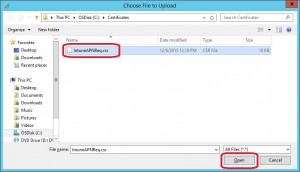
8. Click on the Browse button.

9. Select the IntuneAPNReq.csr file created earlier and click Open.
10. Click on Upload.

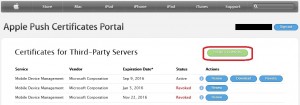
11. When you perform these steps in e.g. Internet Explorer as I’ve done in this post, you’ll be asked to run a json file. Simply just cancel that and refresh the website. You should not see your APN certificate with a status of Active. Click on Download next to your APN certificate.

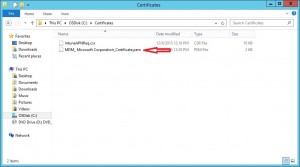
12. Select to save the MDM_Microsoft Corporation_Certificate.pem file, e.g. in C:\Certificates.
13. Back in Microsoft Intune admin workspace, click on Upload the APNs Certificate.

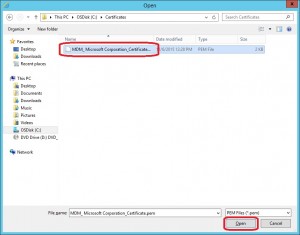
14. Click on Browse.

15. Select the MDM_Microsoft Corporation_Certification.pem file from C:\Certificates and click Open.
16. Enter your Apple ID in the form of your email address used for your account and click Upload.

17. One the APN certificate has been uploaded, you should see that iOS and Mac OS X Mobile Device Management Setup is Ready for enrollment.

Enrolling an OS X device
As when you’re enrolling iOS or Android devices, the first thing you would do is to download the Company Portal app from the respective app stores, login with your credentials and follow the enrollment process. For OS X devices, the process is similar, although there’s no application that needs to be installed. Let’s go ahead and enroll an OS X device into Microsoft Intune.
Note! During this enrollment process, a management profile will be installed on the OS X device that requires elevation.
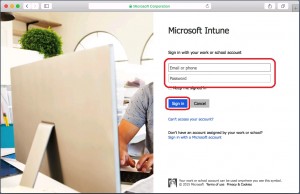
1. Open Safari and browse to portal.manage.microsoft.com.
2. Enter your credentials and click Sign in.
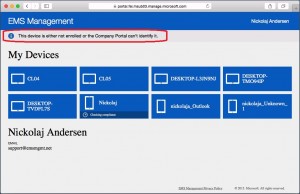
3. Once you’ve been signed in successfully, you’ll see your previously enrolled devices for the user that you signed in with in addition to some company portal information.
4. Click on the notification bar to start the enrollment process.
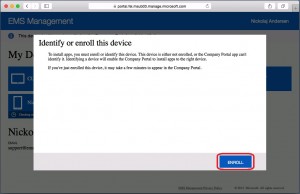
5. Click on Enroll.
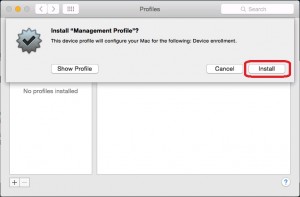
6. When enrolling iOS devices for instance, you have to install a management profile. The same is required for OS X devices. Click Install.
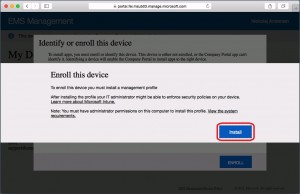
7. The management profile will now be downloaded and you’ll get a window asking if you want to install the profile, click Install again. In order to be able to install this profile, you need to be an administrator, as mentioned earlier. Enter your local user password when prompted and click OK.
8. The management profile is now being installed.

9. Click to Continue.

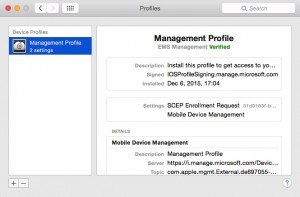
10. Click Install again.

11. Once the management has been successfully installed, the Profiles window will appear showing the management profile. It’s not really that transparent to the end user, but the enrollment process has now completed. Close the Profile window and refresh the website in Safari.
12. We can now see the OS X device listed under My Devices, meaning that it’s enrolled in Microsoft Intune.

What’s next
With the capabilities Microsoft Intune to now also manage OS X devices, it’s clear that Microsoft is investing heavily in their MDM platform making it able to manage all types of devices in an enterprise. Once the OS X device is enrolled, here’s a list of what you can do from this point on:
- Control device settings with a general configuration policy:
Mac OS X configuration policy settings in Microsoft Intune - Deploy Mac OS X settings you created with the Apple Configurator:
Mac OS X custom policy settings in Microsoft Intune - Collect hardware and software inventory from Mac OS X devices:
Understand your devices with inventory in Microsoft Intune - Run new reports that display details about the Mac OS X devices you manage:
Understand Microsoft Intune operations by using reports
If you have any question, write a comment or send me an email.









Hi Nickolaj, Thank you for the nice post. I have my Mac OS Sierra 10.15.5 enrolled in Intune, and now I want to collect software inventory.
However, the Refresh Inventory remote task in the Intune admin portal is unavailable. In fact all options in Remote Tasks are grayed out.
Can you please point me to some documentation for what is needed to collect software inventory from Mac OS X devices.
Thank you,
Zoltan