In this post, I will show you how to enforce usage of email apps to access Office 365 email. My testing is done with OnePlus 5, I can’t be sure if all Android model behave in the same way.
- Scenario 1: Allow use any email clients, redirect install Microsoft Intune Company Portal app, and enforce enroll device to Intune.
- Scenario 2: Allow setup any email client but block sync emails, enforce/redirect use Outlook app. When setup email in Outlook, redirect install Microsoft Intune Company Portal app, and enforce enroll device to Intune.
- Scenario 3: Allow usage of Android native email client only, redirect install Microsoft Intune Company Portal app, and enforce enroll device to Intune, block anything else.
Requirement:
- Office 365 licenses
- EMS or Intune licenses
- Android device.
- Device compliance policy configured.
Scenario 1: Allow use any email clients, enforce enroll device to Intune.
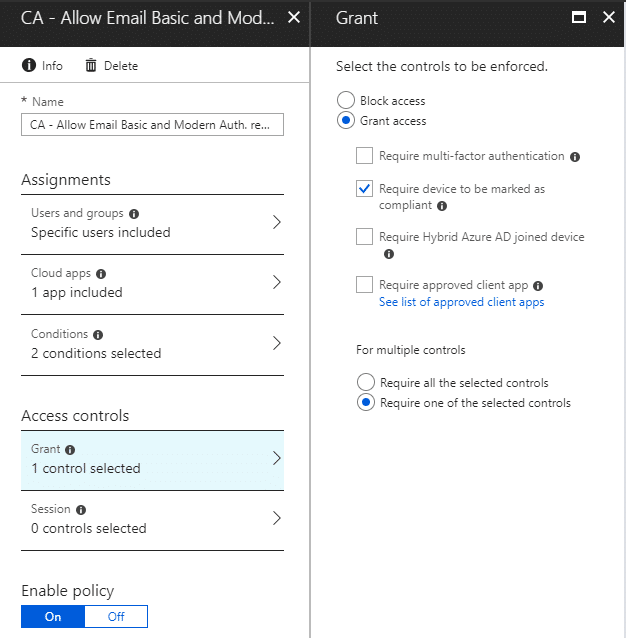
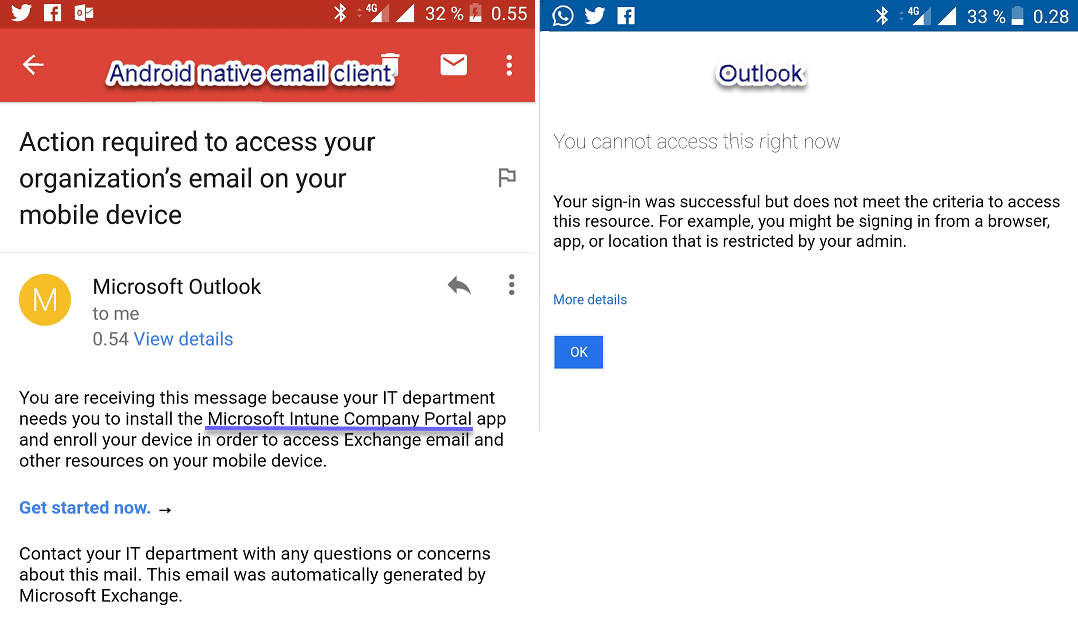
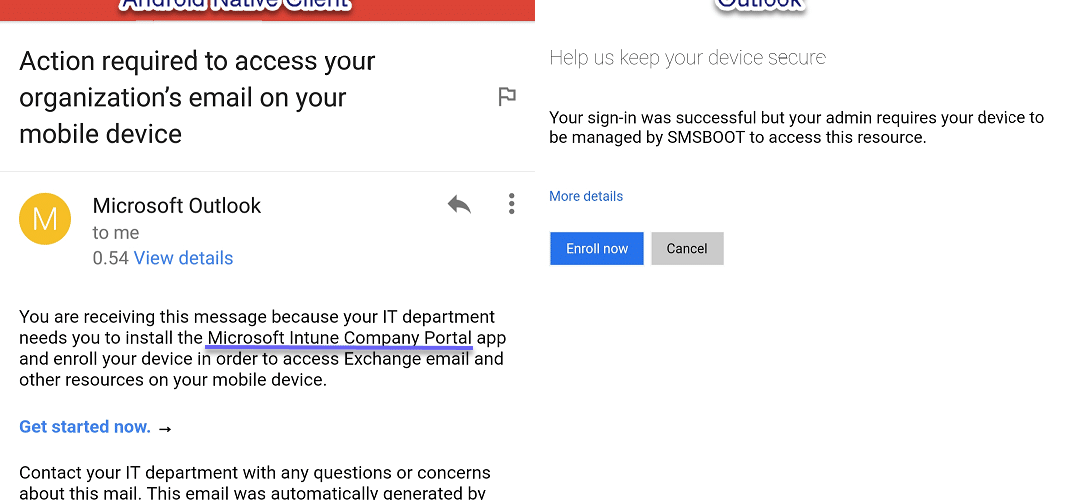
In this scenario, users can setup any email clients to access Office 365 email. User will receive an email redirecting them to download Microsoft Intune Company Portal, then guide them to enroll the device to Intune.
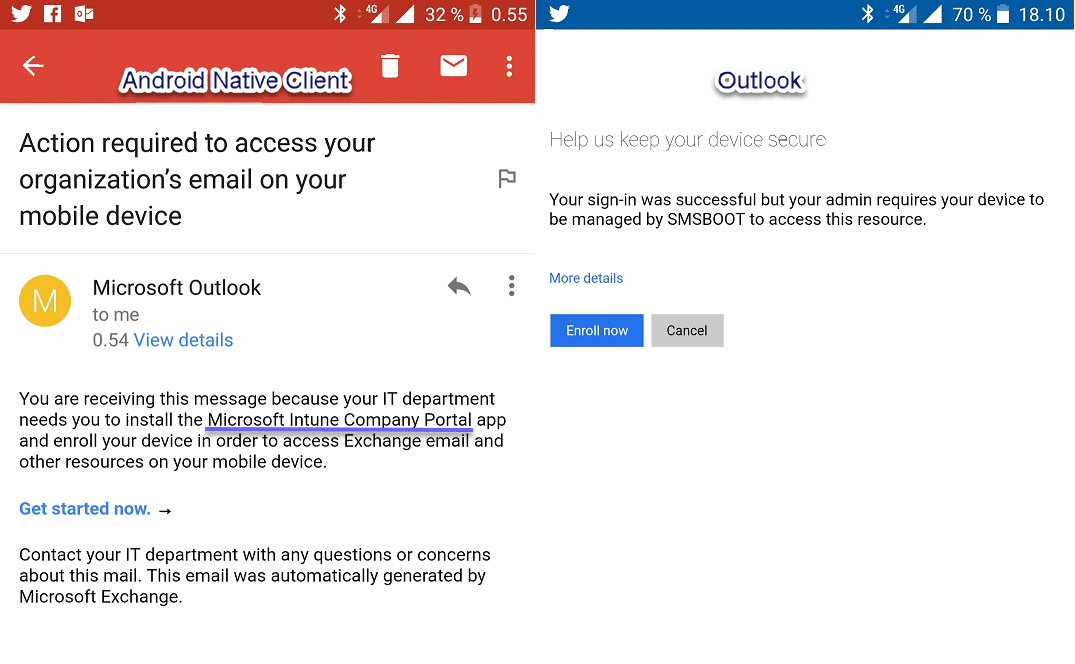
This conditional policy will require the device to be marked as compliant. When the device is not enrolled to Intune (device is not compliant), Intune Conditional Access leverages Exchange ActiveSync to quarantine these legacy clients and sends an email into their inbox indicating that the they need to install Microsoft Intune Company Portal app and enroll their device in order to access Exchange mail and other resources.
