Creating a WiFi profile in ConfigMgr is not really a new feature, but now that ConfigMgr is starting to get a better integration with Microsoft Intune, management of mobile devices becomes more important that before. In the latest service pack that was released for ConfigMgr 2012 R2, a bunch of new features for managing and supporting mobile devices was introduced. You can read more about them at the link below:
https://technet.microsoft.com/en-us/library/mt131422.aspx#BKMK_cmintune
So why would you deploy a WiFi profile to your mobile devices? There could be many reason for doing so, one of them for instance is if you’re whole company are going off site for e.g. a conference. The conference center has a WiFi network that you want to want the user to automatically connect to when they are in range. This is a great example where the ConfigMgr administrator can pre-deploy the WiFi profile to the mobile devices, and once the users get near the WiFi network, they’re automatically prompted for entering the password.
Another example would be to distribute a WiFi profile for the users to connect to a company WiFi network with a WPA2 Enterprise encryption, using a certificate. That would let the users automatically connect to the company WiFi network automatically once they’ve enrolled into Intune (or Intune integrated with ConfigMgr, acting as the MDM athority).
In this blog post I’ll demonstrate how you can create and deploy a WiFi profile for iOS devices (the same process applies for iOS devices) for a WiFi network setup with WPA2 Personal with a preshared key (simply because I don’t have a WiFi AP setup in my lab environment with WPA2-Enterprise, that might come in another post). Unfortunately ConfigMgr 2012 R2 SP1 integrated with Intune doesn’t support to specify the preshared key at this moment. It’s possible to create a WiFi profile for Android as well with the same configuration as mentioned above, but in my lab environment I ran into issues when the WiFi profile was deployed to my Android 5.x device. It appears from what I can understand, that the Android platform doesn’t support deploying a WPA2-Personal WiFi profile as of right now. The documentation below confirms that as well of my test in my lab:
https://technet.microsoft.com/en-us/library/dn818903.aspx
Create a WiFi profile for Mobile Devices
As already mentioned, I’ll create a WiFi profile using WPA2-Personal encryption for the iOS platform.
1. Open the ConfigMgr console and go to the Asset and Compliance node.
2. Expand Comliance Settings, and then expand Company Resource Access.
3. Right click on Wi-Fi Profiles and select Create Wi-Fi Profile.

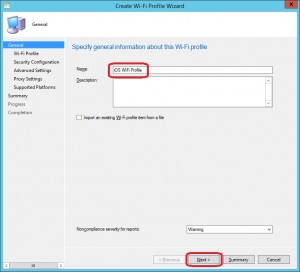
4. On the General page, give the profile a name, e.g. iOS WiFi Profile and click Next.
5. On the WiFi Profile page, configure the following:
Network name: <name of your network>
SSID: <SSID>
Connect automatically when this network is in range: Checked
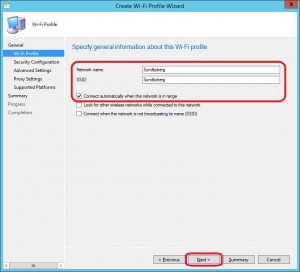
It’s important that the Network name and SSID should configured with the same name, e.g. Sundbyberg and Sundbyberg as in the picture above. They’re also case-sensitive, so you need to take that into account when configuring your profile. Click Next.
6. On the Security Configuration page, configure the following:
Security type: WPA2 – Personal
Encryption: AES
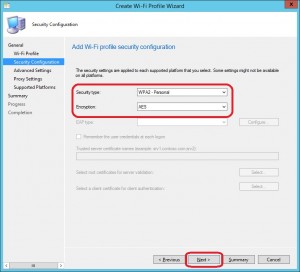
Click Next.
7. On the Advanced Settings and Proxy Settings pages, click Next leaving the default configuration.
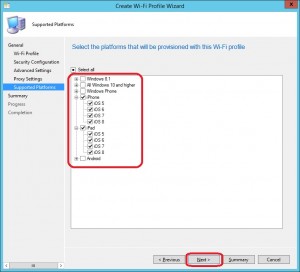
8. On the Supported Platforms page, put a check mark in iPhone and iPad check boxes and click Next.
9. On the Summary page, click Next.
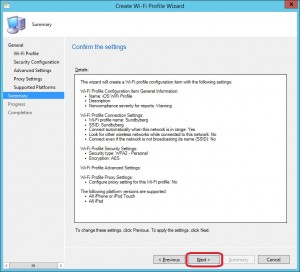
10. On the Completion page, click Close.
Deploy a WiFi Profile to a collection with Mobile Devices
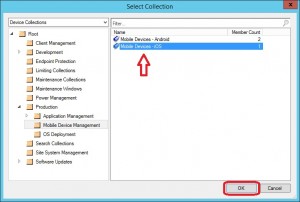
You’re able to deploy the WiFi profile to either User Collections or Device Collections. Whether you’re going to target all of your managed devices, to ensure complete coverage with the deployment, or just for a bunch of users in a specific department, it doesn’t matter, both types of collections works fine. In this demonstration I’ve created a collection called Mobile Devices – iOS containing all of my iOS devices, that I will as target for the deployment.
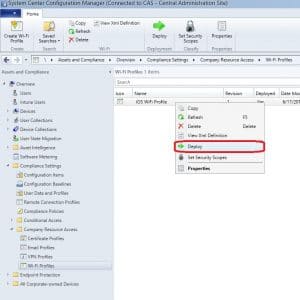
1. Go to Assets and Compliance, expand Compliance Settings and then Company Resource Access. Select Wi-Fi Profiles and right click on the iOS WiFi Profile that we previously created. Select Deploy.
2. Click on Browse.

3. Select either a User Collection or Device Collection. As seen in the picture below, I’ve chosen a Device Collection called Mobile Devices – iOS. Click OK.
4. Specify a schedule for the WiFi profile to be evaluated for compliance. Keep in mind that the compliance evaluation is running on the mobile device, so you’d probably not set it to evaluate every 5 minute or so. Running the evaluation every day or so should be sufficient in most cases. If you’d want to create an in-console alert when the compliance falls below a certain threshold, configure that as well by enabling Generate an alert, and configure the threshold in percentage. Click OK.

Verify Compliance of a WiFi Profile
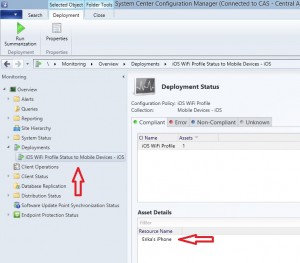
As with any other deployments, the details can be found under Monitoring – Deployments. Below is a screenshot of my deployment for the iOS WiFi Profile:









Add comment