At one of my customers we’ve recently implemented Role Based Administration in ConfigMgr 2012 R2, which is great because they can now start to leverage the many great things that comes with it. One of them is to begin dividing the different teams into Security Roles, and while doing so, we needed to create a custom Security Role for a team that would mainly focus on OSD. In this post I’ll walk you through the necessary steps you need to take in order to create a Security Role called OSD Manager, that has permissions to perform common tasks involved when working with OSD in ConfigMgr 2012.
In my lab environment, I want users that gets associated with the OSD Manager Security Role to be able to do the following:
- Create and Deploy Task Sequences
- Create and import Drivers
- Create Driver Packages
- Read Applications and Packages to be able to use them in a Task Sequence
- Import Operating System Images and Operating System Installation Packages
- Distribute content to Distribution Points and Distribution Point Groups
- Give Read permissions to collections
I also want to only allow the users to only be able to work with a specific set of Collections.
Create OSD Manager Security Role
We begin with creating a new Security Role, where we’ll set the permissions that every Administrative User that get’s associated with this Security Role will be given. The easiest way is to go about this is to copy the Security Role with least privileges, so we don’t have to click like a maniac. One of these built-in Security Roles are the Remote Tools Operator role. One thing to note here is that these permissions that are outlined in this blog post, only reflect a certain custom Security Role. It’s not written in stone that this is the only way to go about handling permissions. One company may not require OSD Managers to be able to create Device Drivers, or perhaps they need the users to be able to create Packages also, instead of only giving them Read permissions as in the example below.
In order to perform all of the tasks mentioned above, first we need to create the Security Role and specify the required permissions:
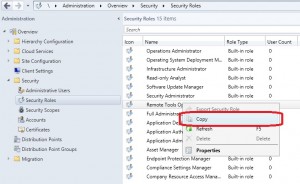
1. Open the ConfigMgr console and go to Administration – Security – Security Roles.
2. Right-click on the Remote Tools Operator and select Copy.
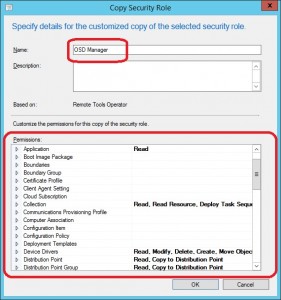
3. In the Name field, enter OSD Manager.
4. Edit the permissions to reflect the following:
- Application
- Read: Yes
- Collection
- Deploy Task Sequence: Yes
- Read: Yes
- Read Resource: Yes
- Device Drivers
- Create: Yes
- Delete: Yes
- Modify: Yes
- Modify Folder: Yes
- Move Object: Yes
- Read: Yes
- Run Report: Yes
- Distribution Point
- Copy to Distribution Point: Yes
- Read: Yes
- Distribution Point Group
- Copy to Distribution Point Group: Yes
- Read: Yes
- Driver Package
- Create: Yes
- Delete: Yes
- Modify: Yes
- Modify Folder: Yes
- Move Object: Yes
- Read: Yes
- Operating System Image
- Create: Yes
- Delete: Yes
- Modify: Yes
- Move Folder: Yes
- Move Object: Yes
- Read: Yes
- Operating System Installation Package
- Create: Yes
- Delete: Yes
- Modify: Yes
- Move Folder: Yes
- Move Object: Yes
- Read: Yes
- Package
- Read: Yes
- Task Sequence Package
- Create: Yes
- Create Task Sequence Media: Yes
- Delete: Yes
- Modify: Yes
- Modify Folder: Yes
- Move Object: Yes
- Read: Yes
- Run Report: Yes
5. Once you’ve configured all of the above permissions, click OK.
Add an Administrative User
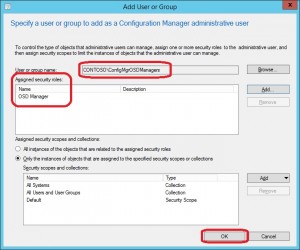
The next step is to associate the newly created Security Role with either an user or a group. I recommend that you create an Active Directory group called e.g. ConfigMgrOSDManagers (that’s what I have in my lab environment, anything else will of course work as well).
1. Go to Administration – Security – Administrative Users.
2. Right click on Administrative Users and select Add User or Group.

3. Click on Browse next to User or group name and locate the group you want to add (in this case I’m going to add a group called ConfigMgrOSDManagers as mentioned earlier).