- Go to Azure Portal : https://portal.azure.com/
- Go to Intune and create new Conditional Access Policy
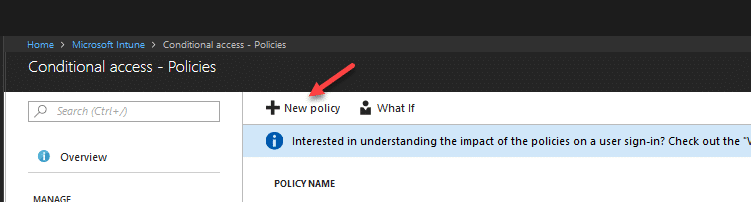
- Fill information as bellow:
Name: CA – Allow Email Basic and Modern Auth. requried enrolled (Android)
Assignments – Users and groups: choose user groups that you wish to assign this policy
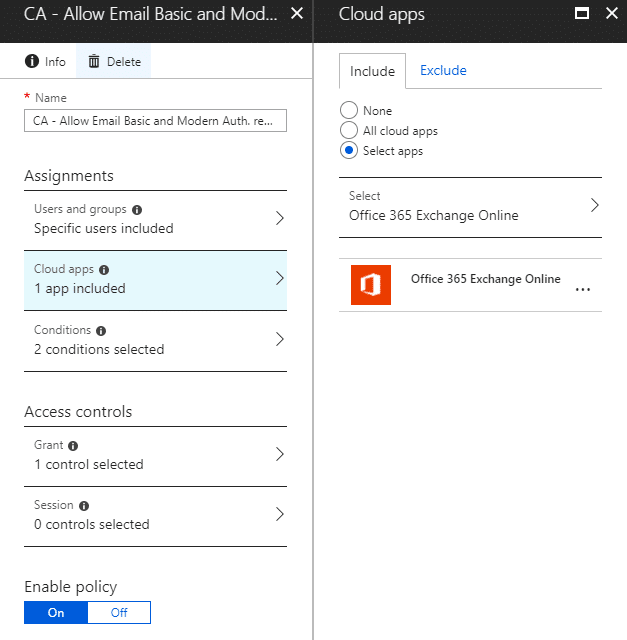
Assignments – Cloud apps: Select apps – Office 365 Exchange Online
Assignments – Conditions: Client apps (preview) – Modern authentication clients, Exchange ActiveSync clients, other clients
Access controls – Grant: Grant access – Required device to be marked as compliant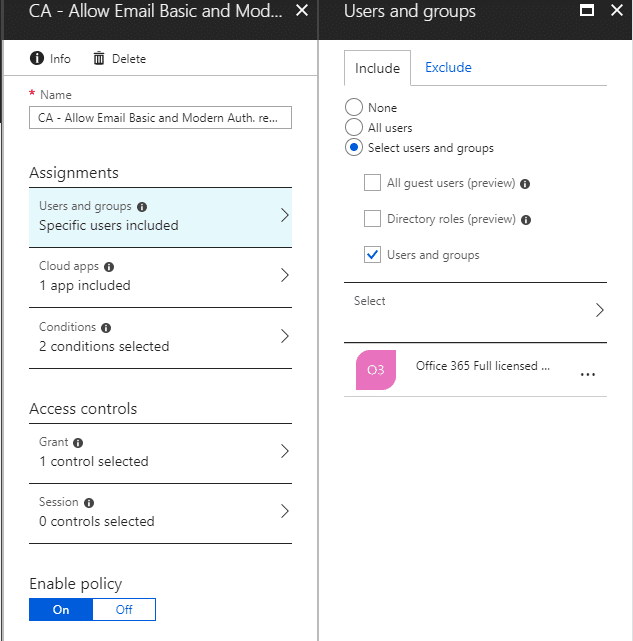
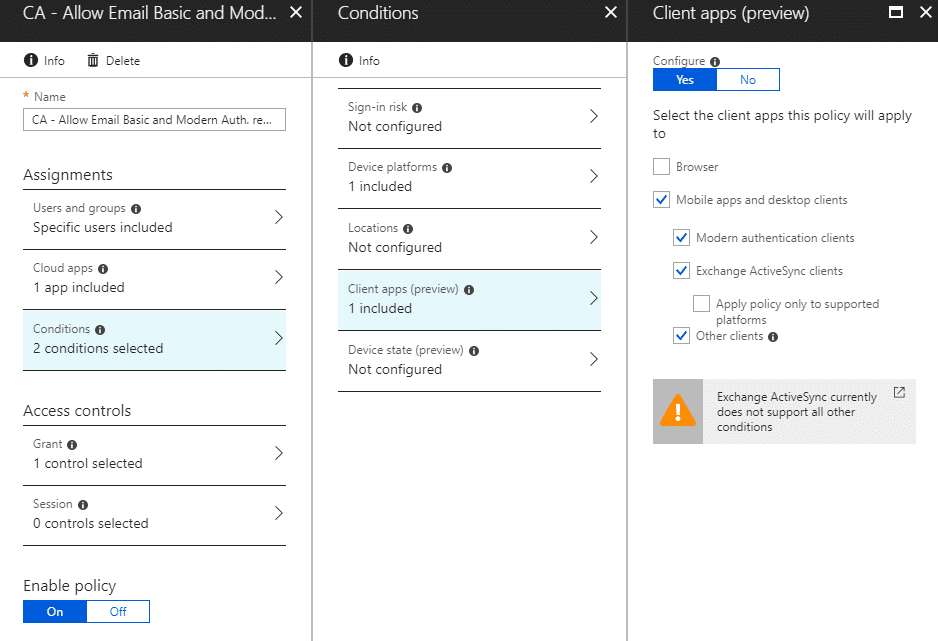
-
Enable policy
Scenario 2: Allow setup email but block sync emails, enforce/redirect use Outlook, enforce enroll device to Intune.
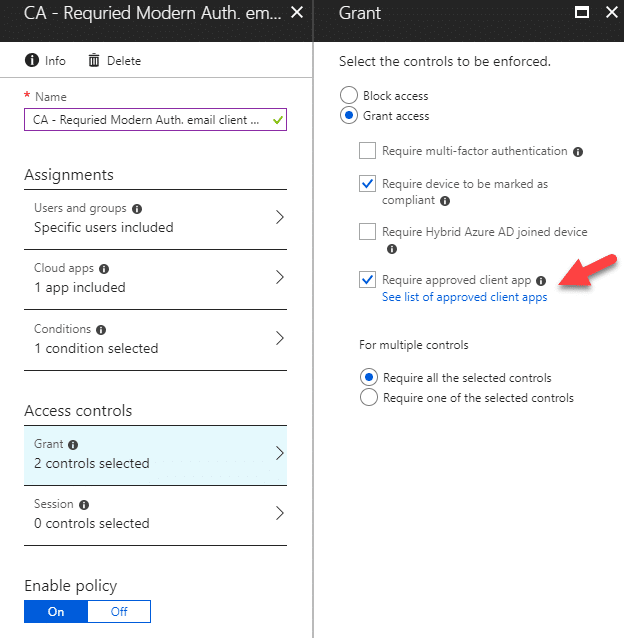
In this scenario, users can allow setup Android native email client for Office 365 email. The user will receive an email and will be redirected to download Outlook. When the user setup Outlook, it will enforce the download of the Microsoft Intune Company portal app and guide the user to enroll the device to Intune. The user will not be able to use Android native email client to sync Office 365 emails.