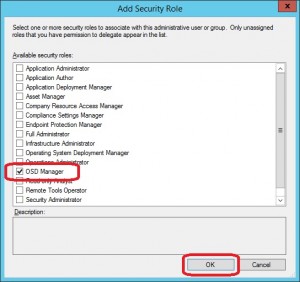
4. Click on Add next to Assigned security roles, select the OSD Manager Security Role and click OK.
5. At this point, I’ll not configure the part where we assign objects and instances for Collections and Security Scope. by not doing this, I’m granting the group access to all ConfigMgr objects and collections that have the Default Security Scope assigned to it. You could of course do this right away if you know what Collections the group needs to work with, but for demonstration purposes, I’ll do that in another step.
6. Click OK.
Assigning Collections to an Administrative User
Now that we’ve created the Security Role, added an Administrative User and assigned it the correct OSD Manager Security Role, we want to limit the Collections that the group of users can work with. For example, we only want the users to be able to deploy a new created Task Sequence to a specific set of Collections.
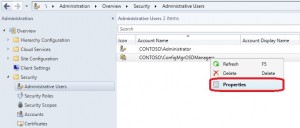
1. Go to Administration – Security – Administrative Users.
2. Right click on the user or group that you choose in the previous step when we added a group (in this case CONTOSO\ConfigMgrOSDManagers) and select Properties.
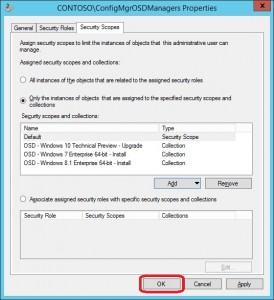
3. Go to the Security Scopes tab, select the All Systems collection under Security scopes and collection and click Remove.
4. Perform the same removal steps for the collection called All Users and User Groups.
5. Click Add and select Collection.
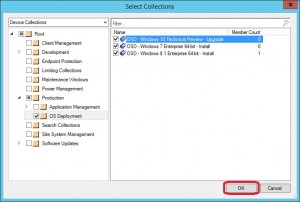
6. Select Device Collection in the top left drop down menu and make the desired selections of Collections. In my case I have 3 collections associated with OSD that I want to add, they are:
- OSD – Windows 7 Enterprise 64-bit – Install
- OSD – Windows 8.1 Enterprise 64-bit – Install
- OSD – Windows 10 Technical Preview – Upgrade
When you’ve selected the Collections you want, click OK.
7. When ready, click OK in the Properties window.
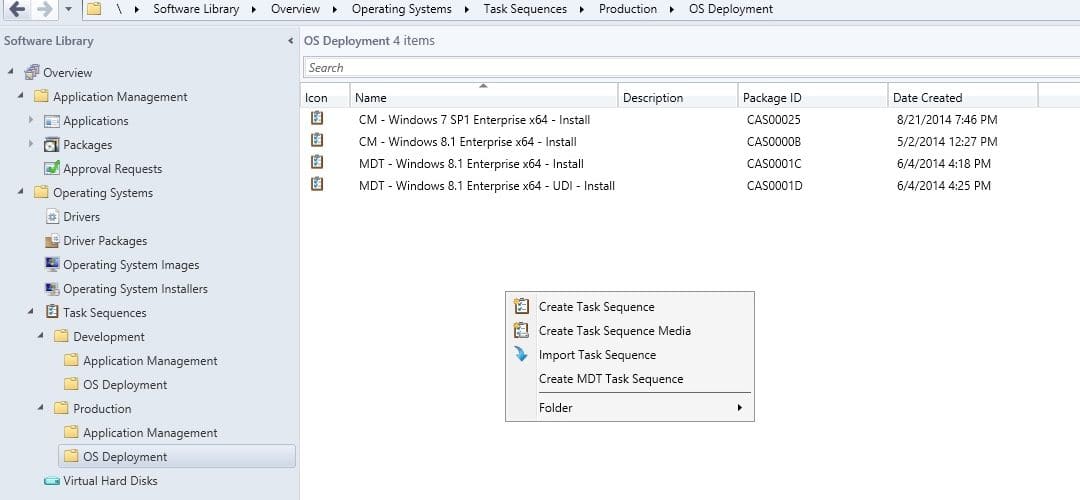
We’ve now successfully taken all the necessary steps in order to start giving those OSD Managers something to work with. One of those users are James Andersson in my environment. If we launch the ConfigMgr console with his credentials, we should now get a much more restricted console experience. Here’s a screenshot from the Software Library node:









This article is very helpful. Thanks!