This conditional access policy will require the device to use an approved client app and be marked as compliant, in this case the approved email app is Outlook. If user is using other email client than outlook to access Office 365 Exchange Online, it will enforce usage of Outlook app and will not allow to sync email. Intune Conditional Access leverages Exchange ActiveSync to quarantine these unapproved clients and sends an email into their inbox indicating that the they need to install Outlook app and enroll their device to access Exchange mail and other resources.
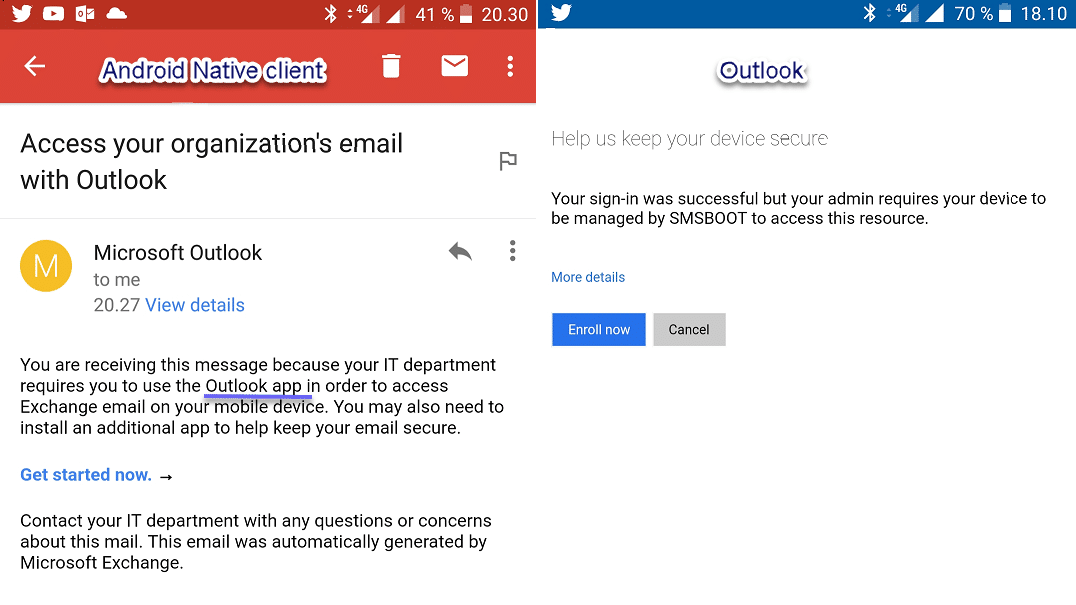
Configuration are quite similar as “Scenario 1: allow both Android native email client or Outlook”, only changes are:
Name: CA – Required Modern Auth. email client and enrolled (Android)
Access controls – Grant: Grant access – Require device to be marked as compliant
Access controls – Grant: Grant access – Require approved client app
For multiple controls: Require all the selected controls
Scenario 3: Allow usage of only Android native email client, block anything else.
In this scenario, users can setup Android native email client to access Office 365 email. User will receive an email redirecting them to download Microsoft Intune Company Portal, then guide them to enroll the device to Intune. User cannot access Office 365 email from any other method than native email client with basic authentication.
We will need to create two Conditional Access policies, one for allow Exchange ActiveSync basic authentication, another one for block modern authentication client and other clients.
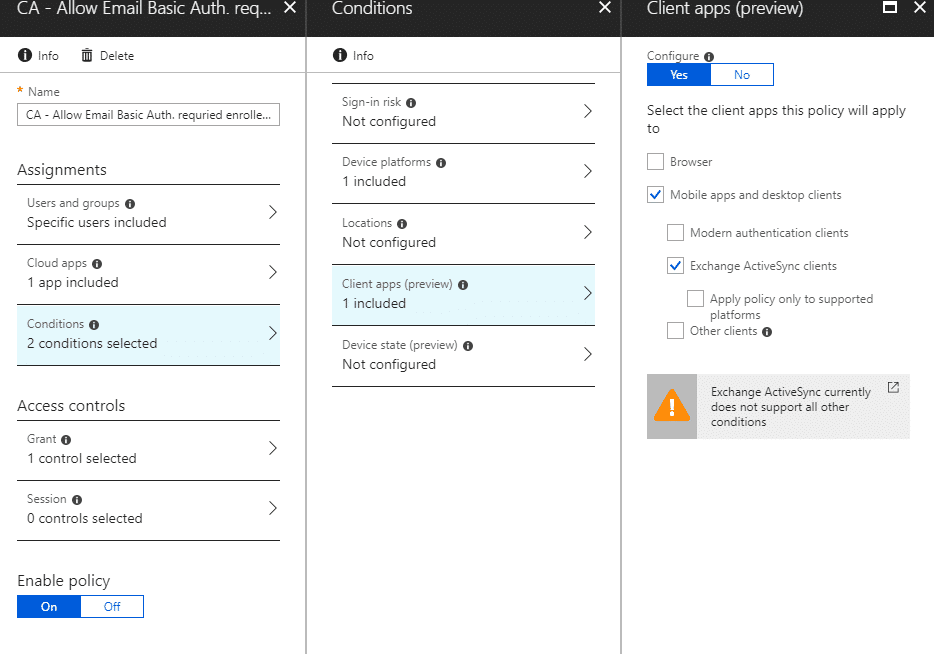
Conditional Access Policy for allow Exchange ActiveSync basic authentication
Configuration are quite similar as “Scenario 1: allow both Android native email client or Outlook”, only changes are:
Name: CA – Allow Email Basic Auth. requried enrolled (Android)
Assignments – Conditions: Client apps (preview) – Exchange ActiveSync clients
Access controls – Grant: Grant access – Require device to be marked as compliant
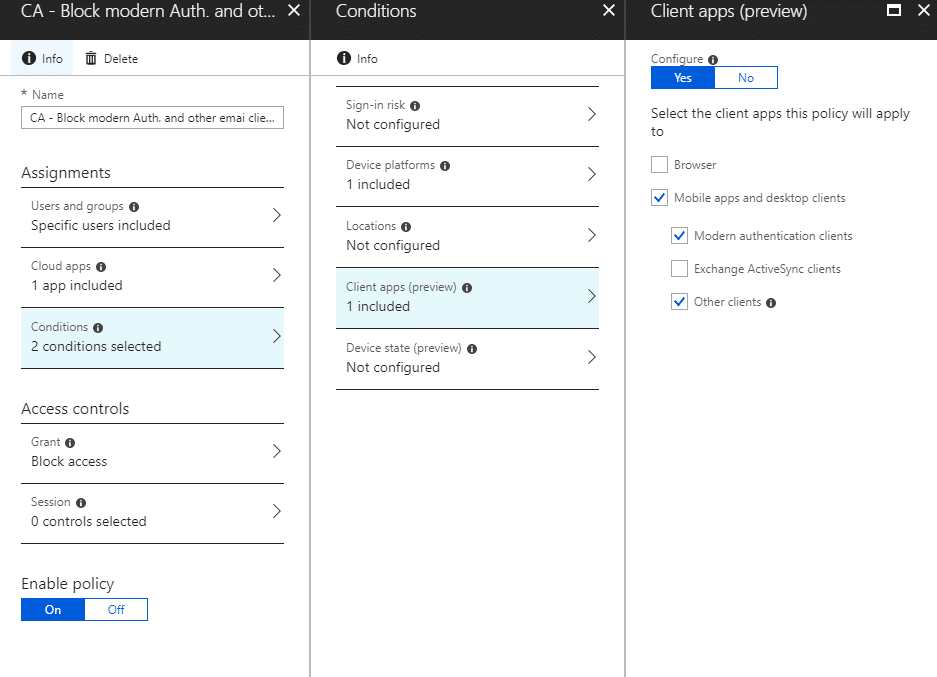
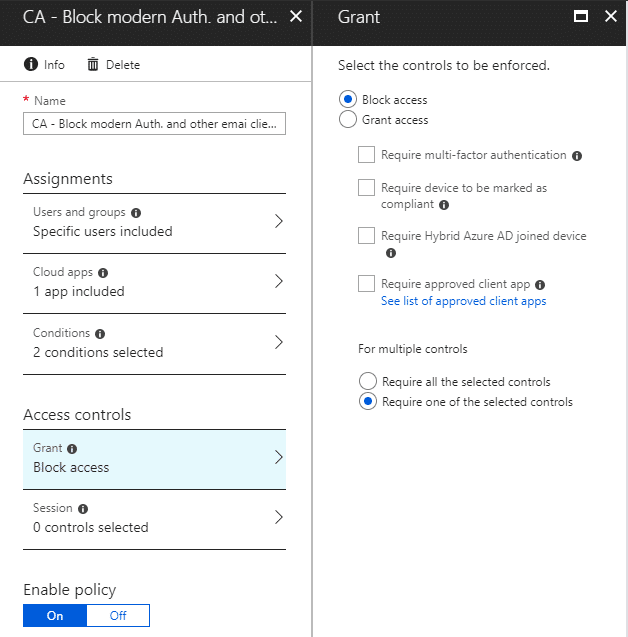
Conditional Access Policy for block modern authentication clients and other clients
Configuration are quite similar as “Scenario 1: allow both Android native email client or Outlook”, only changes are:
Name: CA – Block modern Auth. and other emai clients (Android)
Assignments – Conditions: Client apps (preview) – Modern authentication clients, Other clients
Access controls – Grant: Block access
NOTES:
If you have already setup your native email client before you created the Exchange ActiveSync basic authentication Conditional Access policy, you might have to wait 5-6 hours for those settings to apply. At the moment when I was writing this, I couldn’t find a working solution for this matter.








so nice share, i was unexpected
So nice share, i can try this now to acces email from Android with Microsoft Intune.thnks
nice article
Thankyou for sharing this article
thanks for sharing bro
work on 2020?
Thanks For sharing
Any news on why scenerio 1 does not work on Android Enterprise? This was also working for me some time ago but now I have the same problems as other’s here.
Last time I have been told that the issue is fixed. I haven’t test it for quit sometime. But I personally wouldn’t like allow user use any email client for enterprise, because IT end up support multiple email clients for end users. I would choose scenario 2, enforce them use only outlook, and block legacy.
Since a couple of weeks i had some issues in SCENARIO 1: ALLOW USE ANY EMAIL CLIENTS. Outlook app works good. But if i want to use an android app GMAIL (android for work app) i got the message: “Action required to access your organization’s email on your mobile.” Is there any workaround how i can still use the app GMAIL in the Android for Work? Or is there any changes in GMAIL / Intune ?
Hello Emotino, sorry for the delay. I have been testing this, and seems it’s no longer work in Scenario 1 when using Android Enterprise. It still works if not use Android Enterprise. I don’t what has changed, last time when I tested, it was still working. I have tested this now many times, reset my phone, enrolled to Intune using company portal, work profile created (Android Enterprise), apps installed and the device is complaint. Once when configured conditional access to allow Exchange ActivceSync client policy, Gmail client cannot connect to Office 365. If I disable the CA policy, Gmail client configured Office 365 succeed. I just open a support case for this (case ID 118091819036088).
Thank you for testing this! I test the scenerio 1 again. The scenerio 1 still not working.
Do you already have some respone of your case id 118091819036088?
Hello, I still have that case opened. Supports managed repro the same issue. I need to do more test again and reply them after my holidays. 🙂
Regards, Sandy
Do you already have a workaround for scenerio 1?
Hi,
i am facing the same issue with Gmail Cclient and CA policy. Gmail shows that the device is unregistred but it isn’t.
Did you ever get an answer from support to this issue?
Kind regards
Marco
Yes, the support case is solved long time ago, they said they have identified the issue and it’s fixed. I haven’t test this for quite some time since then.
Hi Zeng, I am trying to achieve scenario #2. I have configured scenario #1, which appears to be a prerequisite for scenario #2
Exchange ActiveSync Basic Auth
Exchange Online Modern Auth (Android)
The message that I get is as follows,
“You are receiving this message because your IT department has blocked your email access. This could be due to temporary conditions, like your network location.
Contact your IT department with any questions or concerns about this mail. This email was automatically generated by Microsoft Exchange.”
Hello, I updated my post since there are new features came not long time ago. I test all my scenarios, they all still works. Will you read it again and make sure not any other CA policy blocking it? Please let me know the result. If still not working for you, please let me know, I will contact you then via email. Thanks.
Bingo! It is now working as per your post. You were correct, there was another policy impacting the expected results. I had a CA policy that was set on my test account that would (should) prevent access from certain regions. Not sure why this CA was impacting your scenarios. I will have to revisit that CA in greater details.
In any event, thank you very much for your help in this regard. 🙂
Hi Zeng, are you referring to another post “Require device to be marked as compliant”? If so, I am not able to find it on this site.
I did not have a Device Compliance policy configured for Android device. However, after creating one and only requiring that the device not is rooted, I am still faced with the same message.
Can you tell What conditional access settings do you have now and what scenario are you trying to do? What exactly message did you get about email is blocked? From Android gmail client or outlook or other email client?
Though this appears to work on my android phone, I do not get the same verbiage in the dialogs in this article. In fact, it outright tells me that email is blocked. There is nothing saying that I have to install the Microsoft Company Portal app or any link redirected to it. Nor does it redirect me to the Outlook app or link to it.
Is there a setting that I am missing elsewhere in Azure/Intune to get the verbiage and redirect to show?
Can you tell What configuration do you have now? The setting I mentioned in post “Require device to be marked as compliant”, that requires have “Device compliance” settings configured. I will update my post about that.
So in essence, using Native client is EAS, and using Outlook App is Mondern Authentication.
ActiveSync policy works on all devices, as it only looks for the EAS protocol not device., this is what i use for require IOS devices to be registered when in ActiveSync mode.
Thomas,
It still doesn’t work on my iPhone. I can still access the corporate mail without any problems. On Android, it works as expected.
Thanks for this breakdown of all conditional access possibilities! The scenario’s are very clear and representative for customers. Maybe also throw in some mfa 🙂
Does scenario 1 also work for ios native mail cliënt of does it not USD basic auth?
Thanks, sure give some love for MFA. 🙂
Sorry, I can’t say for sure how it works on iOS, didn’t test it, it’s possible it works as well.
I tested the Exchange active sync basic auth rule from scenario 1 on an iOS device. I regret to say that it doesn’t work. I can still access my corporate email on a non-enrolled iPhone. On my Android device, it works as expected. :-/
Thank you for testing it on iOS device and sharing the result Peter!
Ye its weird, i have a client i tested with Outlook before, and it worked like a charm, but now i tested with ActiveSync and you are absolutly right, it doesnt work. But there are no settings that define device in Scenario 1, so why doesnt it affect IOS?
6 Hours later, i got the email in the EAS client that i need to register with Intune to get access on the IOS Device, with no change to scenario 1 configuration, Peter can you confirm that it works with you?
I also configured the second rule of scenario 1.
On Android, it works as expected.
On iOS, on my unenrolled device, I couldn’t access the corporate mail with the native app anymore. I got the message I needed to enroll. So I did. After that, I installed Outlook and was able to read the corporate mail. But I still can’t use the native mail app to read the corporate mail.
Peter, then you must have something wrong elsewhere.. Maybe a compliance policy, or a intune App policy somewhere.
I have no problems getting the mail on both the native mail client and Outlook app, once i registered the phone.